We're migrating to the Cisco Community on March 29. The Meraki Community will enter read-only mode starting on March 26.
Learn more- Technical Forums
- :
- Mobile Device Management
- :
- Info: Signing macOS packages with a cert
Info: Signing macOS packages with a cert
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Info: Signing macOS packages with a cert
For security reasons, and to protect users, it may sometimes be required that you prevent unsigned (or unknown) packages from being deployed.
If you're downloading a PKG from a vendor's website, then this *shouldn't* normally affect you. But, if you want to build your own packages (custom pre and post flight scripts, for example), or the application vendor hasn't signed their app (you should consider why this is), then here's a simple guide on how to sign a package for deployment using Meraki Systems Manager
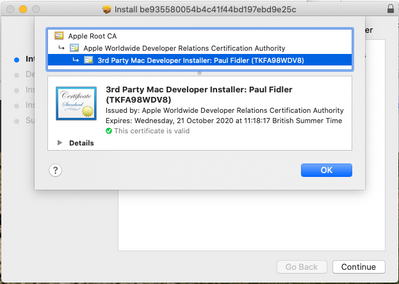
If you don't know if a package is signed on not, when running the installer manually, you'll see a padlock in the top right: Clicking on this will show you the signing certificate
Requirements:
You’ll need a developer account at https://developer.apple.com along with a paid for subscription.
Part One: Apple Developer Website
- Log on to: https://developer.apple.com/account/resources/certificates/list
- If redirected, go to Account > Certificate, IDs & Profiles
- You should have any certificates already created. Click the +
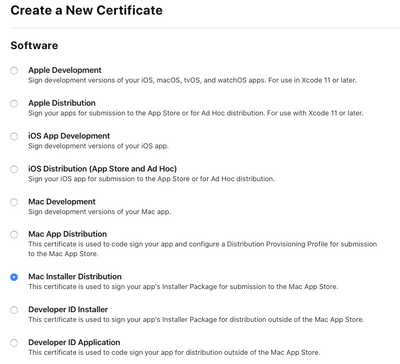
- Select Mac Installer Distribution, as shown, and click Continue
- The site will now ask for your CSR...
Part two: Creating a CSR
- Open Keychain Access on your Mac
- Click Keychain Access > Certificate Assistant > Request a Certificate from a Certificate Authority.
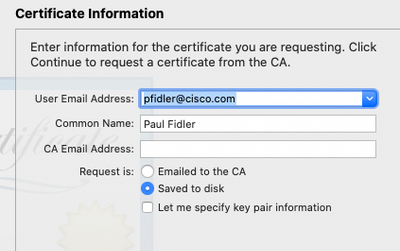
- Enter an email address in User Email Address.
- In the Common Name field, enter a name for the key
- Leave the CA Email Address field empty.
- Choose “Saved to disk”, and click Continue, and save this.
More details here: https://help.apple.com/developer-account/#/devbfa00fef7
Part 3: Requesting your certificate
- Go back to your web page at Apple Developer
- Under Create a New Certificate, click Choose File
- Select the CertificateSigningRequest.certSigningRequest file you created earlier
- Click Continue
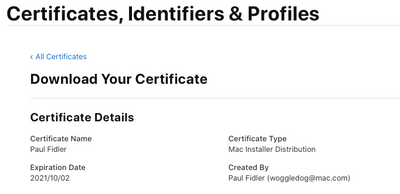
- You can now download your certificate
- Double Click this to add to your Mac’s keychain (You may wish to create a new keychain to keep your developer certs)
Part Four: Signing your package
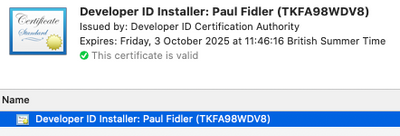
You’ll need to know the identity of the signing certificate you created in the first section. You can find installed Identities with:
security find-identity -v -p codesigning
Open Terminal in the directory where your newly created install package is. We are going to use com.meraki.plistonly.pkg
Type:
productsign --sign 'Developer ID Installer: Paul Fidler (7H6G5F4D3D)' com.meraki.plistonly.pkg com.meraki.plistonly-signed.pkg
You’ll be prompted for the currently logged in user’s password.
You should see the following:
productsign: using timestamp authority for signature
productsign: signing product with identity "Developer ID Installer: Paul Fidler (7H6G5F4D3D)" from keychain /Users/Paul.Fidler/Library/Keychains/login.keychain-db
productsign: adding certificate "Developer ID Certification Authority"
productsign: adding certificate "Apple Root CA"
productsign: Wrote signed product archive to com.meraki.plistonly-signed.pkg
And, et voila, you now have a signed installer called com.meraki.plistonly-signed.pkg !