Get answers from our community of experts in record time.
Join now- Technical Forums
- :
- Security & SD-WAN
- :
- AutoVPN: Hub to Hub?
AutoVPN: Hub to Hub?
Solved- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
AutoVPN: Hub to Hub?
Solved! Go to solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hubs will always connect to other hubs, that is standard Meraki AutoVPN operation. With spokes you can select which hubs they will connect to. The exit hubs should work fine. What you are describing sounds similar to what is often called regional hub-and-spoke in this document, https://documentation.meraki.com/Architectures_and_Best_Practices/Cisco_Meraki_Best_Practice_Design/...
I doubt this will assist with some of your issues, which appear to be due to the Great Firewall, but as a concept it should work.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hubs will always connect to other hubs, that is standard Meraki AutoVPN operation. With spokes you can select which hubs they will connect to. The exit hubs should work fine. What you are describing sounds similar to what is often called regional hub-and-spoke in this document, https://documentation.meraki.com/Architectures_and_Best_Practices/Cisco_Meraki_Best_Practice_Design/...
I doubt this will assist with some of your issues, which appear to be due to the Great Firewall, but as a concept it should work.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Excellent Thanks Bruce.
I wasn't aware you could have more than one Hub in an Org, and therefore assumed the only topology available was a hub and spoke setup. Thanks fo the link to the doc, very helpful - not sure why that didn't come up in my google searching.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
I now have the trial vMX's setup and running on Alibaba Cloud and part of my Org. However, I'm struggling to get the basic setup working.
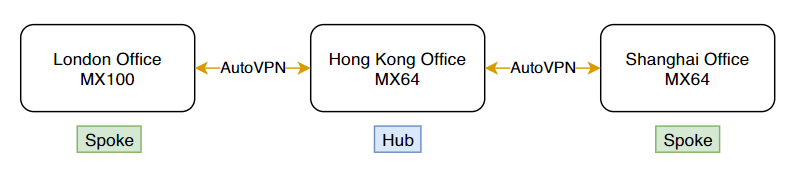
My current setup is:
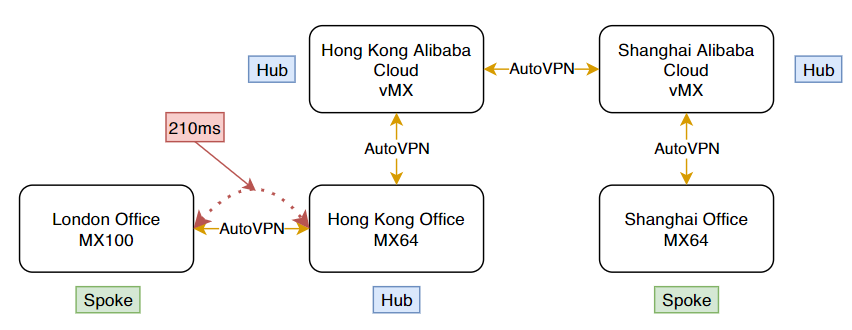
The end goal is this topology:
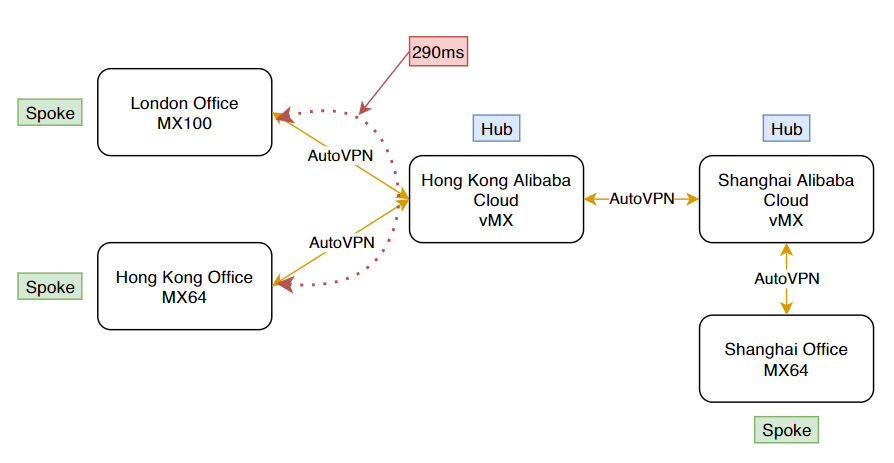
As a side note, I would prefer to keep the London <> Hong Kong Office AutoVPN as it is as latency is good at 210ms. I would prefer to avoid the scenario below, where these sites are both spokes to the HK vMX as this increases latency between these sites.
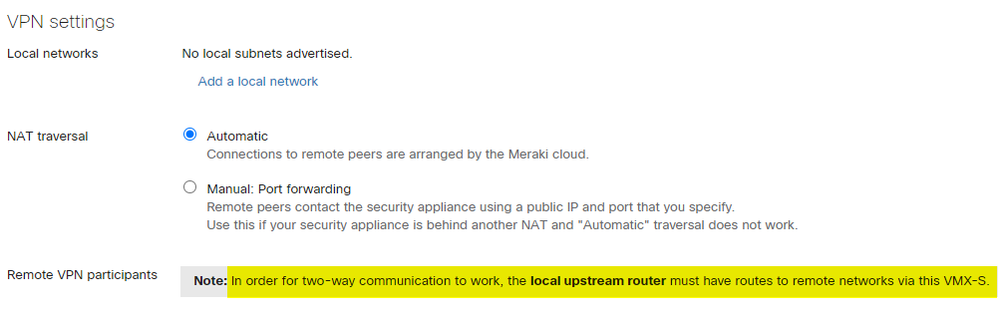
Anyway, back to my point, in the vMX's > Security & SD-WAN > Site-to-Site VPN, it says about adding routes to the upstream router.
I presume this means the Alibaba Cloud VPC. Here, I have created static routes for 192.168.110.0/24 (which is the network the HK Office MX64 is in), next hop = ECS instance (HK vMX)
However, with this in place, if I go to the HK Office MX > Appliance Status > Tools > Ping the internal IP of the HK vMX, I get no reply (100% loss).
When looking at Organization > VPN Status, I see all sites connected. On the HK vMX, if I run a packet capture on the site-to-site VPN I get nothing at all🤨
What am I missing? Thanks in advance.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I think I would request some free trial VMXs and test it out. Then you'll know for sure.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks @PhilipDAth .
I have registered my interest in the trail of the two vMXs so look forward to getting that setup and I will update this post when testing is underway.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
And he was never heard from again...... 😢
-
3rd Party VPN
172 -
ACLs
91 -
Auto VPN
301 -
AWS
36 -
Azure
70 -
Client VPN
381 -
Firewall
855 -
iOS
1 -
Other
551 -
Wireless LAN MR
1