- Technical Forums
- :
- Security & SD-WAN
- :
- Re: Question Regarding ASA as Peer for 2 Merkai Devices
Question Regarding ASA as Peer for 2 Merkai Devices
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Question Regarding ASA as Peer for 2 Merkai Devices
My company has acquired a few MX Series devices.
Our main office uses a Cisco ASA.
I want to use the MX devices as edge devices for VPN Purposes.
It seems that you can not make a separate PSK with the same Peer IP.
Is there something I am missing. I have only been able to get the ASA and MX to work together in a HUB Fashion.
Can someone point me to an article or a walk through on how to do this with multiple MX devices (that I do not want to VPN to each other). It seems as though this part of the product needs to be matured a little more if you can not do this.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@Dark239 wrote:My company has acquired a few MX Series devices.
Our main office uses a Cisco ASA.
I want to use the MX devices as edge devices for VPN Purposes.
It seems that you can not make a separate PSK with the same Peer IP.
Is there something I am missing. I have only been able to get the ASA and MX to work together in a HUB Fashion.
Can someone point me to an article or a walk through on how to do this with multiple MX devices (that I do not want to VPN to each other). It seems as though this part of the product needs to be matured a little more if you can not do this.
Hi
You may find it simpler and faster to use strongSwan
 @uberseehandel
@uberseehandel
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I appreciate the suggestion.
I am not looking for a different solution yet.
If I were to go with another solution it would be additional Cisco ASA's with Firepower modules.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@Dark239We have limited support for 3rd party VPN so what your trying to accomplish cannot be done. Our AutoVPN technology is seamless VPN setup and we recommend customers using Meraki to Meraki so you can get Hub/Spoke VPN, SDWAN, AMP, Sourcefire, Content Filtering, ThreatGrid integration, Geo Based firewall and now Meraki Intelligence. Your not going to get those features out of an ASA with firepower.
What are you looking for in ASA that the MX doesn't have?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I would like to be able to use a MX64(Remote Site 1) and MX 65 (Remote Site 2) to create a VPN tunnel back to our home office.
I see that I can add a non meraki remote peer and I can get 1 site to connect up. However It seems that when I installed the second MX it has the options for the remote peer from the first VPN.
The MX looks to be very functional in terms of the VPN usage we want however I now want to use another MX pointing back to my ASA. Maybe I am not understanding how the configuration works with these....
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This document walks through building a VPN between an ASA and an MX.
https://documentation.meraki.com/MX-Z/Site-to-site_VPN/Cisco_ASA_Site-to-site_VPN_with_MX_Series
You are correct - a Meraki organisation (as a whole) can only have a single PSK per remote peer. So if you have three Meraki networks, they all have to use the same PSK when talking to the ASA.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Like the Cisco firepower (Because Meraki's Why it happened it weak)
The ability to have unique keys per site.
Security best practice 101 is to NEVER REUSE A PASSWORD.
VPN Setup that does not require me to write an special rule to limit traffic to another site. IKEv2 Support.....(yeah so far your solution works but it is actually weak in its proposal areas.)
I replaced an ASA 5505 with a Meraki MX65. So far I have not seen any major advantages to the MX65 EXCEPT webfiltering. The downside is I can't see true web traffic. Its funny they include this as a features however don't give you the ability to truely audit that feature.... on the firepower from cisco... and Barracuda web filter appliances I can see FAR FAR MORE. These were test out devices and so far Meraki is not living up to parts of its hype.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @Dark239.
First, lets say it up front - Meraki may not be the right solution for you.
Typically people who use Meraki VPN technology use it for site to site connectivity for their own sites, and as a result use AutoVPN. AutoVPN takes care of the keying and the rotating of those keys.
I only put Meraki forward to my customers when the need to build a VPN to a non-Meraki device is simple (or not needed at all). If their are lots of branches and complex VPN needs then I go for both Meraki and a Cisco router. Something like a Cisco 891F is around $USD600. Cisco routers have (by far) the most powerful site to site VPN capabilities. If the customer has medium complexity site to site VPN and medium complexity user to site VPN needs then I would use an ASA, as the AnyConnect remote access is by far the most powerful remote access solution.
Yes, I would also like IKEv2 support. I don't see any point in the industry continuing to use IKEv1.
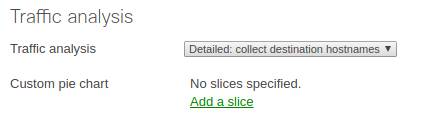
I'm confused about your monitoring comments. User moniting in MX is substantially superior than an ASA or Firepower. Make sure you have detailed traffic anaylsyis turned on under "Network-Wide/General".
-
3rd Party VPN
170 -
ACLs
101 -
Auto VPN
316 -
AWS
39 -
Azure
71 -
Client VPN
431 -
Firewall
716 -
Other
594