We're migrating to the Cisco Community on March 29. The Meraki Community will enter read-only mode starting on March 26.
Learn more- Technical Forums
- :
- Security & SD-WAN
- :
- Help with MX Firewall Rule
Help with MX Firewall Rule
Solved- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Help with MX Firewall Rule
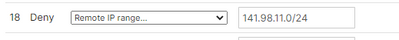
Can anyone tell me why this Layer 7 rule:
Doesn't block this IP Address:
141.98.11.14
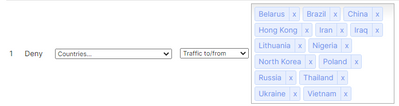
The above IP address also appears to be from Lithuania, and I've added Lithuania to the blocked country list, yet it is still able to access my network.
Thanks,
Ian
Solved! Go to solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I figured this out. I appreciate your responses. The appliance in question uses Group Policies and I was using the firewall settings page and not controlling the firewall on the particular group policy.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Your rule blocks the destination of 141.98.11.0/24 from inside traffic heading out through your MX
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks. Is there a way to block incoming IPv4 traffic?
Any idea why the Deny countries rule isn't blocking traffic from Lithuania?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
MX blocks all inbound traffic by default. What specifically are you seeing happen in your network?
I tested and while I couldn't ping 141.98.11.14 .13 did respond to ping. So, I tried both a L7 rule denying the entire /24 and also tested blocking Lithuania. In both cases pings no longer went through. So, it appears to be doing its job in my test.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
We're seeing a continuous trickle of authentication attempts on our Exchange server. It's nothing major, about 20 attempts / hour, but since the HAFNIUM attacks last March, I'm trying to monitor and be more proactive against potential threats.
We have a 1:1 NAT to our exchange server allowing TCP ports 25, 443 & 587.
Additionally, we have a 1:1 NAT to a VPN server allowing TCP 443 & UDP 500/4500.
Soon after I enabled the Deny countries rule about a year ago, it prevented us from receiving email from the countries listed, but perhaps it also only blocks outbound traffic even though the rule uses the terminology "To/From"?
Thanks again for you help.
Ian
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
We're seeing a consistent trickle of failed authentication attempts on our Exchange server. It's nothing major, around 20 / hour, but since the HAFNIUM attacks last march, I'm trying to be more proactive about monitoring and blocking unwanted access attempts.
We've got a 1:1 NAT to our Exchange server allowing TCP ports 25, 443 & 587. We've also got a 1:1 NAT to our VPN server allowing TCP 443 & UDP 500/4500.
I'm pretty sure the Deny countries rule has blocked email from countries listed in the past. Does it only block outgoing traffic? The rule language says To/From, so I assumed it blocked incoming traffic as well as outgoing.
Thanks again for your help,
Ian
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I've responded to you twice and my messages aren't getting posted for some reason.
I'll try again.
I'm seeing a consistent trickle of failed authentication attempts on our Exchange server. It's nothing major, around 20 / hour, but after the HAFNIUM attacks last March, I'm trying to be more proactive about blocking these IP addresses.
We're got a 1:1 NAT allowing TCP ports 25, 443 & 587 to our exchange server. We've also got a 1:1 NAT allowing TCP 443 & UDP 500/4500 to our VPN server.
I tried your ping test from our exchange server and despite having rules denying traffic to 141.98.11.0/24, Lithuania & explicitly blocking 141.98.11.13, the ping is still successful.
We're on version MX 17.6, if that makes a difference.
Edit: We have 5 MX Appliances. 2 with 1:1 NAT and 3 with no NAT forwarding rules. The only appliance that the Layer 7 firewall rules do not work as expected is the one I originally posted about.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sorry about our over-zealous spam filter, @IanMcNamara! I’ve released your messages (though that’s probably not that helpful at this point)
Cheers!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I figured this out. I appreciate your responses. The appliance in question uses Group Policies and I was using the firewall settings page and not controlling the firewall on the particular group policy.
-
3rd Party VPN
174 -
ACLs
91 -
Auto VPN
306 -
AWS
36 -
Azure
70 -
Client VPN
382 -
Firewall
867 -
iOS
1 -
Other
557 -
Wireless LAN MR
1