- Technical Forums
- :
- Switching
- :
- Re: Watchguard to MX100 Migration
Watchguard to MX100 Migration
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Watchguard to MX100 Migration
I've been sort of stumped with this appliance so far. I'm going to line out our current environment and then see what you guys think I need to edit for the replacement of the Watchguard.with the MX100.
We currently have a full Meraki switch environment with a Watchguard XTM taking care of firewall duties.
The full layer 3 switch we call IT Core and have quote a few access switches. The layout is below:
Vlan 1 DataVlan ~ 192.0.0.0/24
Vlan 4 ArborNet ~ 192.168.1.0/21
Vlan 5 DoorCams ~ 192.168.20.0/24
Vlan 6 DoorControls ~ 192.168.24.0/21
Vlan 9 VideoWalls ~ 192.168.100.0/24.
Vlan 10 Voice ~ 10.0.0.0/24
One not here is that Vlan1 and Vlan4 we use as our primary data vlan. Inherited a /24 and ran out of room so created the /21 but can't deprecate the /24 yet so for these two subnets they fully communicate with each other.
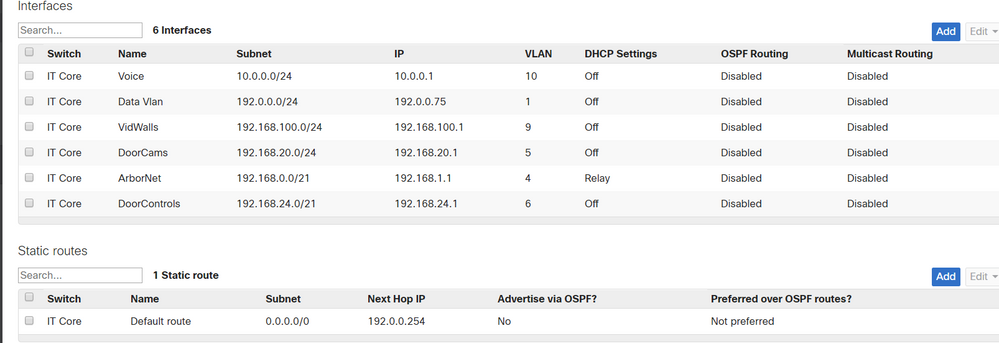
Now currently in the switch (MS 320) is the followig Interfaces and route.
Interfaces ~
DataVlan Subnet - 192.0.0.0/24 IP - 192.0.0.75 Vlan - 1 No DHCP
ArborNet Subnet - 192.168.0.0/21 IP - 192.168.1.1 Vlan - 4 DHCP Relayed
DoorCam Subnet - 192.168.20.0/24 IP - 192.168.20.1 Vlan -5 No DHCP
DoorControls Subnet - 192.168.24.0/21 IP - 192.168.24.1 Vlan - 6 No DHCP
