Get answers from our community of experts in record time.
Join now- Technical Forums
- :
- Cloud Security & SD-WAN (vMX)
- :
- vMX public IP has been changed by itself
vMX public IP has been changed by itself
Solved- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
vMX public IP has been changed by itself
Hello,
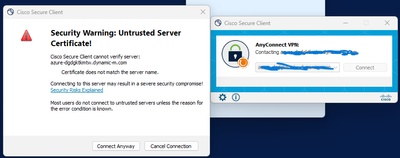
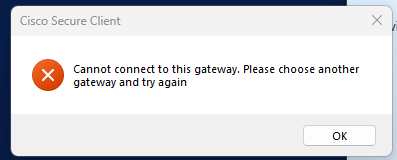
I got an issue regarding client VPN, users are not able to connect to Anyconnect client VPN. This solution was deployed 2 years back and working fine until few days back we got this problem. upon investigation i see the Public IP in Meraki dashboard is different the one associated to meraki VM nic in Azure. I am suspecting it has been changed, Any idea what to do?, and how the IP on dashboard is different and in Azure portal associated to VM is different?
Current firmware MX 18.107.7,
I did all troubleshooting related to below issue: but i am sure its about the public IP.
Solved! Go to solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks guys @PhilipDAth @jhoney12 @BlakeRichardson @alemabrahao for your suggestion. It has been rectified. problem was the service provider was managing both express route circuit(Azure) and newly deployed FW, and they diverted all default route from express route circuit to the FW, due to which the vMX appliance got the public ip of FW. default route was removed and vMX got actual IP(Azure provided at VMX interface) and the Client VPN gateway has started to work. It can be done by the FW IP,but that was not intended to do config in FW for this solution(managing certificates,DNS records etc)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Does it have a dynamic IP?
If yes, it assigns a dynamic public IP to the vMX. If the device is ever rebooted in Azure, it will change the public IP. You might want to consider using DDNS instead of an IP address since it’s dynamic.
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
2 years with a dynamic public facing IP is a pretty good run. Dynamic DNS or see if you can obtain an static IP for your vMX
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
All MX's support DDNS (you don't even pay to pay for it). Get your VPN users to connect to that.
https://documentation.meraki.com/MX/Other_Topics/Dynamic_DNS_(DDNS)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Two years with a dynamic public-facing IP is quite a commendable stretch. You might want to consider implementing Dynamic DNS, or explore the option of obtaining a static IP for your vMX. It could provide more stability and control over your network configurations.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
hi
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks guys @PhilipDAth @jhoney12 @BlakeRichardson @alemabrahao for your suggestion. It has been rectified. problem was the service provider was managing both express route circuit(Azure) and newly deployed FW, and they diverted all default route from express route circuit to the FW, due to which the vMX appliance got the public ip of FW. default route was removed and vMX got actual IP(Azure provided at VMX interface) and the Client VPN gateway has started to work. It can be done by the FW IP,but that was not intended to do config in FW for this solution(managing certificates,DNS records etc)
-
3rd Party VPN
1 -
Auto VPN
26 -
AWS
17 -
Azure
57 -
Client VPN
6 -
Cloud native firewall
2 -
Cloud networking
26 -
Firewall
5 -
Hybrid Cloud
6 -
Multi Cloud
3 -
Multi Region Cloud
4 -
Other
7 -
Quick Start
1 -
Virtual firewall
30