Get answers from our community of experts in record time.
Join now- Technical Forums
- :
- Security & SD-WAN
- :
- Re: Dual MX and Dual ISP
Dual MX and Dual ISP
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Dual MX and Dual ISP
Never deployed in this configuration before, I've done single MX with dual wan, Is there a specific way to setup these MX in either hot spare or true LB config?
Its two MX 100 and two different ISP
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This is my typical setup. Most important is to have at least a /29 from both ISP so that both MXes can have an own IP on both ISPs subnets. Ideally you have also one spare IP as the virtual IP. The rest is pretty much straight forward.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
so do i need to create a DMZ of some sort for each ISP on one of the MS switches? Im having a hard time picturing the cabling
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
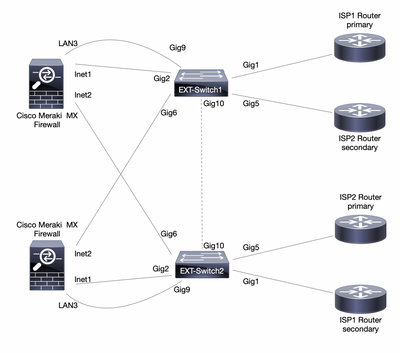
You should have two external switches for full redundancy. Here is a picture of my default-setup:
The external switches are typically Cisco Cat1000-10. Both MXes are connected to both external switches and the ISP-routers also go to both switches. The connection LAN3 on the MX to Gig9 on the switch is for the management of the external switches. This is a dedicated DMZ on the MX.
On the switches, Gig1-4 are VLAN A (ISP1) and Gig5-8 are VLAN B (ISP2). Gig9 is the management VLAN and Gig10 is a trunk.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
got it, that helps, but we don't have extra switches at the moment, both ISP are single router handoff (ATT/Spectrum). Is there a way to do this using an extra MS225?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@leadtheway :Below guide will help you out. Use load balancing and make backup for each other.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
yeah I understand that for load balancing the Wan connections, I also want to make the MX fully redunant
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@leadtheway : yes you can still do that redundancy. Let suppose x amount of traffic is passing through wan1 and y amount of traffic via wan 2, if wan 1 link down, the x amount of traffic failover to wan2 with y amount of traffic, similar vice versa.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes, but using a MS225 IMO is a waste of precious resources and with only one of them you still have a single point of failure. When using a Meraki-switch, just make sure that this external switch is in a different dashboard-network as the MXes.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
its an extra switch we aren't using. I just confirmed with ISP, one is a /30 and one is a /29 so not sure what I can even do now given your suggestions (which are awesome and will be used from now on)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
With only a /30, you can not directly connect both MXes to that ISP. I would try hard to replace the /30 with a /29. There are other solutions for this scenario but all make the setup more complex and again you need additional equipment:
You could replace one of the switches with an extra router and terminate the ISP on that link. Between the MX and the Router you have a private transfer-network that gives you enough IPs for both firewalls. In this case the router does the NAT and has a static route to your internal network while the MX is configured to not do any NAT.
Another solution is to connect the ISP1 (with the /30) only to your primary MX and ISP2 to both MXes. Here you only have full redundancy and both ISPs available on MX1, but that should not be a major problem.
-
3rd Party VPN
171 -
ACLs
91 -
Auto VPN
298 -
AWS
36 -
Azure
70 -
Client VPN
381 -
Firewall
851 -
iOS
1 -
Other
549 -
Wireless LAN MR
1