We're migrating to the Cisco Community on March 29. The Meraki Community will enter read-only mode starting on March 26.
Learn more- Technical Forums
- :
- Switching
- :
- Re: 802.1x Wired connection with RADIUS server authentication
802.1x Wired connection with RADIUS server authentication
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
802.1x Wired connection with RADIUS server authentication
Hello all,
I hope you be able to assist me because I'm frustrated.
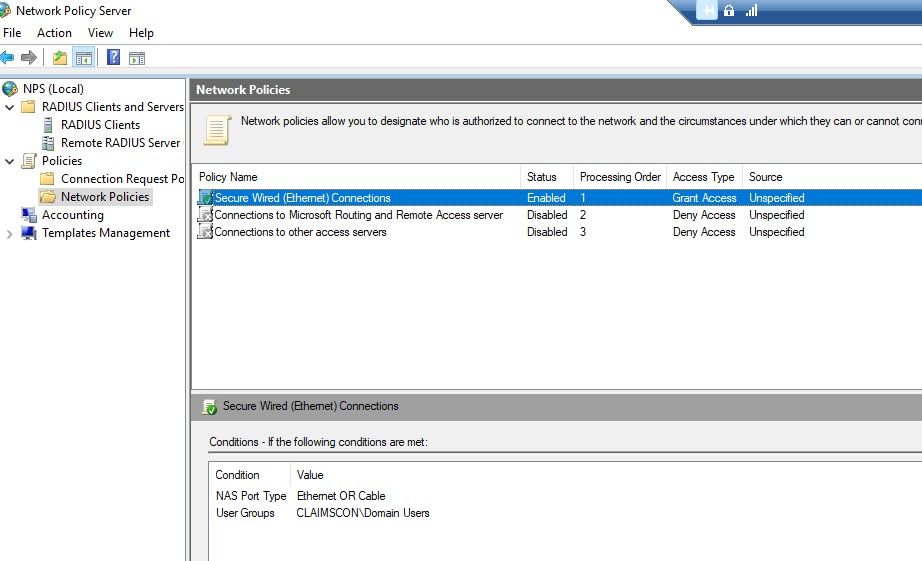
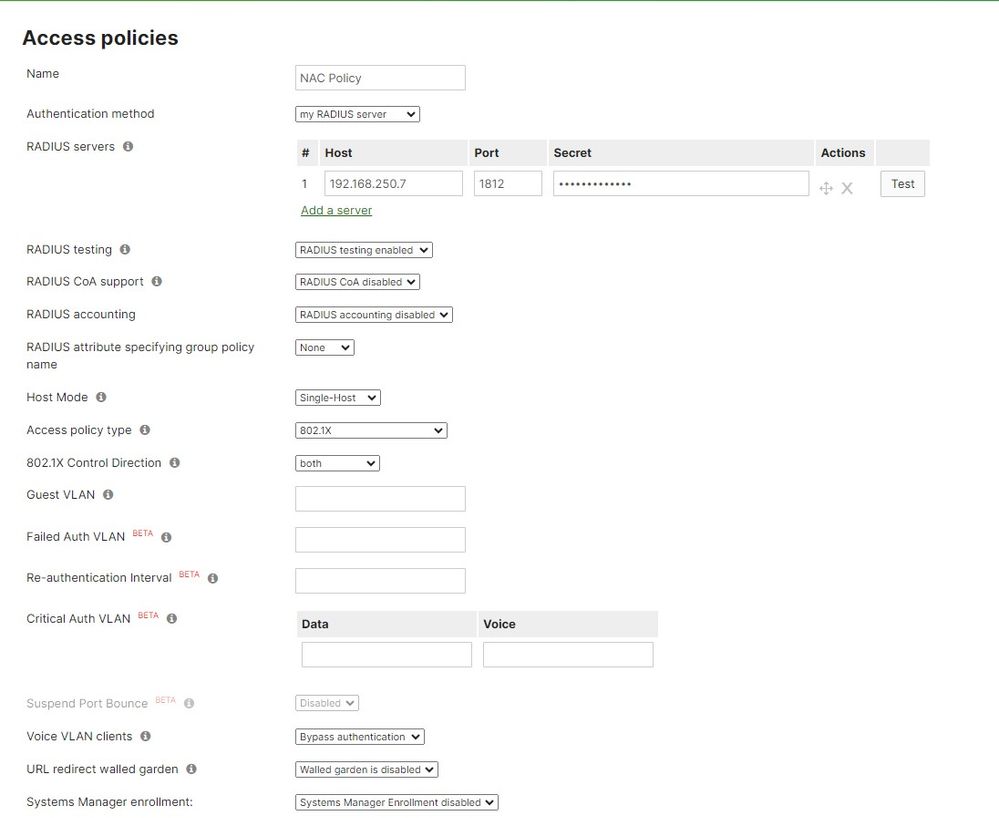
I have 2 Meraki Switches MS-225 for Lan connection only. No vlans. all ports are configured on Vlan 1.
