Get answers from our community of experts in record time.
Join now- Technical Forums
- :
- Wireless
- :
- Meraki hosted radius EAP failure
Meraki hosted radius EAP failure
Solved- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Meraki hosted radius EAP failure
Hi, could someone confirm that there possibly was a change in the security policy of Meraki radius on the AP's?
I have a customer that works with older scanners that use Meraki radius to join the SSID but started failing since yesterday.
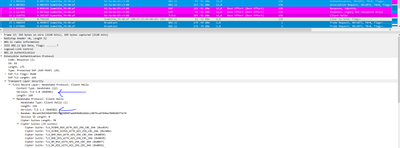
An OTA was not possible but I could capture from the AP that the user was trying and thus I only have upstream packet capture. This showed that the scanners associate but stop at the EAP client handshake. I see modern cipher sets but only older TLS versions in use. Could this be it?
Solved! Go to solution.
- Labels:
-
SSID
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
We have the same issue with the Meraki Radius server and It's confirmed by the Meraki support desk that they have a global issue in their platform. They are working on a solllution with high priority.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
We have the same issue with the Meraki Radius server and It's confirmed by the Meraki support desk that they have a global issue in their platform. They are working on a solllution with high priority.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@Nordinio , have you heard anything back? I have switched something over to wired for the time being, and am waiting on this forum post before attempting to put it back on wireless. Thanks!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Issue was restored by Meraki on the 26th of January at around 20:45 H CET.
There was a proprietary issue on their backend which began causing issues for clients that were only capable of using TLS1.0 or 1.1.
Clients capable of using TLS 1.2 continued working as expected.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Nordinio, we experience an outage as of 1/25/22. The several times I contacted Meraki they did not indicate an outage, although our SSID that authenticates against our NPS server stopped working since then. Our PSK SSIDs were not affected. I found the post below that finally solved our problem Not sure where the MTU size was change, the provider or whatever. On the post they had Meraki change the MTU size to lower than 1500. I went our NPS server and changed our network policy (Settings tab) and under Standard added Frame-MTU and set it to 1344 and that resolved our problem. I'll adjust that amount up later to see how high I will still work but it got this going again. I hope this helps someone. Thank you. https://community.meraki.com/t5/Wireless-LAN/802-1X-EAP-failure-with-Windows-AD-Radius-Help/td-p/319...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I think Meraki really needs to add a global status page to the supprot section of their main website. Users shouldn't have to get in touch with support to find out there is an outage.
Just about every other cloud based system I use has a system / service status page available to customers to check if they are having issues.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Ok thanks for sharing your experience @Nordinio .
The issue was not happening with windows based clients at that time so it's very specific to certain ways of TLS session building.
As a follow up question.
I noticed that there was no traffic going towards the cloud from the AP while the client was attempting to authenticate. Is it so that users are stored inside the AP's instead of AP's reaching out to the cloud every time a new auth comes in.