- Technical Forums
- :
- Security & SD-WAN
- :
- Firewall settings for guest network to enable VPN access to Meraki MX
Firewall settings for guest network to enable VPN access to Meraki MX
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Firewall settings for guest network to enable VPN access to Meraki MX
We are currently migrating our network to Meraki.
We have several network segments (different vlans) at our location including one for guests.
This network is isolated from the other networks, only internet access is enabled.
I've done this in the firewall like this:
deny any protocol source any port <corp-nw> destination any protocol <guest-nw>
deny any protocol source any port <guest-nw> destination any protocol <corp-nw>
allow any protocol source any port <guest-nw> destination any portocol any destination
That works so far.
When I'm connected to the guest Network, I cannot establish a VPN connection to our Meraki Gateway.
I think I have to create a rule to allow that connection... Can anyone tell me how?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
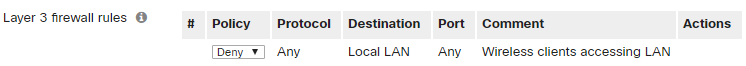
Wireless - Firewall - Deny local LAN , for your Guest Wifi?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I tried a little more. Port forwarding is working, sorry for that. I have only problems with VPN.
As I wrote the network seperation is not the problem. Also VPN from outside to corp lan works fine.
The problem is that I cannot establish this VPN connection when I'm inside the (local, Meraci-managed) guest network.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I would doubt that you could VPN in from inside of the MX to the outside of the MX. I don't think this is a valid config.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sure, from the network state it's not the best.
We have a larger number of mobile devices that connect to foreign public networks and our local guest network.
It would be helpful if the connection could work the same way.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I have setup VPNs on several firewalls and find that most cannot connect to the VPN from the LAN side.
I also have setup Routing and Remote Access on different Windows severs. With that config, users could connect to the VPN from the LAN.
A different way to accomplish a Guest Network that has managed access to the LAN, would be to setup an Employee Guest SSID that uses RADIUS to your server for authentication.
-
3rd Party VPN
167 -
ACLs
100 -
Auto VPN
313 -
AWS
38 -
Azure
70 -
Client VPN
427 -
Firewall
702 -
Other
588