- Technical Forums
- :
- Wireless
- :
- Re: Deny access to ssid
Deny access to ssid
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Deny access to ssid
Hi,
I have some users connecting to a ssid (let´s call it NetworkA) where authentication is done with Microsoft radius to AD.
Is it somehow possible to automatic deny access to other ssid for a device that´s connected to NetworkA?
Regards
Robert
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
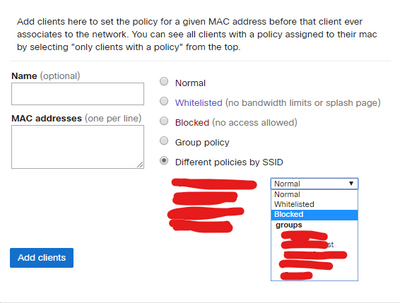
What you can do is block access to SSID from the Clients tab. You can import all the MAC addresses and block them.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
it´s a way, but not a pretty way 😃
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@RVilhelmsen why would a user, that has an active connection to network A SSID then try and connect to the second SSID also how would you having them authenticate on the second ssid ?
CMNA, CMNO, ECMS2
SNSA, SNSP
~~If you found this post helpful, please give it kudos. If my answer solved your problem, click "accept as solution" so that others can benefit from it.~~
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
maybe some users connect to a less restricted network 😉
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Then I would use group policies, once a user has connected to an SSID, assign the policy and then every-time that device connects the policy will control wheat they can do and where. they can go
CMNA, CMNO, ECMS2
SNSA, SNSP
~~If you found this post helpful, please give it kudos. If my answer solved your problem, click "accept as solution" so that others can benefit from it.~~
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
how can i block access to other ssid from a group policy?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
OK, let me set up a lab to have a look at the best way to do this for you, may take a couple of days, if thats OK
CMNA, CMNO, ECMS2
SNSA, SNSP
~~If you found this post helpful, please give it kudos. If my answer solved your problem, click "accept as solution" so that others can benefit from it.~~
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thank you - that´s super fine.
I am stuck and can´t figure out a automatic way to do this.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Use dot1x to authenticate the second SSID, and configure RADIUS not to allow the first group of users to connect to it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I can´t as the other ssid is a guest ssid.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I believe tagging can be an alternative for management across SSID for users in different AD groups, similar to https://documentation.meraki.com/MR/Other_Topics/Using_Tags_to_Broadcast_SSIDs_from_Specific_APs
Thanks!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Use one SSID with iPSK, default it to public VLAN on the RADIUS server and set it so that known MAC addresses go to corporate VLAN.