Get answers from our community of experts in record time.
Join now- Technical Forums
- :
- Security & SD-WAN
- :
- How to allow traffic from VPN vlan to local vlans
How to allow traffic from VPN vlan to local vlans
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
How to allow traffic from VPN vlan to local vlans
Hello,
I have only recently succeeded in establishing a VPN connection from a client PC to my Meraki.
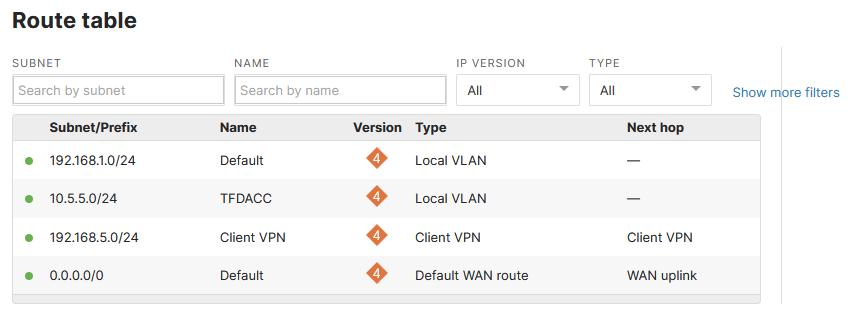
The specified vlan for the VPN is 192.168.5.0/24. My clients have to access servers in my local vlans. These are 10.5.5.0/24 and 192.168.1.0/24.
Do I set this up under port forwarding or under the Firewall? Can you please show an example of how to do it properly?
Second question is there a way to give some clients access to one local vlan, but not the other and vice versa?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You can restrict VPN clients access to local LAN servers by using L3 firewall rules.
See example 2 at the bottom of the following doc
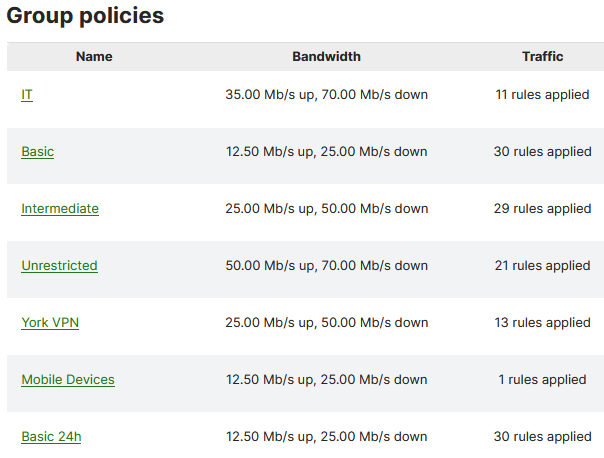
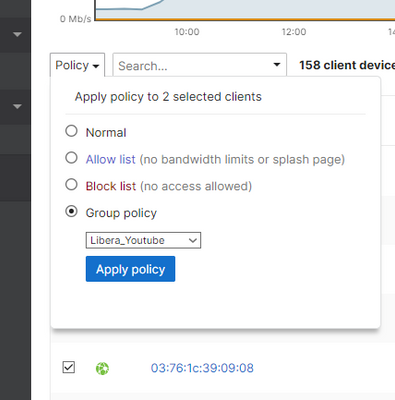
As for your second question, it's only possible using Meraki group policies. You'll need to create two (or more) group policies with the applicable firewall rules. You'll then need to login to the VPN as the user so the client shows up in the dashboard, and then assign the policy to the client.
Not particularly elegant but it will work.
Sadly, group policies linked to AD groups isn't supported for users logging in via VPN.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I don't understand. I don't want to restrict access. I want to allow it. How do I allow it?
I am now connected as 192.168.5.118. When I ping 192.168.1.3 I don't get a ping. When I try to access 192.168.1.3 with my file explorer is cannot find that IP. How do I reach it?
