- Technical Forums
- :
- Security & SD-WAN
- :
- Firmware Update Now dozens of IDS whitelist items?
Firmware Update Now dozens of IDS whitelist items?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Firmware Update Now dozens of IDS whitelist items?
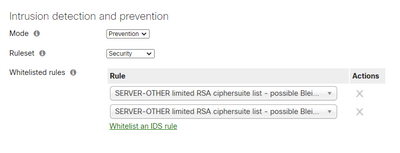
Just updated MX250 to newest firmware last night. Now I have at least 20 items listed under IDS whitelist rules? I have nothing whitelisted, and have no idea how Meraki can just arbitrarily add whitelist rules? There are 2 entries, with at least 10 items listed under each entry. Some to me have absolutely no reason to be whitelisted. Many are SQL related. My first reaction is to remove them all, but I never like to perform knee jerk reactions to things I have little information about. Anyone else see these same types of behavior after the last firmware MX250 firmware upgrade? Some entries are liosted as Malware Backdoor? Why would Meraki whitelist these types of things?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
That sounds pretty odd. Did you check your change log to make sure someone else didn't edit the whitelist?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I thought very odd as well. Change log empty after firmware update. I am a little worried as I have several Malware Backdoor entries now set as whitelisted. I have 2 entries under IDS, with each entry having over a dozen now whitelisted items. I went back pretty far in my change log just to make sure it was not something I missed weeks ago but see nothing. At this point I am going to delete these entries, but I still would love to know how they were entered, and by whom. Here is just a very small screen shot of just a couple of the entries. Are these just the rules Meraki generates, and are now just made visible? I have 2 rules listed, both have different entries. Again, maybe this is just the default Meraki rule-sets. I just never have noticed them visually listed before under intrusion detection. If it is a Meraki default whitelist, I can hardly believe they would have malware-backdoor whitelisted......lol.
Thank you for your response, I
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The firmware update would not have added them.
Take a screenshot, and remove them.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hold on - your screenshot only shows two rules whitelisted, neither of them SQL related.
All the others are signatures that have fired in your organisation that you can add - but are not added.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I just counted, under each "rule" there are almost 40 individual items, I just took a quick screen shot to give everyone an idea of what was there. But they vary greatly.
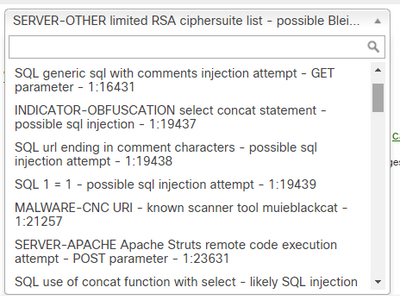
So are you saying all the things in these lists are not really in effect, they are just things that have been tripped?
Very confusing to say the least if this is the case.
So if I just click on one of the items in these "lists" that will then whitelist that particular item?
Again just confusing I have 2 items under "Rule", with 40 sub items under each one of them.
When I click "whitelist an IDS rule" I get another "Rule" with 40 or so different sub items. Even when I click one of the sub items, nothing happens. I do not see that particular item listed, or added anywhere.
What am I missing?..This is what the doc says:
You can whitelist specific SNORT® signatures by clicking Whitelist an IDS rule. Any signatures for which matching traffic has been seen by the appliance will appear in the Select an Option drop-down so that you can select which signature or signatures you wish to whitelist.
So why do I have 2 "Rules"? maximum number of signatures in a rule? When I do click an item to whitelist I do not see it listed anywhere as being whitelisted? If I do delete both of these "rules". As the appliance starts to see attacks, will it just re-build the list again?
Sorry I just find it confusing the way it is presented.
Thank you again, really appreciate your time!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
>So are you saying all the things in these lists are not really in effect, they are just things that have been tripped?
Correct. It shows you the tripped rules so if you need to add something to the whitelist you will select the correct rule (there are so many rules that are almost identical but slightly different).
You have 2 rules because someone has added them in the past.
You also probably need to look at your environment to see why you are getting so many signatures firing, especially SQL signatures. Often an indication of something being poorly coded ... or an actual attack being blocked. More likely poor code - Occam's razor - simplest explanation is probably the right answer).
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Ty Phillip.
Very detailed answer, I really appreciate it. Only mystery, is I set this network up, and have never added any rules, so I am still a little confused as to how? I do believe these all showed up after I installed the latest firmware on Sunday night. I agree with your SQL references , and these fixes are in the works.
If I add something to be whitelisted, where does it show up? For example, I highlighted one of the D-Link signatures as a whitelist since we have no D-Link equipment, but could not see it anywhere as "added" to the whitelist, all it did was create another entire rule set, full of all the previous signatures. So now I have 3 "rules" each with 40 or so entries, some are identical, and really have no idea if this D-Link signature was indeed whitelisted? I am still very hazy on how, or where to see what is really added as whitelisted? Thank you for educating with me on this. I just want to make absolutely sure none of this is actually "whitelisted" as that would be horrifying.
-
3rd Party VPN
170 -
ACLs
101 -
Auto VPN
314 -
AWS
39 -
Azure
71 -
Client VPN
431 -
Firewall
715 -
Other
594