We're migrating to the Cisco Community on March 29. The Meraki Community will enter read-only mode starting on March 26.
Learn more- Technical Forums
- :
- Security & SD-WAN
- :
- Block intervlan routing MX64
Block intervlan routing MX64
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Block intervlan routing MX64
Hello,
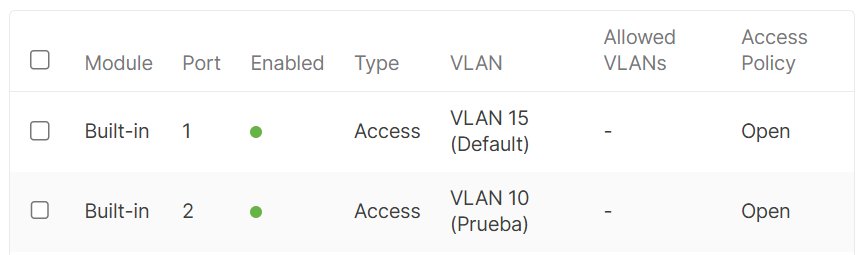
I have following LAN networks.
LAN1 Vlan15 192.168.128.0/24
LAN2 Vlan10 10.10.10.0/24
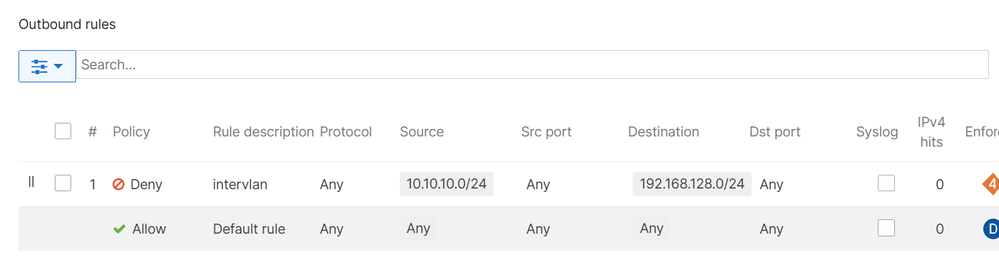
I want to block LAN1 to access LAN1. I created rules under outbound rules but they are not working. Please check Attached screenshots.
Please let me know what I am missing.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Fw rules do not work on active sessions. You need to wait like 10 minutes for the firewall to clear active session.
Or reboot the mx to clear all sessions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
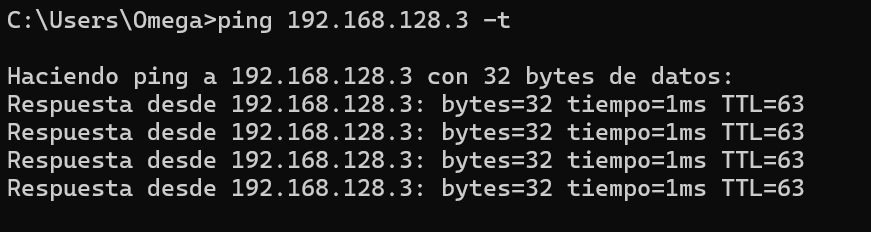
As well as this you need to test using actual end user devices, and not ping the MX itself as it will often ignore firewall rules. (Unclear if .3 is a host of the MX itself)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes, 10.10.10.4 is my PC and 192.168.128.3 is an Access Point. I will wait for 10 min to take effect. Thanks
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi, ok ok I will wait 10 min or reboot the router, I'll let you know.
is that time apply for every rule? I mean if I block 10.10.10.4 to access nike.com Do I need to wait 10 min to take effect? Because I also tried that and didn't work.
Thanks
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Im not sure about the session timeout, could be 5-10 minutes. Also would depend on if the protocol closes the session itself or not.
If you didnt go to that website before, it should work/be blocked.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
For vlan to vlan it worked, but not for a web domain.
I have used this rule:
but ping to www.nike.com always runs:
I have also changed to "Any" instead of ICMP, but it still runs:
Thanks
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
If I recall correctly, ICMP needs to age out. Rules for more common actual application flows tend to take effect immediately.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @EdgeFarming
If traffic is still being allowed from VLAN 10 to VLAN 15, it is possible these are flows existed prior to creating this rule. I would suggest rebooting your MX appliance to end these current flows and check again. Please navigate to Security & SD-WAN > Appliance status > Tools > Firewall logging tool, to check if a flow from VLAN 10 to VLAN 15 is allowed or blocked if you would like to test this live.
I've attached a KB below on utilizing the "Firewall logging" tool from the tools page for reference:
https://documentation.meraki.com/MX/Firewall_and_Traffic_Shaping/Firewall_Logging#Quick_Start_Guide
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
For vlan to vlan it worked, but not for a web domain.
I have used this rule:
but ping to www.nike.com always runs:
I have also changed to "Any" instead of ICMP, but it still runs:
Thanks
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Does the MX definitely see (route) the relevant DNS queries and responses?
Appropriate visibility is needed to turn the domain name into the correct IP-layer rule
Is there any chance the lookup involves CNAME responses?
https://documentation.meraki.com/MX/Firewall_and_Traffic_Shaping/MX_Firewall_Settings#FQDN_Support
I'd look to see if you can packet capture the full query & response
Maybe think about a case with Meraki Support to assist with this - specifically and more generally
-
3rd Party VPN
174 -
ACLs
91 -
Auto VPN
305 -
AWS
36 -
Azure
70 -
Client VPN
381 -
Firewall
865 -
iOS
1 -
Other
556 -
Wireless LAN MR
1