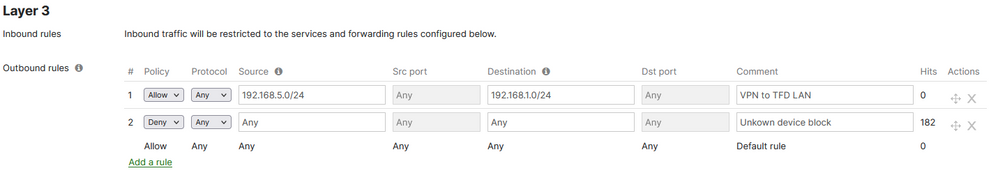
I have added a rule to the Layer 3 firewall like this:
This does not help. I still cannot access 192.168.1.3.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Meraki VPN clients have access to all local subnets within the network by default.
Are you seeing an increase of hits on the deny all rule when running the test? What is the local IP (non-vpn) of your test machine?
You could try a Meraki packet capture to see if the ping packets are making it across the VPN.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
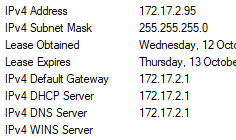
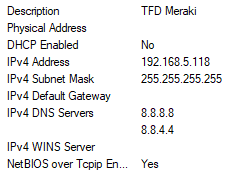
My laptop is on wifi at the moment to test VPN connectivity, here is the wifi and VPN IP's
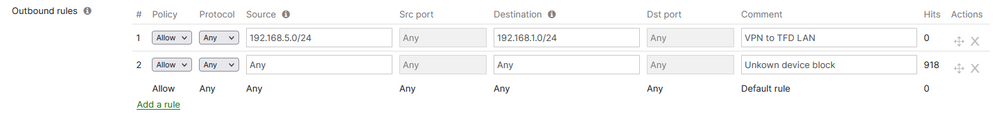
I have (for now) changed the block rule to allow, for testing.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Do you have a route on the MX for the 192.168.1.0/24 network? (Security and SD-WAN -> Route table)
And similarly, do you have routes in the rest of your network to route back to the 192.168.5.0/24 network via the MX?
Do you have any group policies set on the client you're testing from?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I've not changed anything in the routing table, it is still on default settings and look like this:
I do have several Group policies setup and the laptop in question is configured for one of these policies. But I must add that the Group policies are assigned by MAC adress and as the VPN is not using the MAC address of the LAN port on the laptop, I'm not sure that the Meraki will identify the laptop correctly. That being said I'm not interested in using the internet throught the meraki. The laptop can use it's own local internet as long as I can access the LAN on my office network.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Well, I suggest you try putting the machine on the allowed group policy and test again, It's not a route problem and probably a rule on your group policies are blocking the connection.
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I use MAC addresses to add clients to a Group Policy. The VPN connection does not have a MAC adress. How will I add a policy to it?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Has the client connected to VPN right? So you can add to a Group Policy.
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Group Policies
It is possible to manually apply group policies to clients connected via client VPN. Group Policy applied to a client VPN user is associated with the username and not the device. Different devices that connect to client VPN with the same username will receive the same group policy. For more help on assigning or removing group policies applied to a client, refer to the Creating and Applying Group Policies document.
Note: It is not possible to assign group policies automatically once a user connects to client VPN.
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Is it a non-Meraki VPN point or Meraki VPN?
If it is a non-Meraki VPN point, does the point on the other end need to allow its local networks?
There is an example of the configuration between a Cisco ASA and an MX Meraki ( It's Just a example OK?).
https://documentation.meraki.com/MX/Site-to-site_VPN/MX_to_Cisco_ASA_Site-to-site_VPN_Setup
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
So I am simulating a person working from home. That is a windows laptop on a home wifi using VPN to connect to the office MX64.
At the office they must, for example, be able to access the local NAS drive, Server1 or 192.168.1.3. Another user must be able to access a SQL server located at 10.5.5.1.
The VPN only assigns a subnet that is not the same as the local vlan's subnet and I cannot find a way to add more than one subnet to the VPN. So I don't know what to do to access the local subnet/vlan once looged in as a VPN user.
Maybe I'm missing something obvious, as everyone is telling me by default it is all accessible. However the method of accessing it eludes me.
-
3rd Party VPN
159 -
ACLs
88 -
Auto VPN
280 -
AWS
35 -
Azure
65 -
Client VPN
365 -
Firewall
819 -
iOS
1 -
Other
531 -
Wireless LAN MR
1