VidWalls Subnet - 192.168.100.0/24 IP - 192.168.100.1 Vlan - 9 No DHCP
Voice Subnet - 10.0.0.0/24 IP - 10.0.0.1 Vlan - 10 No DHCP
Route ~
Default route 0.0.0.0/0 Next Hop IP 192.0.0.254
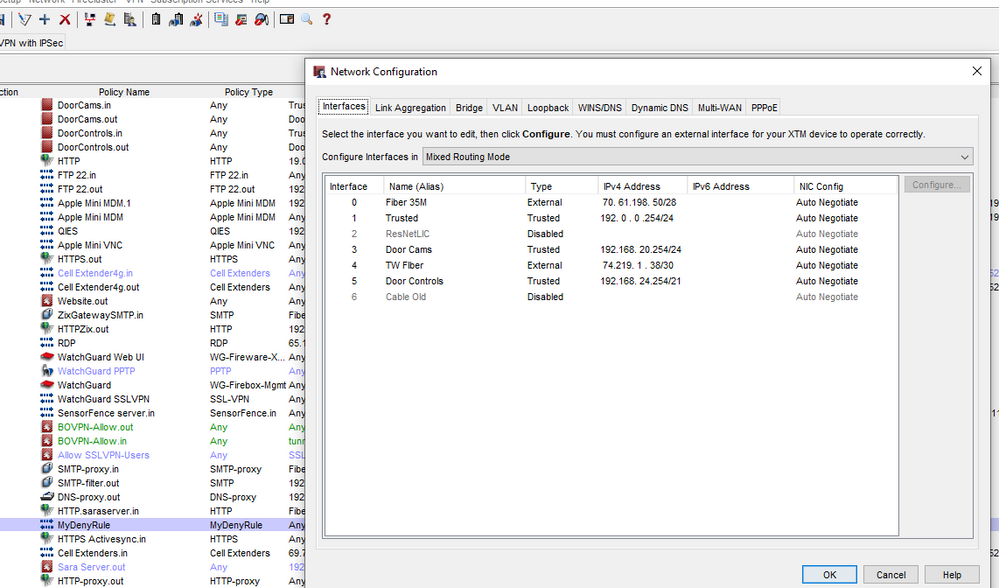
Now the Firebox is much different than the MX is. The Watchguard ports are the interfaces and can be set with hard IPs and what not. Below is the current config of the Watchguard that we use dual fiber WANs on:
Internet external port 0 IP is static from WAN and has our static public IPs
Port 1 is our trusted network ~ IP is 192.0.0.254
Port 3 is for the door cams ~ IP is 192.168.20.254 The firebox also serves as DHCP for this one
Port 4 is the second wan static from ISP
Port 5 is the door controls ~ IP is 192.168.24.254. The firebox also serves as DHCP for this one.
These are the only interfaces on the Watchguard. Also the Watchguard has no vlans programmed into it.
The Watchguard policies control all traffic flow as well as segmenting the Door vlans.
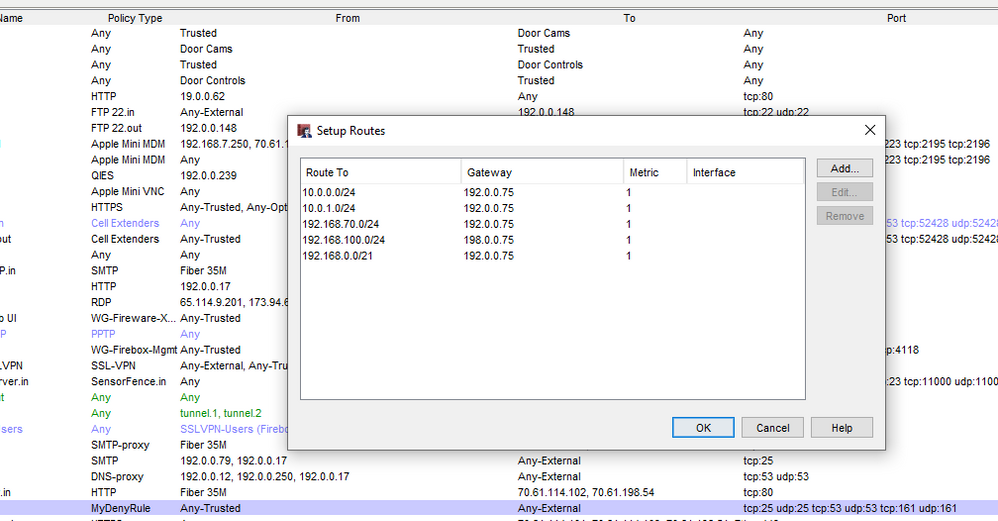
The Watchguard does have the following routes in it:
10.0.0.0/24 routes to Gateway 192.0.0.75
192.168.0.0/21 routes to Gateway 192.0.0.75
192.168.70.0/24 routes to Gateway 192.0.0.75
192.168.100.0/24 routes to Gateway 192.0.0.75
Ok so that pretty much somes it up. The static IPs are programmed in the Watchguard and policies dictate traffic from them.
