We're migrating to the Cisco Community on March 29. The Meraki Community will enter read-only mode starting on March 26.
Learn more- Technical Forums
- :
- Security & SD-WAN
- :
- Re: Issues implementing VLANs on MX84
Issues implementing VLANs on MX84
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Issues implementing VLANs on MX84
Recently inherited this network with no documentation and have no experience with Meraki or design VLANs prior to this, very limited networking experience (currently studying for my CCNA).
Currently we have an MX84 with a bunch of switches.
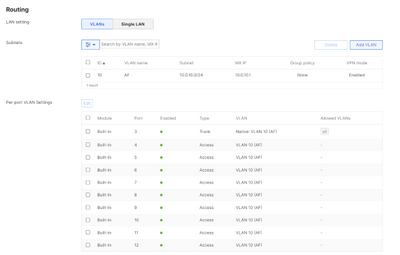
The first thing I noticed that seemed odd is that every single port on every single switch is set to trunk with all VLANs allowed and a native VLAN of 1.
I noted that our only defined VLAN for our primary LAN is ID: 10 (10.0.10.0/24). There are no static routes defined.
I tested out switching the port for my desk to an access port for VLAN 10, but this broke internet access.
If I change the access port to VLAN 1, I can access the internet and still ping devices on the 10.0.10.0/24 subnet.
Am I misunderstanding how this works or is something else misconfigured? Why do I need to have my access ports set to VLAN 1 when our subnet is defined on VLAN 10?
I'm also aware that using VLAN 1 is considered poor design, and would like to work towards implementing more segmentation in our network. Any thoughts on the design below would be appreciated - I'm unsure if I need to create new DHCP servers for each VLAN though or how to go about configuring DHCP in this scenario.
VLAN 90 - Management VLAN
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The reason for the original behaviour you saw is because the ports on the MX are configured for Trunk Native VLAN 10 and Access VLAN 10 (for your environment with only the one VLAN, they are pretty much the same thing).
Your computer is on the default VLAN (VLAN 1) until it hits the MX at which it is placed onto VLAN 10.
When changing the switchport to VLAN 10, you mess up the tagging flow and your traffic is dropped.
VLAN segmentation is definitely the way to go.
What you've got above is a good start.
My suggestions would be:
- Keep the Management VLAN and corporate devices VLAN. I personally don't see a need for the "MX84 Appliance VLAN)
- Segment the printers and other devices to a different VLAN if possible.
- Remove the native VLAN on the MX ports and set the VLAN on the switch access ports instead
When making changes like this, ensure you have a decent maintenance window and have someone on-site who can connect locally to the devices should they accidentally go offline from the dashboard. For example, depending on the existing config, it's very easy to take the switch offline when changing the config on the MX.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
What should the configuration of the MX lan ports look like instead?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi, it depends on...
If a MS is connected on those LAN Ports I would definitely configure a Trunk Port (with Native: Management) instead an Access Port and allow all the VLANs there.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The MX LAN port connecting to the switch should be a trunk port. The native vlan will typically be either the management vlan of the switch (if you haven't configured the management vlan in the switch configuration), an unused VLAN, or none.
-
3rd Party VPN
174 -
ACLs
91 -
Auto VPN
305 -
AWS
36 -
Azure
70 -
Client VPN
381 -
Firewall
863 -
iOS
1 -
Other
554 -
Wireless LAN MR
1