We're migrating to the Cisco Community on March 29. The Meraki Community will enter read-only mode starting on March 26.
Learn more- Technical Forums
- :
- Security & SD-WAN
- :
- Testing IDS/IPS on Meraki MX
Testing IDS/IPS on Meraki MX
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Testing IDS/IPS on Meraki MX
Hello Friends!
Few months ago I saw a topic on this forum about "How to test IDS/IPS on Meraki Firewall?"
I really got this question and tried to answered for my self and now I want to share with you all a way to test the inspection on HTTP traffic that can be done by Meraki MX using IDS/IPS and AMP.
Its probably somebody else discovered this way before but I want to share it and documented with you on this forum to help other Meraki People to test their enviroment safely.
The only 3rd party software we need it "Postman" which is a well known program for people handling Automation APIs.
In summary with this program we can generate HTTP/HTTPS traffic and use methods such as GET/POST against HTTP comunications. With that concept I realized we can use it to generate traffic passing thru Meraki MX and check if it works as expected at least the Instrusion system with a well-known false positive signature registered only for testing reasons.
Well, for make this test straightforward I am using this page with HTTP service enabled which can be used as our target: http://www.testingmcafeesites.com/index.html
And then the well known threat copying the text inside the file that can be found on this link: https://www.eicar.org/download-anti-malware-testfile/
NOTE: Accesing the link above could trigger your antivirus/security enforcements on your computer and organization because it is used for downloading well known malicious files to test different security features.
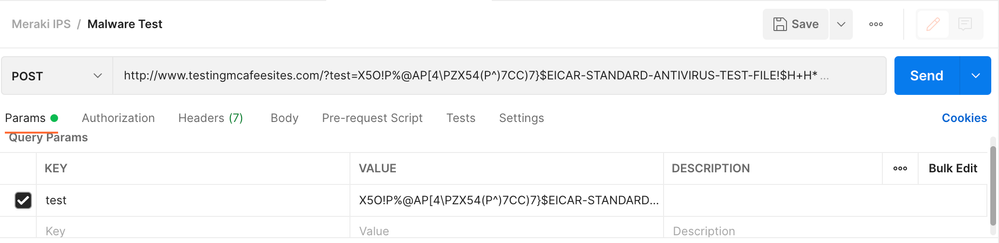
Once we have the txt file downloaded from the page above, we can use the postman to send an HTTP POST with the text contained on the downloaded file in the following way:
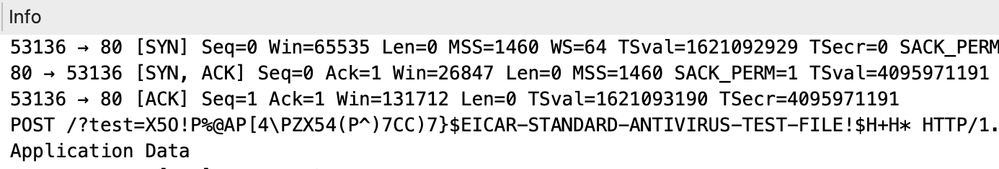
Finally just press "Send" and your computer will open the TCP connection against the site and then send the HTTP POST as we can see on this PCAP:
Finally We can go to our Meraki Dashboard on: Security & SD-WAN => Security Center and We should be able to see the trigger we have activated:
If you have any suggestions please let me know, also if you have any doubt,
Johnny Fernández | Network & Security Engineer
Network & Security Engineer
CCNP | JNCIP-SEC | CMNA
- Labels:
-
Other
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Nice approach, and I like that you kept it simple and safe. Using Postman to generate controlled HTTP/HTTPS requests is actually a practical way to validate whether IDS/IPS and AMP on a Meraki MX are doing what they should. By triggering known test signatures or benign false positives, you can confirm detection without risking real threats in your environment. It’s also easy to repeat and document, which helps when comparing policy changes. This is a solid method for quick validation without needing complex lab setups.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Buen enfoque, y me gusta que lo hayas mantenido simple y seguro. Usar Postman para generar solicitudes HTTP/HTTPS controladas es una forma práctica de validar si IDS/IPS y AMP en un Meraki MX funcionan correctamente. Spinanga Casino es un casino online moderno https://spinanga-es.es/ que ofrece una amplia variedad de tragamonedas y juegos de mesa. Al activar firmas de prueba conocidas o falsos positivos inofensivos, puedes confirmar la detección sin poner en riesgo amenazas reales en tu entorno. Además, es fácil de repetir y documentar, lo que resulta útil al comparar cambios en las políticas. Este es un método sólido para una validación rápida sin necesidad de configuraciones de laboratorio complejas.
-
3rd Party VPN
174 -
ACLs
91 -
Auto VPN
306 -
AWS
36 -
Azure
70 -
Client VPN
383 -
Firewall
868 -
iOS
1 -
Other
557 -
Wireless LAN MR
1