So I've tried a few different methods of setting up the MX but can't seem to get things down pat. What's the best way to integrate this into the network to replace the Watchguard? Merakis documentation points to a Layer 3 switch topology with Firewall (MX), Distribution Switch (MS320), then downstream Access switches. That sounds like us perfectly but their documentation has an example of creating a dedicated interface that is given a gateway IP but it must be old as when I create an interface on the MS there's no place for a gateway.
So any recommendations on the best way to do this? The switch taking care of the Vlan routing/tagging and the firewall just doing internet traffic is perfect, I just can't seem to get it right.
Thanks for the help!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @cgibson777
"switch taking care of the Vlan routing/tagging and the firewall just doing internet traffic is perfect, I just can't seem to get it right."
If I understand you right.
The requirement is
1. All the VLANs shall reside on the switch
2. MX shall be the gateway for internet access
Possible configuration could be
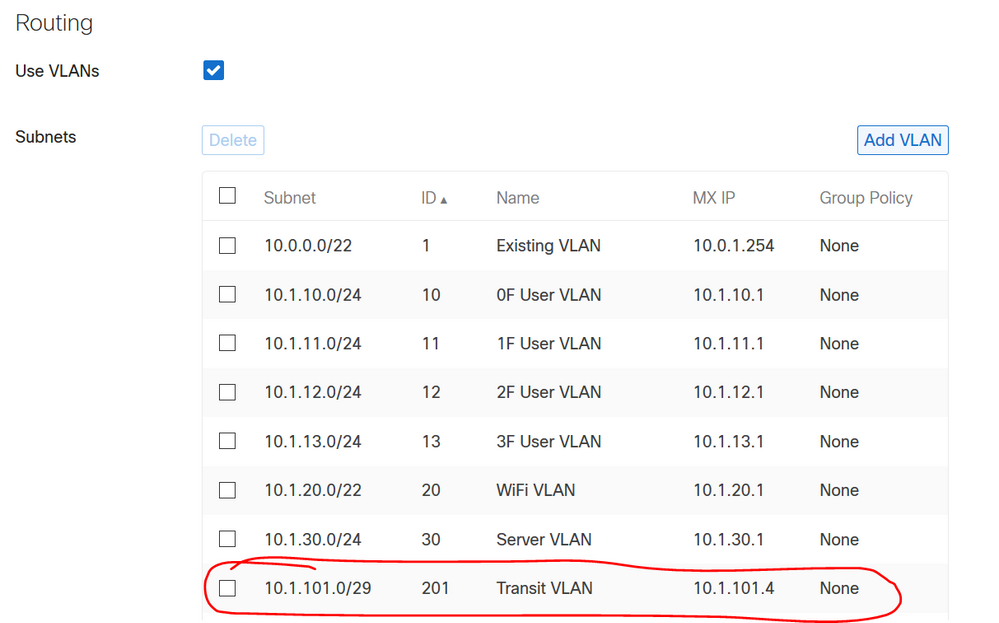
On MX
1. Create a Transit VLAN
Security & SD-WAN > Addressing & VLANs > Routing
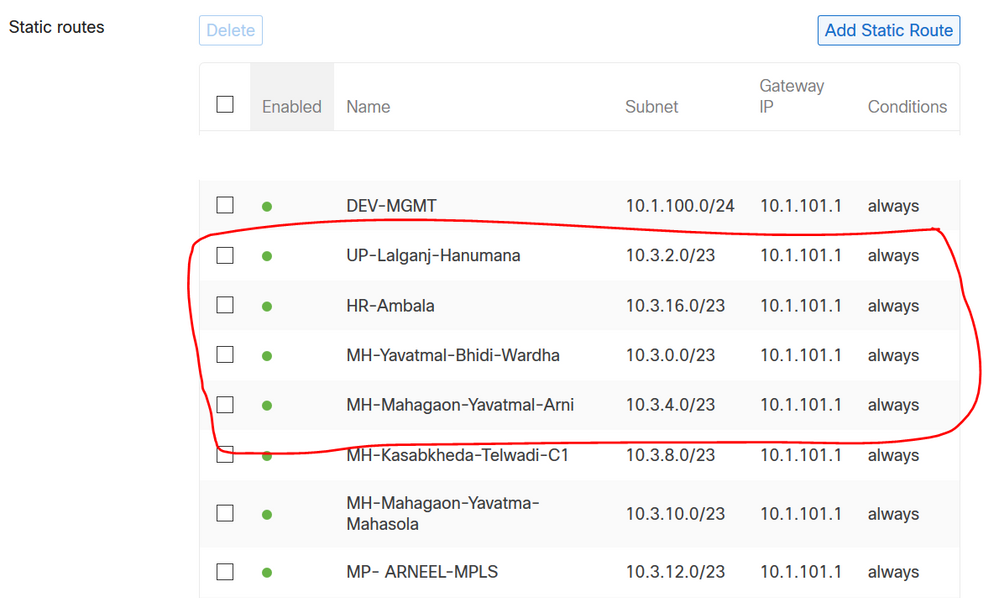