my goal is to authenticate any computer in my organization by user domain group.
I already installed RADIUS server and configured it. its located also on the same network on my Meraki switch.
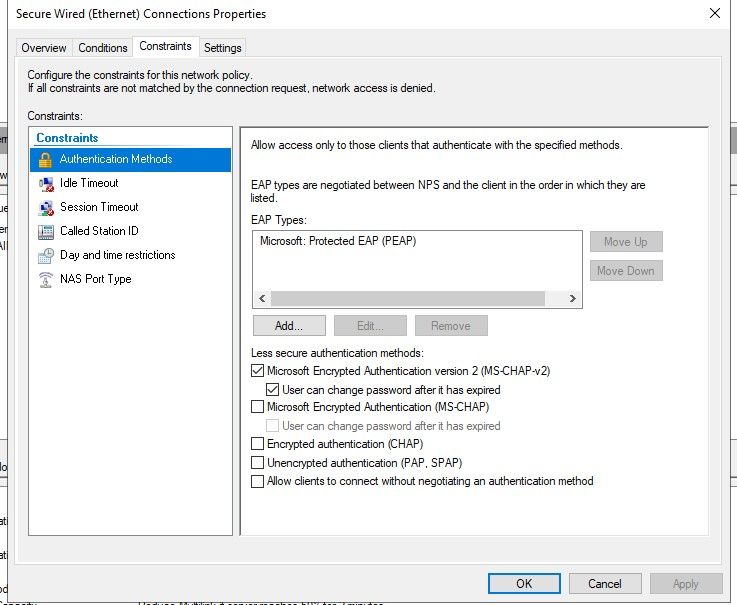
I tried all the authenticated methods I have in the NPS but non of them works for me.
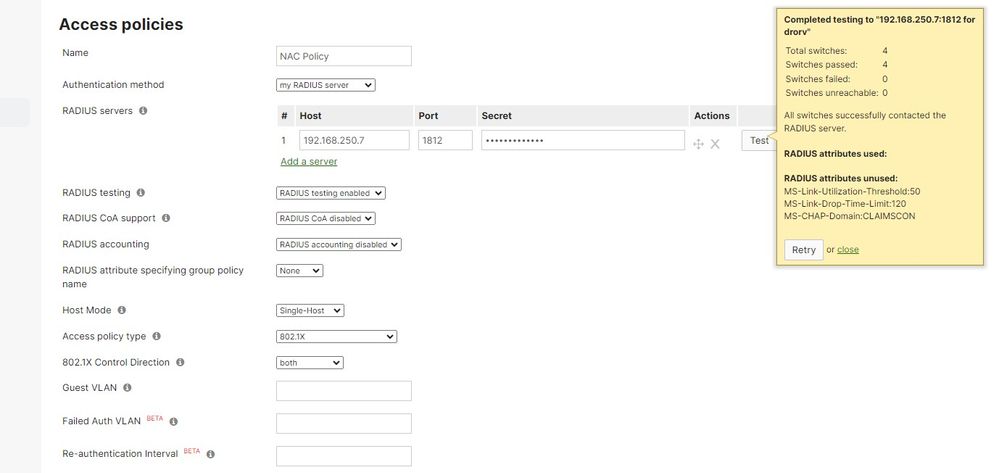
Test connectivity to the RADIUS server is working fine to all 4 Meraki switches.
