- Technical Forums
- :
- Security & SD-WAN
- :
- Re: I want to restrict 1 VPN user to 2 IP addresses How can I do this?
I want to restrict 1 VPN user to 2 IP addresses How can I do this?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I want to restrict 1 VPN user to 2 IP addresses How can I do this?
We replaced our Cisco ASA with a MX provided & supported by our ISP. for multiple reasons.
The ASA had 1 VPN account for our HVAC vendor that was restricted to 2 IP addresses.
Now I can't seem to get anyone at our ISP to even acknowledge my requests to do this, basically telling me its my problem and restrict them thru Active Directory permissions.
We are authenticating the VPN with AD, however these 2 IP addresses are PLC's and do not talk Active Directory.
Mostly pleased with the MX, but not very happy that I have to tell the HVAC people they're out of luck.
No way am I giving them full network access.
Any Ideas?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi rymiles, I believe that is what I want, will take me a bit to read thru it. Thanks.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Another solution. If you use the Cisco AnyConnect client (I'm assuming you are using the Meraki VPN client built into windows at the moment), and you authentication to AD using RADIUS (NPS can do this on Windows server), then you can have NPS send the Filter-Id attribute to dynamically restricting users.
Note that AnyConnect is an additional cost (you need to buy the licences), but it is quite cheap (IMHO).
ps. AnyConnect is a million times better.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Has something changed?
We were using AnyConnect and RADIUS when we switched to the Meraki and were told that AnyConnect was not supported.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
These are the instructions for configuring AnyConnect on Meraki MX.
https://documentation.meraki.com/MX/AnyConnect_on_the_MX_Appliance
It works great.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
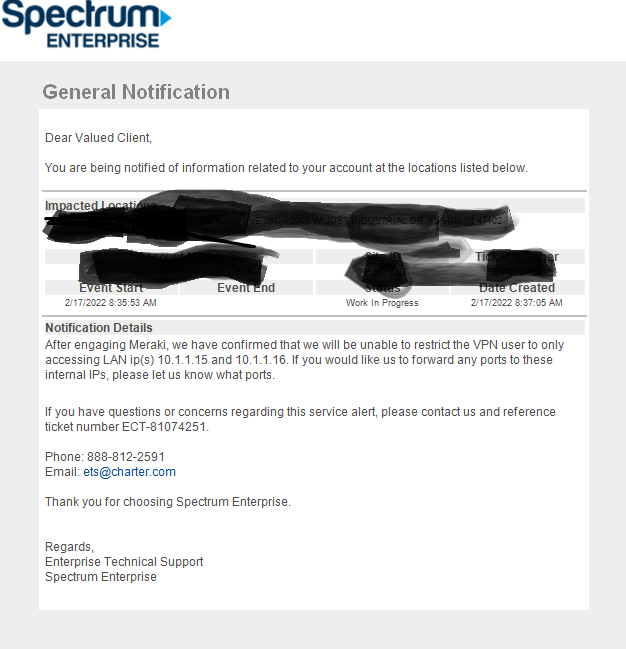
I am going to try to do this myself, but it Seems I am getting conflicting information.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You can restrict access of a VPN user by applying a group policy to the VPN user, and putting whatever layer 3 firewall rules you want in there.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Do other users also use client VPN? If so, the above approach probably wont work (it affects all client VPN users).
What you can do though is create a group policy (perhaps called client-vpn-hvac). In that add the firewall rules to say what they can access (don't forget to put a deny all at the end). Then go to the Network-Wide/Clients list, and find their VPN connection (add in the username column if you haven't got it already turned on). Then assign the group policy to that connection. It will stick for all future connections as well.
Then the restriction will only apply to that one VPN user.
-
3rd Party VPN
171 -
ACLs
101 -
Auto VPN
318 -
AWS
39 -
Azure
72 -
Client VPN
434 -
Firewall
722 -
Other
598