- Technical Forums
- :
- Security & SD-WAN
- :
- MX67, ISE 2.7 and MAB
MX67, ISE 2.7 and MAB
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
MX67, ISE 2.7 and MAB
Guys, this should be a simple problem, if I could just find the right documentation!
I have a Meraki MX67, with a site-to-site VPN linking to a hub Meraki MX84 HA pair. I have client PCs successfully doing IEEE802.1x authentication on the MX67, using an ISE (v2.7) in the network at the MX84 end, so I know both ends work fine.
However, the user wants to authenticate devices with no supplicant, so needs to use MAB. The MX67 has an option to use MAB, but it fails (reject) despite the devices being configured in the ISE.
Other documentation I've found says that the ISE is looking for the "call-check" attribute when authenticating, but the MX67 doesn't provide it. As a result, the MAB fails, and indeed I can see failure notiifcations in the log and the traffic in the packet trace.
So I need to stop the ISE looking for the "call-check" attribute from the devices MAB-ing on the MX67, but I can't find anything that tells me how to do that or if its possible. Yes, I know it would be better to trunk a switch to the MX67 and do "normal" MAB on a "normal" switch port, that was my original response, but apparently a switch won't fit the budget.
If there is any document that says how to do it, can I have a link, or some idea of how to do the job. It sounds like just switching something off....?
Any hints will be gratefully recieved!
Thanks
Jim
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
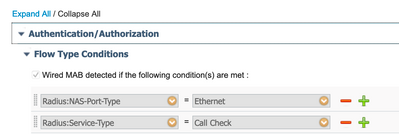
This is part of the "Network Device Profiles" where the ISE has the infos how to do AuthC, AuthZ, if CoA is supported, how VLANs are set and so on.
This is what is used if you use the Network Device Profile "Cisco":
At the moment I don't know which attribute can be used for Wired MAB on the MX.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
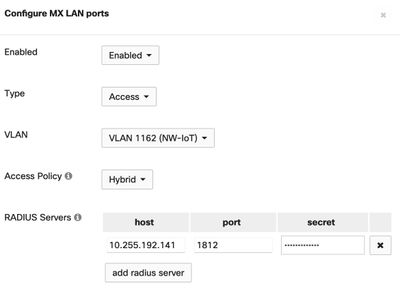
I did some tests with my MX64W and this is what works:
The MX Port-Setting:
The ISE Authentication policy:
First rule matches on MAB, second rule matches on 802.1X for both wired and also my SSID "MX-TEST-EAP". The last rule matches on the client-VPN.
Actually, I don't really like how it's implemented. The MX is quite limited for this kind of konfig.
It doesn't even apply the returned VLAN to the session. For a pure Home-Office environment I could think about using this, but not anything more complex.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Now I'm gonna move the goalposts, sorry.....its been suggested that I could use the inbuilt MAC capabilities of the MX to do what I need, so create a firewall rule to block everything, apply that, then use a client rule to whitelist the clients by MAC address. That should work OK, but I believe setting the firewall deny-all rule will prevent the existing ports on dot1x from working. That being the case, I will have to whitelist all devices and can't use dot1x even for the devices upobn which it works.
Is the situation as I describe, or have I misunderstood something
Thanks
Jim
-
3rd Party VPN
170 -
ACLs
101 -
Auto VPN
317 -
AWS
39 -
Azure
71 -
Client VPN
431 -
Firewall
721 -
Other
597