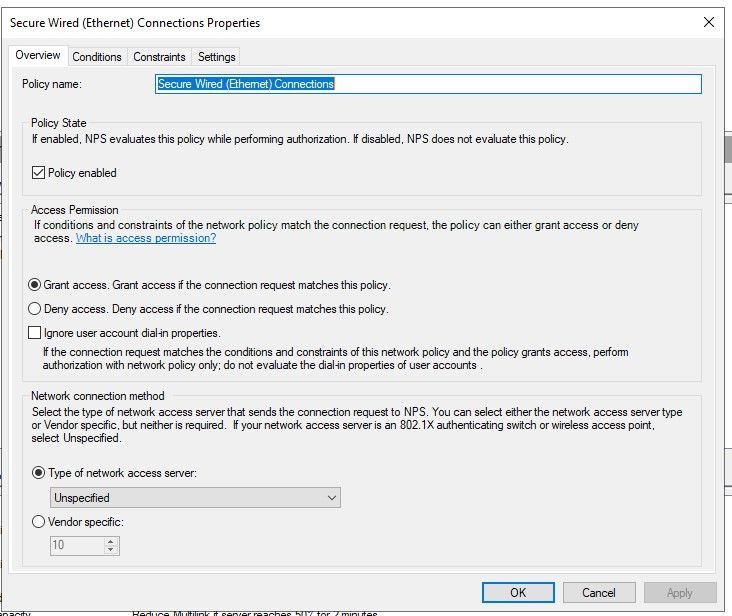
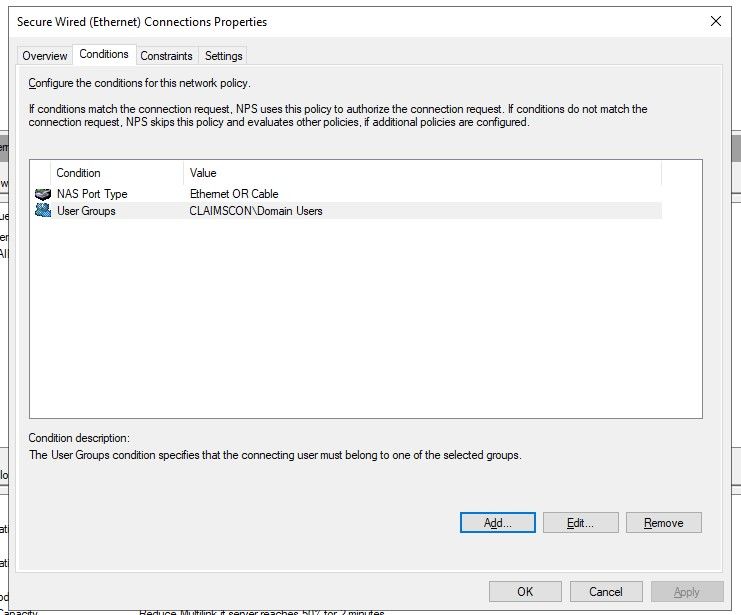
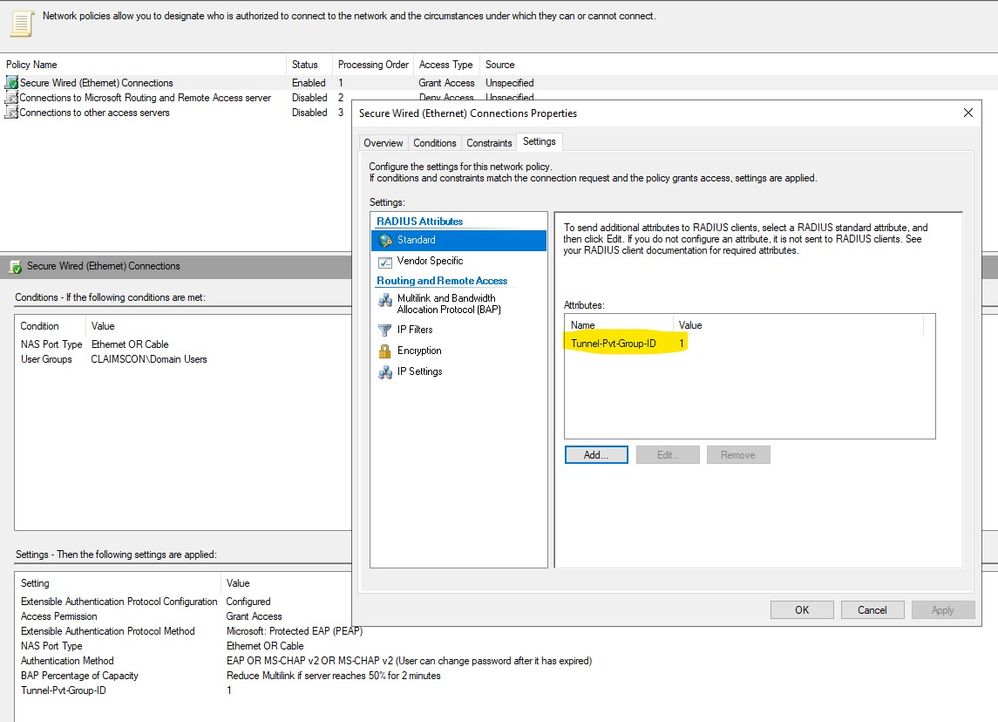
