- Technical Forums
- :
- Security & SD-WAN
- :
- Re: VPN Ip adresses range
VPN Ip adresses range
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
VPN Ip adresses range
My main subnet is 10.69.11.0/24 and my DHCP is off since we have a Windows DHCP server.
In my asa 5505, I had a vpn setup and the vpn clients used to get a DHCP IP in the range 10.69.11.220-10.69.11.253 from the ASA.
Where can I setup thin in the meraki?
Thank you
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The subnet is set at the clientvpn option itself. Dhcp is provided from the mx
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I don't understand your answer.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
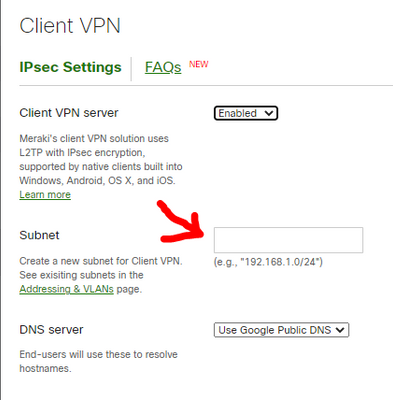
@Alain_Bensimon in the dashboard go to Security & SD-WAN - Client VPN and enable the VPN, the setting is here:
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
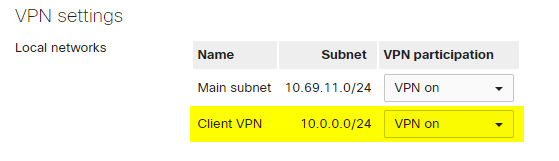
Currently I have this:
and this
I would like the VPN clients to get IP's within my main subnet.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @Alain_Bensimon I don't think that is possible, the subnets need to be different to be routable
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
so what are my options?
I absolutely need VPN clients to get IP's within that range because we have a site to site VPN to access some programs that are located on another site, and if clients are out of that range, they are denied of entry.
Is it possible to disable the VPN client subnet and get IP's from our Windows DHCP server that already assign IP's to our local clients?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@Alain_Bensimon you could divide the existing LAN subnet in two and have half for the LAN and half for the VPN clients i.e. LAN has 10.69.11.0/25 and VPN has 10.69.11.128/25, or you could ask the other site owner to permit an extra subnet and use that for the VPN.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@cmr I thought about that, but then they will be on another vlan, and the VPN clients won't have access to the local ressources of our main Lan.
Is there any way that the meraki does not assign IP adresses to the VPN clients and let my Windows DHCP server take care of it?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I don't think so, I cannot think of any modern firewalls that allow that feature.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The ASA can provide the VPN addresses via DHCP.
back to topic: Why shouldn’t. systems on the main LAN not be able to communicate with VPN clients on a different LAN? For sure that works.
-
3rd Party VPN
166 -
ACLs
100 -
Auto VPN
312 -
AWS
38 -
Azure
70 -
Client VPN
427 -
Firewall
697 -
Other
583