We're migrating to the Cisco Community on March 29. The Meraki Community will enter read-only mode starting on March 26.
Learn more- Technical Forums
- :
- Wireless
- :
- Weird Client Connectivity Issue
Weird Client Connectivity Issue
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Weird Client Connectivity Issue
Good morning,
I am having a really odd issue right now with one device. We are a full Meraki house with MS350 access switches, ms425 core switches, and a MX250 firewall. Our AP's are also Meraki and they are all MR46's. We are a school district and probably have around 230 AP's districtwide.
I have one Dell Windows 10 laptop that when I connect it to any SSID that is not a splash page SSID, it connects but with no internet. All internal services are working (DHCP, DNS, File Shares, etc.) but it won't go out to the internet. When I try to go to the internet, it redirects to a Meraki splash page that asks for a username and password and says "Welcome to High School - Appliance". We don't have any SSID's with a splash page setup like this. For reference, our MX250 is named High School - Appliance.
Now here is the weird part. By default, Windows does not turn on MAC randomization on the WiFi profiles. The SSID I am using to test here is a standard WPA2 PSK network with no splash pages or anything custom. It tags to a specific VLAN but thats it. If I turn on MAC randomization on the SSID profile in Windows, the device connects with no issue and is able to go out to the internet. Once I turn randomization off, it goes back to doing what it was doing before with the splash page information I listed above. It is for this reason, I think there is something on the Meraki end that is causing this. I have no issues connecting other devices to this network districtwide.
I have searched the Meraki dashboard high and low and I can't find anything that would show this device being applied a special policy or blocked or anything like that. I have a TAC case open and the TAC support engineer yesterday was doing packet captures on it and couldn't really figure out what was happening. He saw it reaching out to our domain controllers and other internal services but then saw the redirection to the splash page. Has anyone ever run into anything remotely close to this? I am about to call TAC back to try and troubleshoot more but I am running out of ideas on this. I would prefer not to have to drop this client in a special OU in AD just to apply a WiFi profile that has MAC randomization turned on. Thank you for your time.
- Labels:
-
Other
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Regarding the page issue, didn't you check if splash login is not configured in the MX?
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
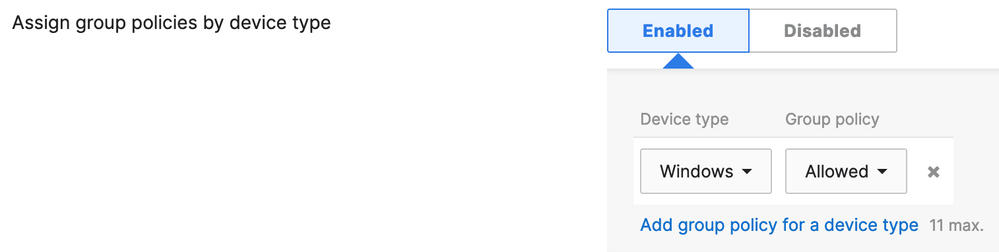
Are the SSIDs configured for assign policy by device type? https://documentation.meraki.com/MR/Group_Policies_and_Block_Lists/Applying_Policies_by_Device_Type
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thank you for your replies.
alemabrahao - Since we Active Directory integration enabled on the MX, according to Meraki documentation the splash page feature in the MX is disabled.
Ryan_Miles - Currently we do not have any of these device type Group policies set on this SSID. With that being said, it was turned on when we were initially setting everything up. I checked the client list and this device shows up with a normal policy and does not list that it is being blocked.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
As a test have you tried/can you try manually assigning the Allow list policy and report back if that changes anything? https://documentation.meraki.com/General_Administration/Cross-Platform_Content/Blocking_and_Allowing...
Also, do you have other SSIDs? Can the client connect to those? Or create a temp test SSID and try to connect.
And you mentioned policy by device type was at one point configured. On this SSID if you toggle policy back on without clicking save does it show device type policies like this? If it does maybe try deleting it (click the x) then choose disabled, then save the page.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
If the burned in MAC isn't working the MAC is likely filtered or blocked somewhere along the line, keep digging. Perhaps its being contained by WIDS/WIPS or an explicit blocks via group policy....
just as a matter of principle since its a WPA2-PSK and Windows:
- Update the windows drivers.
- Open Power Shell or Command prompt and Type the following command to view wireless settings and press Enter: netsh wlan show interfaces Does this show your actual PHYSICAL MAC? If so, proceed. If not make sure random mac is deleted by flipping the switch in wireless connection's. Rinse and repeat
- Open Power Shell or Command prompt and type the following command to view the wireless network profiles saved on your computer and press Enter: netsh wlan show profiles
- How many saved profiles are here? If the user is like most typical user there will be a whole heck of a lot. Many of which are invalid, stale, old ,corrupt.
In Power Shell or Command prompt Enter: netsh wlan delete profile name=* This will flush the profiles but you may want to also eradicate them from the registry:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\NetworkList\Profiles
- How many saved profiles are here? If the user is like most typical user there will be a whole heck of a lot. Many of which are invalid, stale, old ,corrupt.
- Reboot and try to connect using the actual MAC, you will have to enter the PSK for your network again, so have it handy.
Also, to rule out the actual NIC you could try replacing it..... I still suspect its blocked or contained somewhere.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Good morning TBHPTL,
Thank you for your response. When working with TAC the other day I reinstalled the card in Windows with the most current drivers from Dell. Unfortunately, that did not work. I ran the show interfaces command and that is showing the actual physical mac of the wireless card. When I listed the profiles, there was only the one PSK profile there under user. There was also a Group Policy profile. This is for a new 802.1x network we setup that uses EAP-TLS. I ran the command to remove everything however the Group policy one can't be removed since its pulled down from policy. When I looked at the registry though there was over half a dozen profiles in there from profiles I already deleted off this laptop. I deleted everything under Profiles there in the registry. Rebooted and I am still getting the same redirection issue. I do think there is something in Meraki somewhere blocking or containing this but I can't find anything on the dashboard. I am hoping TAC can find something behind the scenes here. If they can't, I may just have to randomize the MAC for this machine to get it working.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You are most definitely being filtered if it works with LMAC . The real MAC is on a naughty list somewhere.
this is why mac filtering is an ineffective tool, too easy to circumvent