We're migrating to the Cisco Community on March 29. The Meraki Community will enter read-only mode starting on March 26.
Learn more- Technical Forums
- :
- Security & SD-WAN
- :
- Client VPN using vMX
Client VPN using vMX
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Client VPN using vMX
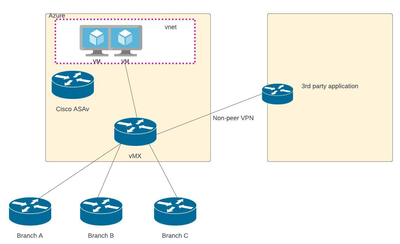
We will replace Cisco CSR1000v with vMX, vMX will be connect to site branches and have some non Meraki VPN peer networks. I have Cisco ASAv in Azure for VPN, we are planning to remove Cisco ASAv and use Meraki client VPN. My question is
1) How client VPN will communicate to 3rd party application that is connected through non-meraki VPN tunnel.(diagram attached) do i need to add routes(static etc)
2) How many users can connect at a time? do we need any additional license for this feature?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
When you enable AnyConnect on the VMX, the subnet will show up under "Site-to-Site VPN"
Here you can enable the subnet to have access to VPN. (No routing settings needed)
Your branch sites will not be able to communicate with the 3rd party application behind the non meraki peer via SDWAN if you're planning for this?
Depending on vMX model it handles different number of VPN clients:
https://meraki.cisco.com/product-collateral/mx-sizing-guide/?file
vMX small 50
vMX medium 250
vMX large 500
You need a seperate AnyConnect licens to run this
#QualityWiFi
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes plan is that they should access 3rd party application behind VPN(non meraki) then how should we try to do this? any recommendation
Branch A is MX
and other are Cisco legacy routers(not MX)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You just need to include the client VPN subnet in the encryption domain.
You could delay replacing the CSR1000v until all the legacy branches are replaced and then simply add a static route on that platform (for the client VPN subnet) and redistribute it into that VPN system.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Related to traffic between branch office and 3rd party application:
Since 3rd party application is accessed through https://abc.companydomain, I think it would work if all traffic goes to DNS in Domain controllers and DNS then points to 3rd party application link. So point is Branch offices DNS are pointing to Domain controller(DNS). Since all non peer will be connected to Azure network.
So if branch office wont communicate with each other but atleast they can communicate to 3rd party app(https://abc.companydomain.) what do you think?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You cannot reach a Non-Meraki VPN network (3rd party application) from a Meraki AutoVPN tunnel (Branch site)
Only local subnets on the MX that has the Non-Meraki VPN tunnel can reach it. (The AnyConnect subnet should work)
If you need access from branches to 3rd party application you need to build a Non-Meraki VPN tunnel from each branch and from vMX to the provider
#QualityWiFi
-
3rd Party VPN
174 -
ACLs
91 -
Auto VPN
306 -
AWS
36 -
Azure
70 -
Client VPN
382 -
Firewall
867 -
iOS
1 -
Other
557 -
Wireless LAN MR
1