We're migrating to the Cisco Community on March 31. The Meraki Community will enter read-only mode starting on March 26 through March 31.
Learn more- Technical Forums
- :
- Security & SD-WAN
- :
- Re: How do I restrict a host or hosts to only access a certain website?
How do I restrict a host or hosts to only access a certain website?
Solved- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
How do I restrict a host or hosts to only access a certain website?
Hi,
I want to restrict a host or a number of hosts to only access a certain website, let's say
cnn com
How do I do this?
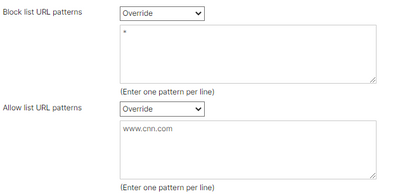
I'm thinking of creating a group policy and creating a block list of "*"" and only allowing only cnn com
Next, I'll create a firewall rule and specify the host or hosts that needs to access and the ip address of the destination
Then I apply the policy to the host.
Is this process correct?
I initially tried the group policy on a host and it seems that they still can go to other sites even though they're restricted by the * and the sites they're allowed to is specified.
Thanks
Solved! Go to solution.
- Labels:
-
Firewall
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The URL filtering should work as intended.
As per the below doc, the example provided matches what you're trying to achieve
Content Filtering - Cisco Meraki
I just performed a quick test of the URL filtering with a group policy and it seemed to work correctly.
It took a few minutes to apply but once applied it worked as intended.
Potentially existing flows through the MX won't be blocked so you might have to reboot the device for that.
As you indicated, the other way to do it is to create an L3 firewall rule to allow access only to the known public IP and deny all other traffic. This requires the public IP being relatively static but will end up being a 'stricter' policy than just URL filtering.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The URL filtering should work as intended.
As per the below doc, the example provided matches what you're trying to achieve
Content Filtering - Cisco Meraki
I just performed a quick test of the URL filtering with a group policy and it seemed to work correctly.
It took a few minutes to apply but once applied it worked as intended.
Potentially existing flows through the MX won't be blocked so you might have to reboot the device for that.
As you indicated, the other way to do it is to create an L3 firewall rule to allow access only to the known public IP and deny all other traffic. This requires the public IP being relatively static but will end up being a 'stricter' policy than just URL filtering.
-
3rd Party VPN
174 -
ACLs
91 -
Auto VPN
306 -
AWS
36 -
Azure
70 -
Client VPN
383 -
Firewall
868 -
iOS
1 -
Other
557 -
Wireless LAN MR
1