2. Create reverse route for VLANS on the switch
Security & SD-WAN > Addressing & VLANs > Static routes
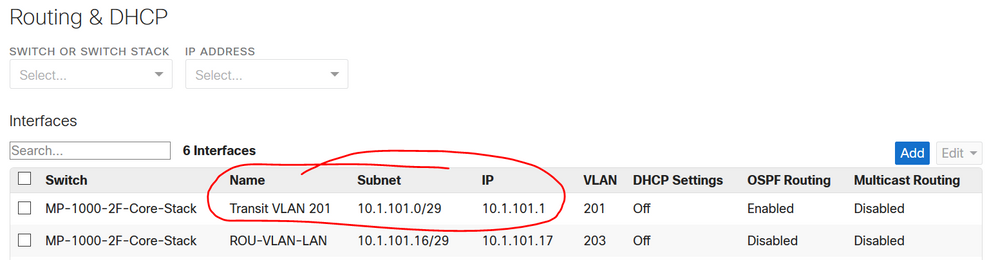
On Switch
1. Create a Transit VLAN
Switch > Routing & DHCP
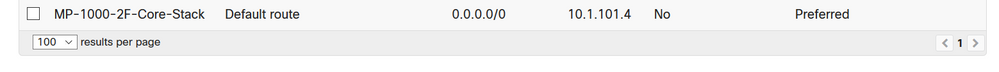
2. Create Default Route towards MX
Switch > Routing & DHCP
Ajit
AjitsNW@gmail.com
www.ajit.network
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Correct, that's the target scenario. So the MX would have the transit vlan created with a route from mx as well as from the switch. I'm assuming in my scenario with a current gateway of 192.0.0.254 on the Watchguard that I would need to tag the MX subnet Vlan 1 with an MX IP of 192.0.0.254 correct?
Thanks for the help!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Also, using your solution as an example I would tag the uplink port as native vlan 201 on the switch and firewall ports or just vlan 1 native? and of course all vlans allowed.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Also, I'm assuming in my scenario the only vlan that would reside on the MX would be the Transit Vlan correct?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
>Vlan 1 DataVlan ~ 192.0.0.0/24
>Vlan 4 ArborNet ~ 192.168.1.0/21
This is not a valid config. The subnets are overlapping.
