- Technical Forums
- :
- Security & SD-WAN
- :
- Packet Capture for IDS matches - Inspect Packet not available
Packet Capture for IDS matches - Inspect Packet not available
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Packet Capture for IDS matches - Inspect Packet not available
Related to this thread - https://community.meraki.com/t5/Security-SD-WAN/Packet-Capture-for-IDS-matches/m-p/141960
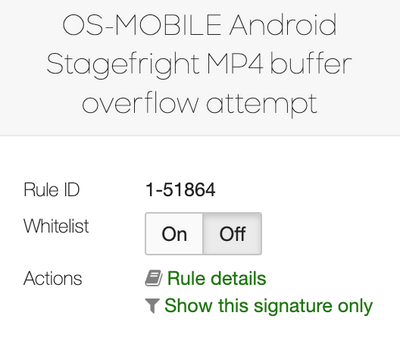
When I am looking at Security Center -> MX Events and choosing an event from today, I do not get an Inspect Packet option. I thought this was previously available. Was that option removed?
Example options from MX Events tab:
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @sec_eng_owl
Thanks for bringing this one up. Just checked my Lab Mx which is on Fw 16:16. I get the same results as you in that I can’t see the inspect packet element.
Just checked a customers network, same firmware, I can see the inspect packet element.
What MX do you have and what license are you running? Ie Enterprise Sec, Advanced Sec or Secure SS-WAN plus?
https://www.linkedin.com/in/darrenoconnor/
I'm not an employee of Cisco/Meraki. My posts are based on Meraki best practice and what has worked for me in the field.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
We are on 16.16, not sure about the license.
I checked all our devices and tried a few different snort signatures on each, and I found an egress suspicious TLD query signature that let me inspect it. Other signatures on the same device did not have the option. Why does it vary per signature?
Also the Source column in the MX Events table shows a tiny "Meraki Network OS" under the hostname for signatures that I can inspect too, if that is of any help.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Just went to the customers dashboard where I could see the inspect packet report. Even seems hit and miss there also. Out of multiple events I could only see one which gave me the inspect packet option
https://www.linkedin.com/in/darrenoconnor/
I'm not an employee of Cisco/Meraki. My posts are based on Meraki best practice and what has worked for me in the field.
-
3rd Party VPN
168 -
ACLs
101 -
Auto VPN
313 -
AWS
38 -
Azure
70 -
Client VPN
428 -
Firewall
704 -
Other
591