- Technical Forums
- :
- Full-Stack & Network-Wide
- :
- Re: User-Agent known malicious user-agent string - Win.Trojan.Batlopma
User-Agent known malicious user-agent string - Win.Trojan.Batlopma
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
User-Agent known malicious user-agent string - Win.Trojan.Batlopma
Hi all,
I'm trying to dig down into my device event logs, as I'm continually seeing this pop up a number of times every week. Unfortunately, the furthest I can get down is to the AP level. Beyond that, I have no way of narrowing it down to an offending device.
I just want to confirm whether or not its a false-positive.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
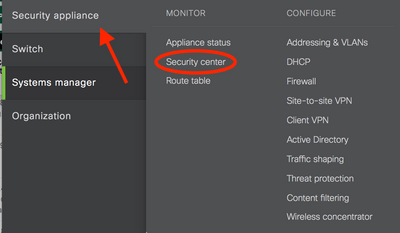
Are you running an MX appliance as your gateway? If so you should be able to get the information you are after from the security centre as shown in the attached screenshot.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Blake,
I appreciate your reply. Unfortunately, if you're talking about the link that takes me to Snort, its not very helpful --
https://snort.org/rule_docs/1-39362
Additional, it doesn't tell me the actual endpoint. I'm only seeing my own Access Point. Per Meraki themselves -- Hi,
If the device is connected to a NAT mode SSID which it looks like it is, there is no way to know what specific device generated that alert.
But that doesn't sound totally right. I'm not sure why I wouldn't be able to see the "offending" device beyond the AP.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Can you change the SSID to use bridge mode, and have the MX doing the NAT?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Philip, I'm going to see if I can change that SSID tonight and do some testing. Will have to report back if this is feasible for the wireless at this time.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Did you resolve anything with this? I have a number of work cell phones triggering it while using a legitimate site. I think it is a false positive. I actually know it is specific cell phones just based on the numbers of occurrences and people coming to IT saying a legitimate app is not working.
Thanks,
Chris
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I narrowed this down with one of my users based on device/geography/time of use and it looks to be WeChat for our scenario.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sorry for the late reply, the events are infrequent so I haven't kept them at the top of my radar. I haven't made any changes to the wifi just yet.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Seeing that in one of my clients. Connects back to IP addresses belonging to Tencent according to whois.domaintools.com. Wondering what it is. All "affected" devices are ios in this case.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I'm seeing this to an Android device in a customer. Calls back to a server hosting malicious domain for 1 week, according to Umbrella - and its nameserver has co-ocurrences to many malware samples.
Android threat hunting is a challenge though, lack visibility as per initial comment.
Camillo
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
+1 to that comment. I feel the same frustration as you for androids - I am.trying to correlate using AMP for endpoints, umbrella and Meraki MX. AMP4E on Android gives very limited control and visibility.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I have found AMP to be flagging some antivirus (ESET, BitDefender) updates and Android service updates as "Win.Trojan.Batlopma". I've found that I sometimes need to temporarily disable AMP to get these updates to work.
I hear MX 14.x solves some issues with AMP, but I'll have to wait until that comes into the stable stream.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@kordm 14.x is solid. Don't wait - because it probably has less issues than what you are using now. There is no point staying on 13.x with its issues just because of a label.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I've also gathered this is WeChat related and we're on MX 14.38. Additionally, we've tested MX 15.1 and still see the issue. From what I gather, this issue sits in one of two places - either the SNORT rule is out of date and needs to be updated with false positive info (which support is apparently useless for - they'll just suggest "whitelist") or the SNORT implementation from Meraki needs some tweaking. Would be great to see this fixed...