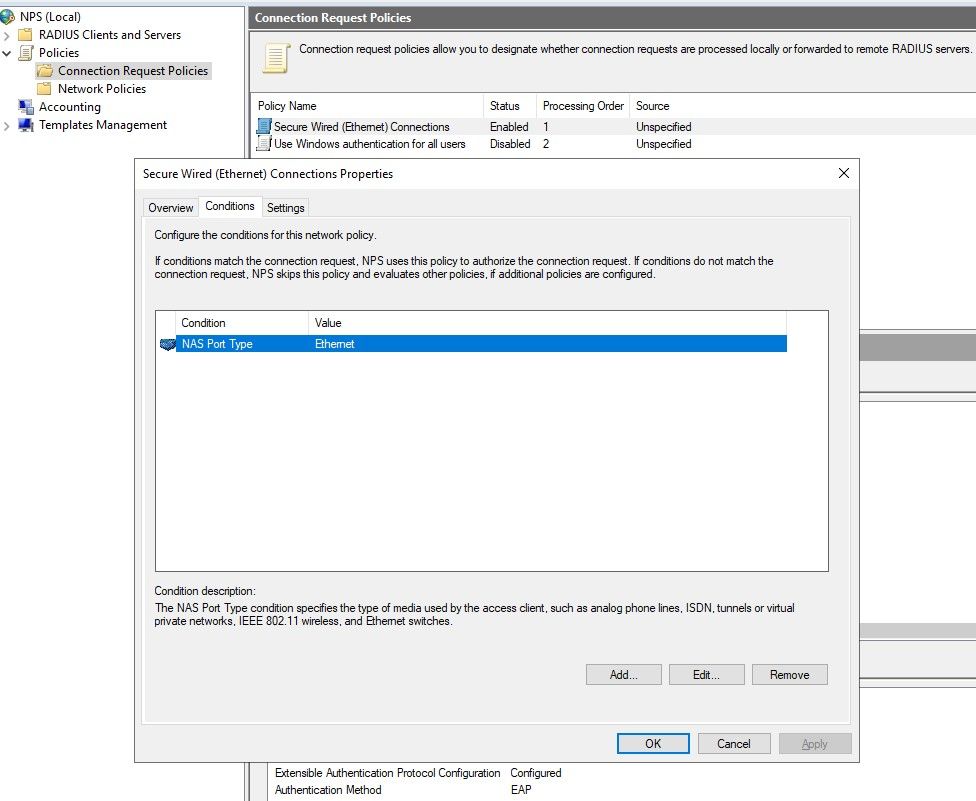
Currently my conditions are NAS Port Type Ethernet or cable along with Domain users User Groups.
