We're migrating to the Cisco Community on March 31. The Meraki Community will enter read-only mode starting on March 26 through March 31.
Learn more- Technical Forums
- :
- Security & SD-WAN
- :
- Non-Meraki VPN peer + Meraki autoVPN - routing
Non-Meraki VPN peer + Meraki autoVPN - routing
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Non-Meraki VPN peer + Meraki autoVPN - routing
Hi!
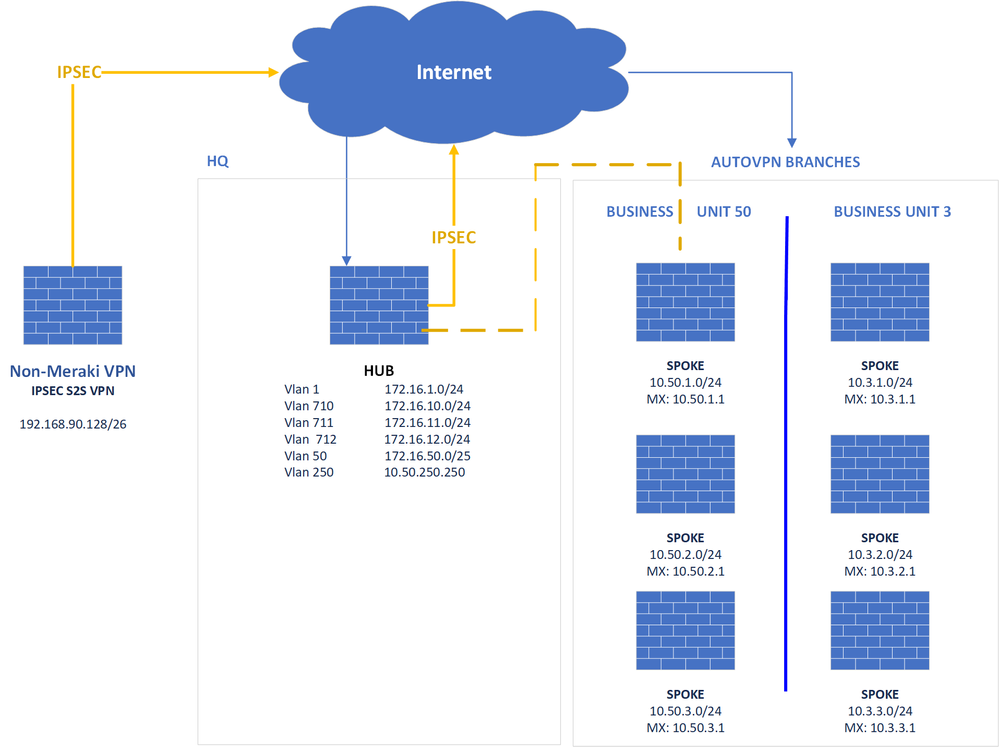
At our company we are using MX appliances for the HQ and the braches. The branches are divided in two business units. Business unit 50 and 3 with there own unique private subnets. The branches are the SPOKE's and at the HQ the MX is set-up as HUB.
Now! For an external web services application i need to setup a IPSEC Site-2-Site with Non-Meraki VPN peer. This web services application is only needed for users at the HQ and business unit 50 (about 30 spokes).
I managed to build the IPSEC to the HQ MX HUB, and i am able to ping the Non-Meraki VPN subnet, but i am unable to reach the Non-Meraki VPN at the spokes. Its just not routing the IPsec VPN traffic. I have attached a diagram of our setup. Could you please help to find a solution for this.
Thank in advance.
Arnout
- Labels:
-
Auto VPN
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You can't do that. You will also need to build the non-Meraki VPN to each spoke.
You may find it easier to buy an additional MX and host it where ever the web services application is (if they will allow it).
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Dear Philip
Is the above solution still the only valid one or there is any better workaround without extra MX appliance?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
>Is the above solution still the only valid one
Correct.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello,if my network is like this what settings should i do on my newly installed meraki device?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Are you able to install your new MX at the cloud provider?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I have opened a new dashboard and it is installed.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Another solution is to buy an additional MX to go at the hub site, but place it in a different organisation. This should go on the same LAN as your existing hub MX.
On the new MX add a static route pointing to your AutoVPN MX that covers all of your subnets. On your AutoVPN MX add a static route pointing to the remote site to site VPN destination with the new MX as the next hop, and publish this static route into AutoVPN.
Then build the site to site VPN to the new MX.
Voila. All your spokes now have access.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Philip,
Thanks for your response and help :).
I think the solution with the additional MX sounds the best and easiest way.
But one question, why should this MX run in a different organisation?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
>But one question, why should this MX run in a different organisation?
You are going to have to make the new MX an AutoVPN hub (it wont have any spokes) to enable the non-Meraki site to site VPN. You wont be able to add a static route pointing to the AutoVPN spokes via the other proper hub. It wont allow it to be added.
Actually, if you get the supernetting correct it may be possible, but it would be safer to put it into another organisation.
Actually, this article by Aaron Willette explains it really well.
http://www.willette.works/merging-meraki-vpns/
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
I'm currently setting the below up with a new MX. Just to check should the Non Meraki VPN MX have a separate public IP address from the Meraki AutoVPN MX?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
If they are two seperate MX units then yes, they should each have their own public WAN IP address.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Since the spokes have a default route back to the hub and the hub have the routes to the non Meraki VPN networks, shouldn't the spoke traffic have reachability to the non Meraki VPN networks?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I currently have this situation, does MX 18.107.2 still have this Meraki VPN - Non Meraki VPN routing limitation?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes. That won't be changing.
-
3rd Party VPN
174 -
ACLs
91 -
Auto VPN
306 -
AWS
36 -
Azure
70 -
Client VPN
383 -
Firewall
868 -
iOS
1 -
Other
557 -
Wireless LAN MR
1