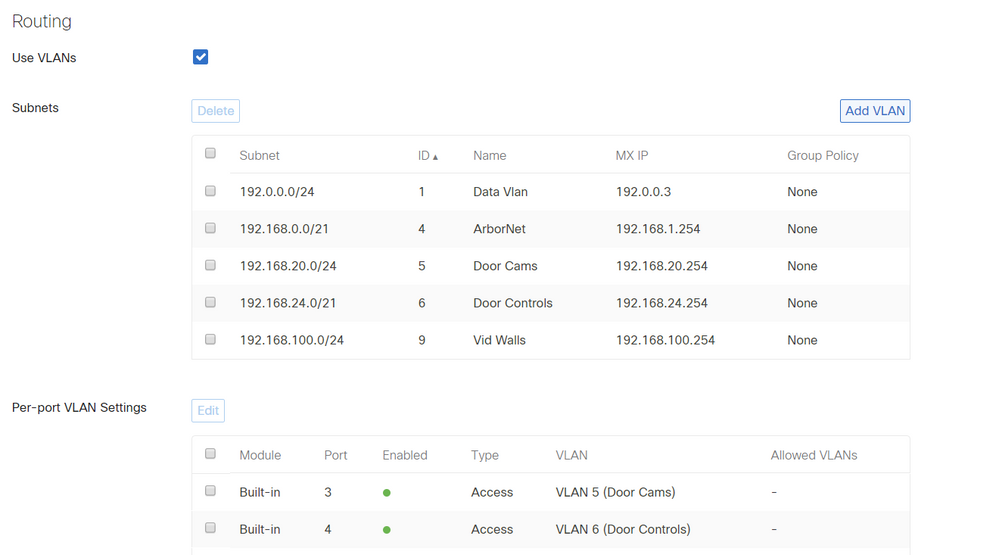
You can configure VLANs on the MX like you have at the moment and then assign them to ports.
So you can make that part work the same if you like.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
That was what I was trying to do in the beginning but couldn't seem to get the static routing to work properly between the MX and the MS320. Create each VLAN on the MX with a corresponding port on the MX, then tagging that port to a corresponding port on the MS. That's essentially how we have it today with the firewall interfaces on the Watchguard and then it has the static routes back to the layer 3 switch. Then it just shoots traffic to the trusted interface to the Watchguard.
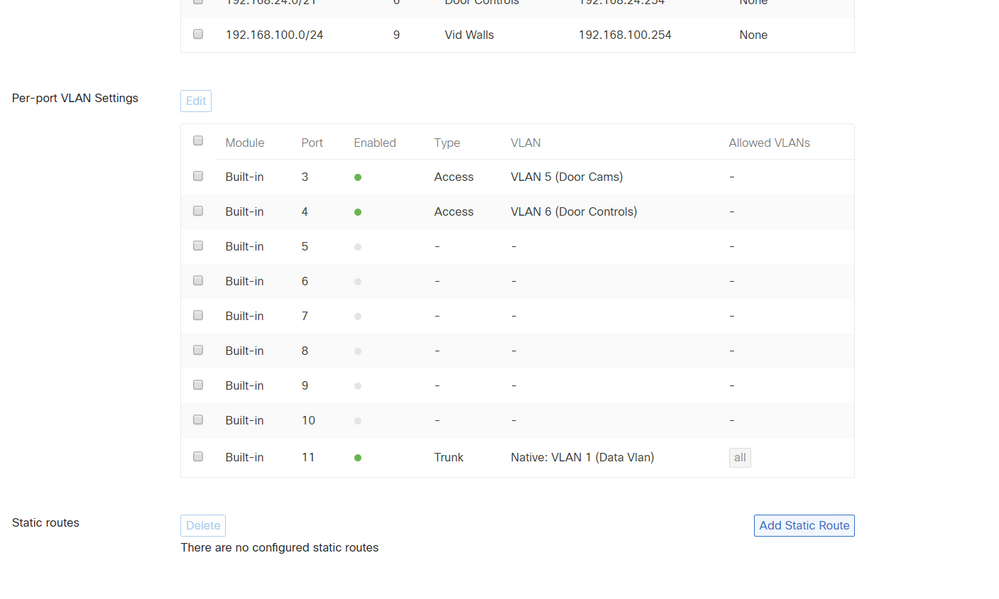
Here's what I have today on the switch (MS320):
Then the firebox has this:
With these routes in the Firebox:
I did these in the MX as a test. I figured I could do the 192.0.0.3 as a test and then when cutover happens change it to 192.0.0.254. Then using a SPF port as an uplink from the switch to the MX with each tagged native VLAN 1 with all vlans. This kind of matches the Watchguard but the static routes are what's throwing me off.
I'm not opposed to restructuring just want to get it right from the get go so to speak.
Thanks for all the help!