Authentication method is Microsoft: Protected EAP (PEAP).
Not sure if i select domain user group , how is the RADIUS server authenticate it ? by user creds or do I need to validates the users with certificate as well?
The problem is , once i assign the Access Policy to any port its getting red and lost connection to the client computer.
Please help me, what is the exact configuration I need to set on the RADIUS/NPS server ??
Thanks in advanced.
Dror
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Check the documentation.
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
Thanks for you reply.
Yes, I tried all these docs from Meraki but unfortunatly its not helps me.
I preaty sure I need to set the right configurations on the NPS side but so far nothing works for me.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Have you checked the NPS logs?
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
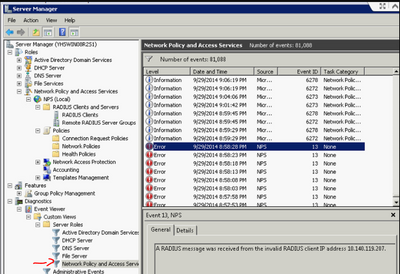
I could find logs only in Event viewer but not something i could point on.
The thing is that I need to know which uthenticated method should i use for domain user authentication.
Is there other place to see NPS logs?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Check which Connection Request policy/Network policy is matching.
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
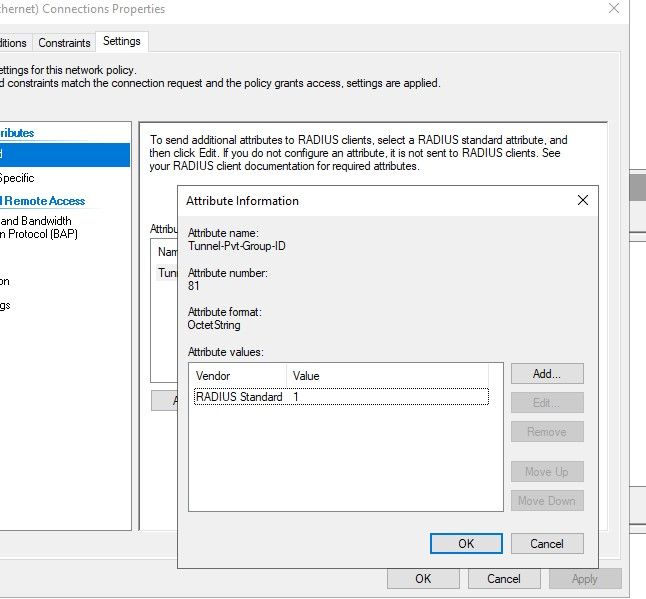
You need to send the radius attribute Tunnel-Pvt-Group-ID with the VLan ID when the user authenticates.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
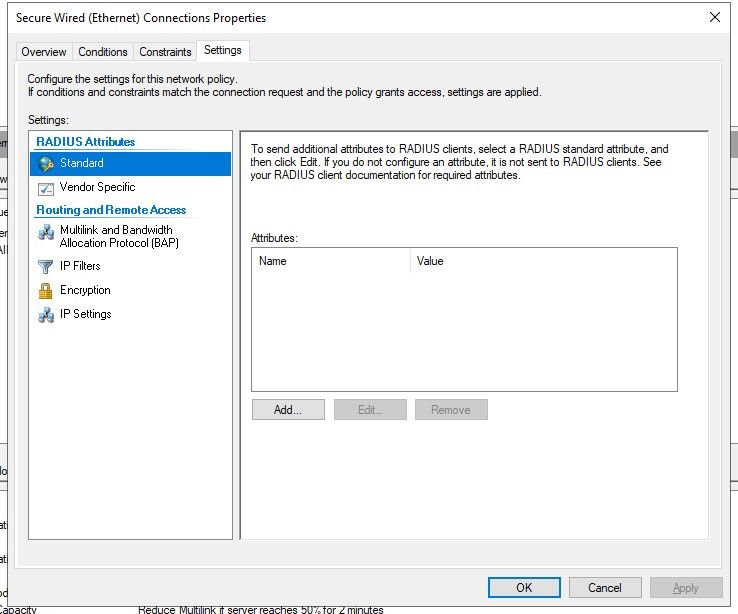
You mean like this ?
