We're migrating to the Cisco Community on March 29. The Meraki Community will enter read-only mode starting on March 26.
Learn more- Learning Hub
- :
- Resources
- :
- ECMS Exam Self-study Lab Supplement
ECMS Exam Self-study Lab Supplement
Introduction
This self-study lab supplement is intended to help exam candidates set up their own lab environment in order to become well-versed in using the Meraki Dashboard. In addition to the lab environment guidance, this supplement provides an outline of the products, features, and tools that candidates should use to achieve suitable proficiency within the Meraki Dashboard.
For a full list of recommended study materials, please click here.
Table of Contents
Lab Environment
The most ideal Meraki lab setup for candidates include an account with full organization administrator access to the Meraki Dashboard. If that is not possible, the candidate should at least have read-only org admin privileges to a Dashboard organization.
Note: Read-only access will enable a candidate to become familiar with Dashboard and most Meraki features. However, some Dashboard user interface elements and features are only visible to admins with full permissions. Similarly, the user will be unable to commit configuration changes and unable to fully test the impact on the network.
Bill of Materials
The recommended minimal viable lab consists of the following bill of materials
|
Recommended Equipment |
Alternate Models |
License* |
|
MX67 |
MX67C, MX67W, MX68, MX68CW, MX68W, MX75, MX85, MX95, MX105, MX250, MX450 |
Advanced Security** |
|
Z4 |
Z4C, MX67, MX67C, MX67W, MX68, MX68CW, MX68W, MX75, MX85, MX95, MX105, MX250, MX450 |
Advanced Security** |
|
MS250*** |
MS250, MS350, MS355, MS390, C9300-M |
Enterprise |
|
MR36 |
MR36, MR44, MR46, MR46E, MR56, MR57, MR76, MR86 |
Enterprise or Advanced |
|
MV12WE |
MV12N, MV12W, MV22, MV22X, MV32, MV52, MV63, MV63X, MV72, MV72X, MV93, MV93X |
Enterprise |
|
MT10 |
MT11, MT12, MT14, MT15, MT20 |
5x Free Licenses |
*Cisco Meraki licenses can be purchased in various durations (1 day, 1 year, 3 years, etc.) and a license that matches the hardware must be applied in Dashboard to avoid device or organization shutdown.
**Candidates may choose to obtain another additional, separate Meraki Insight (MI) license or an Advanced SD-WAN Plus MX license, which is inclusive of MI features. This will enable the candidate to gain hands-on experience with MI features and configurations. This is an optional component, as reviewing all suggested MI study materials is sufficient for exam preparation.
***The recommended switch model must support Layer 3 routing and PoE.
It is possible to test many Systems Manager features without having an SM license in a Dashboard organization (e.g. creating and merging an SM network, configuring management profiles and application payloads). However, the candidate will need a license to enroll a client device to Systems Manager and test pushing configuration profiles. A SM license was not included in the bill of materials table because candidates can utilize Cisco Meraki’s free 30 day trial license for Systems Manager. The trial automatically starts upon enrolling a device into any unlicensed Systems Manager network.
Note: A paid Systems Manager license is required to keep devices enrolled beyond 30 days. If the device is not unenrolled/removed within 30 days, the Dashboard organization will be at risk of being shut down.
Workstation
The candidate should also have a laptop or a desktop with wireless and ethernet ports. Having a physical ethernet port will enable the candidate to test wired access and associated features.
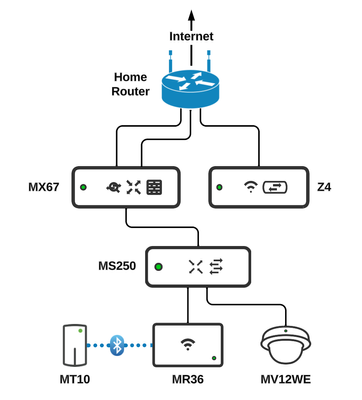
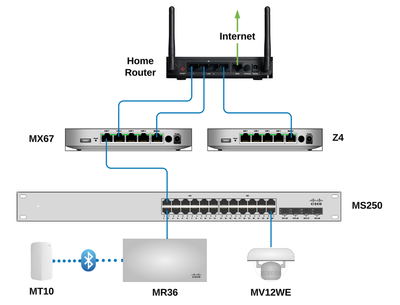
Lab Network Diagrams
The following network diagrams show the recommended topology and network deployment of the lab equipment.
Note: The network topology depicted in this guide is NOT a typical, real-world deployment recommendation. This network topology is strictly for the purposes of testing out Meraki features and it does NOT follow traditional practices/designs for actual production networks.
Figure 1: lab topology diagram overview
(depicted using traditional network icons)
Figure 2: lab topology wiring diagram
(suggested port interconnects between devices)
Installation
Candidates should reference the following installation guides for detailed instructions on how to properly deploy each piece of lab hardware.
- MX Installation Guides
- MS Installation Guides
- MR Installation Guides
- MV Installation Guides
- MT Installation Guides
Guidance of Topics and Features
The following consists of the recommended topics, features, and concepts that a candidate should practice within their lab environment during their preparation for the certification exam. The list is not exhaustive and the exam subject matter is subject to change as a result of updates to the Meraki Dashboard’s user-interface and/or product feature updates.
