Get answers from our community of experts in record time.
Join now- Technical Forums
- :
- Security & SD-WAN
- :
- Cisco Anyconnect Secure Client connectivity testing
Cisco Anyconnect Secure Client connectivity testing
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Cisco Anyconnect Secure Client connectivity testing
This mey be more of a Cisco Anyconnect question, than a Meraki question, but I have not yet been able to find an answer to this behaviour, and since it was on a Meraki MX I first discovered it, I'd might as well try here.
I am no expert in Cisco Anyconnect Secure Client, so I'm relying on others.
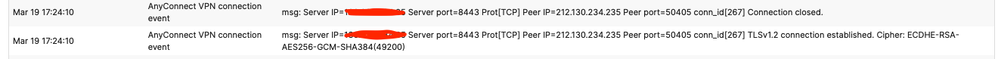
Lately I've been looking into integrating MFA with Okta and Cisco Anyconnect on a Meraki MX, with a customer. Some hours after our troubleshooting session, which went so-so, I noticed a bunch of TLS1.2 Connection Established followed by Connection Closed from my home public IP address, which more or less has continued throughout the weekend.
These two messages have continued many times during the weekend.
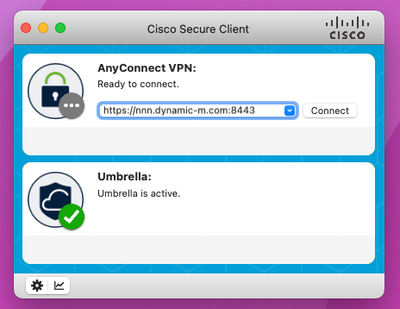
I have two Macbooks - a personal and a work machine, which I both used to test. Both machines have Secure Client installed, but neither of them were attempting to established a connection. I can not wrap my head around what is happening, but I have a theory that, in the Secure Client window, even though it is not opening a VPN connection what ever IP/hostname is in the Secure Client Server field, the client will continously test connectivity to that address? And that this test is a TLS1.2 handshake?
I seem to think that the messages with my public IP address didn't stop until I completely closed the Secure Client application on both macbooks.
Like what you see? - Give a Kudo ## Did it answer your question? - Mark it as a Solution 🙂
All code examples are provided as is. Responsibility for Code execution lies solely your own.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
have you checked the okta documentation?
https://help.okta.com/en-us/Content/Topics/integrations/cisco-meraki-radius-intg.htm
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This has nothing to do with the Okta implementation. The server ip is the Meraki MX, and the peer ip is my public address. Okta does not come into play here. But no, I haven't checked the Okta documentation.
Like what you see? - Give a Kudo ## Did it answer your question? - Mark it as a Solution 🙂
All code examples are provided as is. Responsibility for Code execution lies solely your own.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Is the MX configured to push profile updates to the client?
Have you got optimal gateway selection configured in the Cisco AnYconnect profile?
It will only use TLSv1.2 to connect.
Using a recent client version?
Not sure.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Profile updates are disabled, and we haven't made any specific profile for Anyconnect.
It just seems like the client is doing some connection attempts in the background without actually connecting, perhaps to test connectivity.
Like what you see? - Give a Kudo ## Did it answer your question? - Mark it as a Solution 🙂
All code examples are provided as is. Responsibility for Code execution lies solely your own.
-
3rd Party VPN
173 -
ACLs
91 -
Auto VPN
301 -
AWS
36 -
Azure
70 -
Client VPN
381 -
Firewall
856 -
iOS
1 -
Other
552 -
Wireless LAN MR
1