the port has disabled again after this change.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
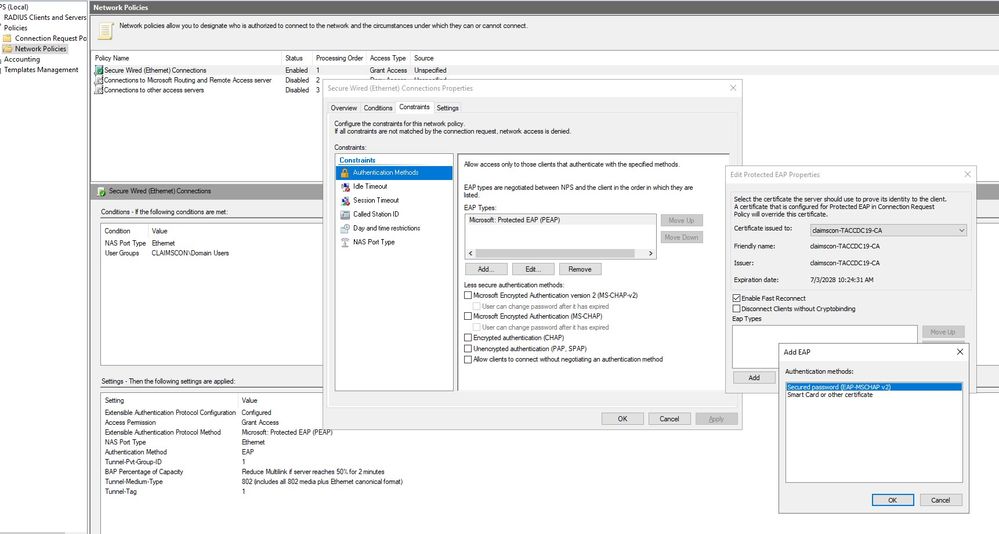
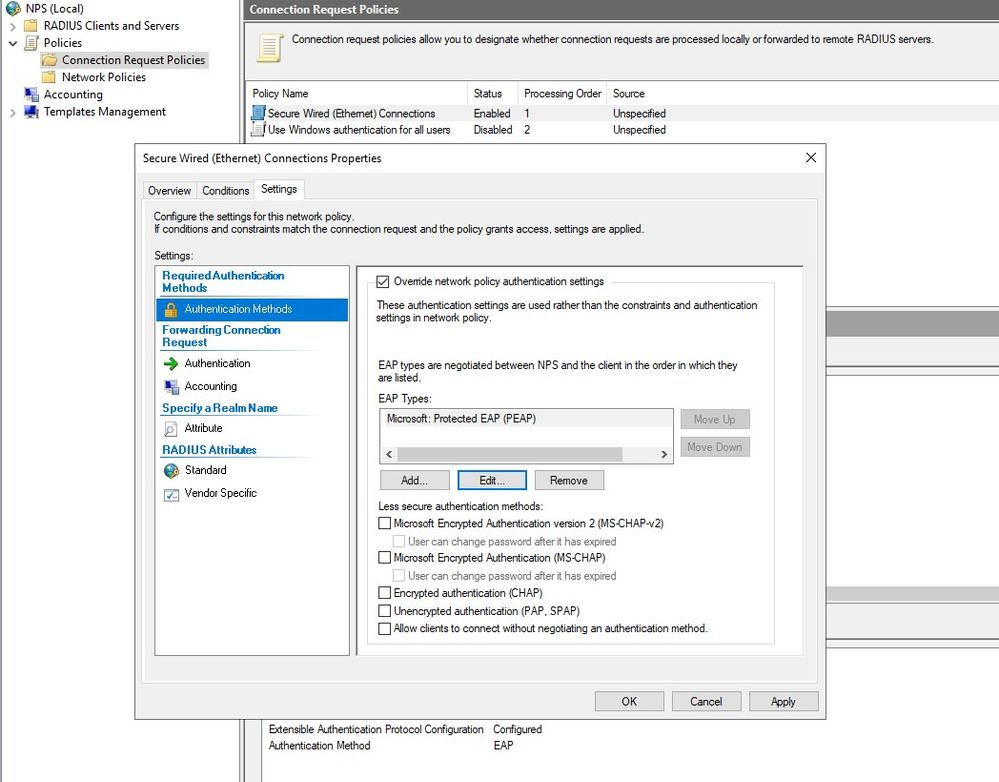
Did you edit the PEAP EAP type to set the inner Authentication method? That is not the MSCHAPv2 that is shown below that box. It has to be configured inside the PEAP config.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I've removed the inside MSCHAPv2. Port still disabled.😕
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Check which Connection Request policy/Network policy is matching on logs.
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
WHAT did you remove? You have to make sure to have the right inner method.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
And what are they ?
these my current Authentication methods:
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Likely the "Secure Password". Did you add it?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
it was there before. it didnt help. port still get disable
if you sure it has to be there i will add it back.
Do I need to use any certificate in order to authenticate the users ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The certificate shown in NPS must be trusted on the end devices.
You really should get a consultant to help you. 802.1X is one of the most complex topics and is especially hard with NPS.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
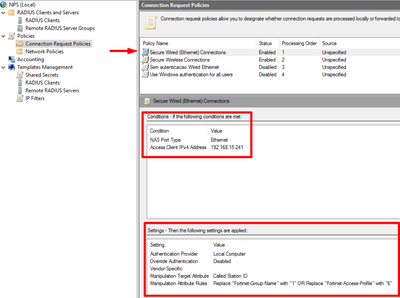
Guys the problem is that it's not matching with any connection policy.
It's very common, create a new connection policy with the the same configuration that you create in the network policy.
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I dont have User Group under connection request policy like I have in Network Policy
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I don't remember exactly what the config should look like, but this might help.
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I tried many consultants before i posted here. 😉
Where can i see the certificate in the NPS ? Couldnt find it.
Thanks
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Really? Don't have a certificate installed? You need an MS Windows server expert.
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
OK but non of the logs i get says something about certificate..
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This is the basics of 802.1x.
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
If the connection request policies are messed up, it doesn't even get to the point where the certificates are relevant. When looking at the screenshot above, it seems that you assigned the root cert to the NPS. Let's say this is as least "unconventional".
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Any change on NPS configuration bring a different logs. I dont know what are the right configuration i need to set.
this is the latest logs I've received:
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You need to create a connection request policy.
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
sure but i already have one configured.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
s there any configuration needed to do on the endpoint ? NIC configurations?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
🤔https://www.virtualizationhowto.com/2018/12/configure-windows-10-for-802-1x-user-authentication/
Please, if this post was useful, leave your kudos and mark it as solved.