Network-wide (cross platform)
- Configure network timezones
- Create, apply, and verify device tags
- Create and define network-wide group policies to address scenarios such as the following:
- Configured to allow devices such as corporate clients
- Configured to contain/restrict blocked devices or those in violation
- Tuned to override or append default network settings
- Create and define network-wide group policies that address devices which should be contained
- Configure Sentry policies to enforce group policies based on a device’s dynamic security policy tags
- Understand the available alert trigger options of each product family and how to configure recipients for email alerting (including adding non-Dashboard recipients)
Security and SD-WAN
- Configure basic addressing
- Configure Auto VPN in various topologies (i.e. mesh, hub-and-spoke) as well as defining local networks for VPN advertisement
- Understand the elements of the VPN Status page to accomplish the following:
- Troubleshoot problematic VPN connections between peers
- Interpret uplink decisions made by the MX appliance of active connection flows
- Create and configure static routes required for dynamic routing (OSPF) route redistribution
- Enable, configure, and verify dynamic routing (OSPF) including analysis of the following:
- Route table page
- “Static routes” table on the Addressing & VLANs page
- Configure proper SD-WAN settings including the use of the following:
- Uplink throughputs for WAN interfaces
- Load balancing
- Flow preferences of various internet traffic types
- VPN traffic selection policies with different traffic filters (including the use of custom created performance classes)
- Configure and verify traffic shaping rules for various scenarios including:
- High priority traffic types such as VoIP and video
- Guests and low priority traffic categories
- Create layer 3 and layer 7 firewall rules
- Enable Advanced Malware Protection
- Enable and configure Intrusion Detection & Prevention
- Enable and configure content filters and URL patterns
- Restrict web search results and enforce YouTube Restricted Mode
Switching
- Configure switch ports (in bulk) with basic setting such as:
- Access/Trunk port type
- PoE settings
- Defining VLANs (including dedicated voice VLANs)
- Create, apply, and verify switch port tags
- Configure and verify an Etherchannel
- Configure and verify a port mirror
- Create and configure switch virtual interfaces (SVI’s)
- Enable, configure, and verify OSPF
- Modify and verify switch ports for proper VoIP deployment
- Configure and verify QoS rules for proper VoIP deployment
- Configure and apply access allow/restriction policies to switch ports using the following:
- MAC whitelist
- Sticky MAC
- Create, configure, and apply user-defined access policies that leverages 802.1X using the following:
- Meraki Authentication
- RADIUS server for authentication
- Systems Manager Sentry
- Create, configure, and apply a port schedule to switch ports
Wireless
- Create and configure SSIDs with various basic association, splash page, and client IP assignment types
- Configure and verify QoS and traffic shaping rules for proper VoIP deployment
- Create layer 3 and layer 7 firewall rules
- Create and configure a dedicated SSID for guests with the following settings:
- Appropriate firewall restrictions and traffic shaping rules
- A custom splash page
- An SSID schedule
- Create and apply RF profiles
- Create and add SSIeD blacklist and whitelist entries to Air Marshal
- Configure and enable SSID alerting in Air Marshal
- Generate a PCI report and focus on the following tasks:
- Proper adjustment and calibration of the scope and environment of the PCI reporting tool
- Identify and review the passed and failed requirements of a completed report
Endpoint Management
- Create and configure Apple profiles for enrolled devices
- Create and configure Android profiles for enrolled devices
- Define the target scope of configured profiles through the use of various tag types (device, policy, user)
- Add and configure different settings payloads to profiles (e.g. restrictions, passcode policy, WiFi settings)
- Create and define security policies
- Import, manage, and push applications out to clients enrolled in SM
- Understand the list of MDM commands that are available
- Understand the list of Live Tools that are available
Smart Cameras
- Identify the available options, features, and settings of the camera platform and how they impact the overall retention capacity
- Identify and review the configurable motion alerting options
- Create and configure video wall layouts
- Review the workflow of building and applying wireless profiles
Smart Sensors
- Identify the various methods for establishing connectivity to Dashboard
- Create and configure sensor Alert Profiles
- Create and customize sensor alert notifications
- Establish and review the relationship between sensors and cameras within Dashboard.
Application Assurance
- Add and configure web applications to be tracked through Web App Health
- Understand the threshold indicators of tracked applications as presented through various filters and perspectives (i.e. per network view, client details view)
- Analyze application trends and configure relevant alerts
- Analyze the status of uplinks and metrics tracked through WAN Health
Organization (administration and troubleshooting)
- Carry out the deployment of a new network including:
- Create a new network (single product and combined)
- Claim and add devices
- Claim, apply, and renew licenses
- Understand how to utilize the elements within the “Help” drop-down menu including the following:
- Obtaining relevant firewall information
- Opening a case with Meraki Support
- Enable, generate, and manage API access for Dashboard administrators
- Add new organization administrators to Dashboard and grant various permission levels
- Scheduled and manage firmware upgrades
- Generate, review, and analyze summary reports for essential information
- Review the information found on Dashboard’s Firmware Upgrades page including the various filters available on the All Networks sub-tab
If you have feedback on any of the content found on this exam preparation resource, please leave a comment below for the Cisco Meraki team. Your comment will not be viewable publicly. We are constantly working to improve this page and welcome suggestions, but cannot guarantee a direct response to every comment.
Last Updated: February 2024