- Technical Forums
- :
- Security & SD-WAN
- :
- Re: Lot of IDS Alerts allowed. What am i doing?
Lot of IDS Alerts allowed. What am i doing?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Lot of IDS Alerts allowed. What am i doing?
Having from today lot of IDS allerts which allowed over my meraki
Till yesterday , meraki blocked sereral times a malware the following malware came from an external ip
From today i have the following problems and the action on mx events page says "allowed"
First of all on lot of events my server appeared as a source and and an ip on Germany appeared as a destination
All the details for the above events says about a cryptocurrency miner ...for example
Cryptocurrency Miner outbound connection attempt
The last hour i have 3 events which allowed (my server is as destination and and ip from France...with different ports in each event (32577,31927,30963) appears as a source
The event details are the following
MSSQL CLR permission set to unsafe attempt
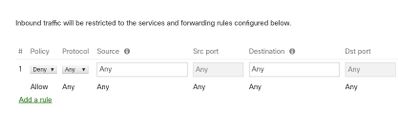
On firewall page i cannot add inbound rules. It says
Inbound traffic will be restricted to the services and forwarding rules configured below. |
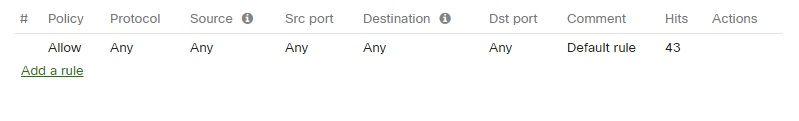
By default on the outbound rules there is a rule which i cannot delete it
This rule says policy allow, protocol, source,destination any and this time count hits...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
So what exactly is the question here?
On the other hand, to really answer your question(s), one would have to know more about your infrastructure, e.g. what is that server mentioned running (OS and services). I would assume that you‘re seeing an IDS alert for something that wouldn‘t have hit because of different OS or service.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello
The server running windows 2016 standard edition
The only service running on the above server is an Sql Server for our ERP program.
I can see that this default outbound rule is running by default on meraki (but i want to know what are these hits)
Our Sql uses a specific port and only one external ip has access on this port (For importing new orders from our b2b webpage)
I can see also that meraki recognizes lot of malwares and viruses every day (especially from mails) but we have also a good endpoint protection which blocks every day all of them
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Ids just detects. Ips prevents.
Incoming (from the outside originated traffic) is blocked by default. If you want to deny some outgoing traffic you can add deny rules before the any any rule
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello
Thanks for the info
We have the MX64 for the last two years. We have never this type of "problem". Also nothing changed in our network the last 2 months except a synology nas we purchased before 20 days. We use it only for operating systems backup in cooperation with veeam. No map drives, no file server
Yesterday i changed ids mode from detection to prevention
From last night we have over 1000 alerts from some ip's from Germany which tried to use our server "maybe" as a cryptocurrencie and mining tool. Our server appeared as a source and the Germany ip's as a destination. All the actions were blocked.
We didn't open any ports the last months , we didn't execute something strange...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@ManolisFr although you can't delete the default rule, you can add a drop all at the bottom as shown below and then add allow rules for the traffic that you want to leave the network. This is more how a traditional firewall works:
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I added 3 outbound rules for this case. There are 3 ip's from Germany.
But they continue the attacks ...
Meraki blocks each attack
I scanned earlier the server. I didn't found anything malicious.
I also reported these 3 ip's but i think that i have to wait... some days
I have about 700 Occurrences the last 2 hours
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Have you applied the DNS updates to your server? There is an actual crypto mining outbreak happening at the moment (I've seen it at an actual customer, it was hard to remove).
The sure sign you are infected is that the CPU will sit near 100% most of the time.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Good call @PhilipDAth , we patched ours within hours of the patch being released as it looked pretty nasty!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanx for the info guys
I cannot find the KB patch from microsoft. Do you have any direct link?
But ..Our server is not a DNS server for our network. We run only SQL , also we haven't active directory
Maybe this patch isn't necessary for us?
All the "attacks" blocked by meraki and our cpu usage is about 10-20% all the time
-
3rd Party VPN
171 -
ACLs
101 -
Auto VPN
318 -
AWS
39 -
Azure
72 -
Client VPN
434 -
Firewall
723 -
Other
598