- Technical Forums
- :
- Security & SD-WAN
- :
- Re: Guest Wifi Network - Custom Hosted splash page security concern
Guest Wifi Network - Custom Hosted splash page security concern
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Guest Wifi Network - Custom Hosted splash page security concern
Hello,
I was reading the documentation about a custom-hosted splash page for a wifi network. So i understand that I have to redirect the customer to my page and allow my domain in the walled garden. I'm OK with that.
As I read the article, i saw that I can use two methods : "Clickthrough" and "Sign-on with meraki authentication".
First of all, i don't want my customer to create an account. I just want them to give one personnal information like a phone number (which doesn't require to have internet access) to indentify them.
In my case, i use the clickthrough. So imagine I create my page, I display a form requiring a phone number and then, as the documentation said, I need to foward the user to a granting page like "https://nXXX.meraki.com/splash/grant?continue_url=https://google.fr".
My question is : If the user directly write in the address bar the url to the granting page, is he going to bypass my splash page ? Because i don't see any shared secret between me and the meraki equipment so he just have to do a GET request, right ?
My second question is : Is there any way to secure that and block any attempt of directly going to the granting page ?
Regards
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
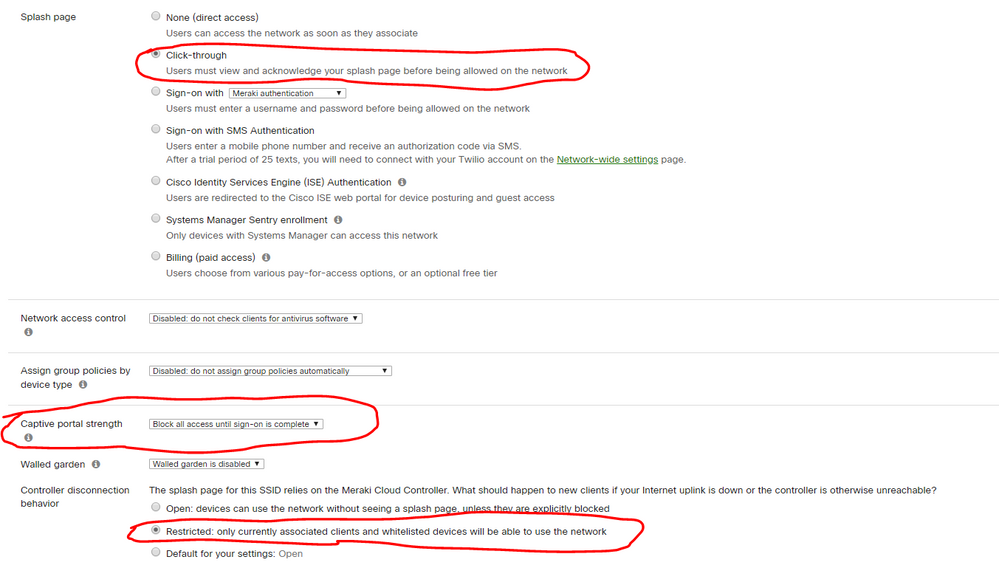
Yes there is as a matter of fact. In the "Access Control" of your SSID you can set this. As long as you have this setting you should be fine. Test it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thank you for your quick response.
But I have a question : How does it work technically ?
I found this troubleshooting guide on the documentation website : https://documentation.meraki.com/MR/Splash_Page/Splash_Page_Traffic_Flow_and_Troubleshooting
It explains all the request made for a Click-through Splash Page with EXCAP.
How setting Captive portal strength to "Block all access until sign-on" and Controller disconnection behavior to 'Restricted" is gonna prevent users to bypass my own splash page and directly hit the "/splash/grant?" webpage ?
PS: I didn't test it for now, maybe it'd work but i don't understand why it would
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
https://meraki.cisco.com/lib/pdf/meraki_whitepaper_captive_portal.pdf
Is that the kind of detail you're looking for?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hmm not really, this is the basis. The link above have more details about the request made.
But your link is the reason why i have security concern :
Once you are prepared to grant access to the user, you must forward certain parameters you can gather from the URL in step 2 above. Specifically, you must forward the user to the following URL:
GET[‘base_grant_url’] + “?continue_url=” + GET[‘user_continue_url’]
Where the following parameters are extracted from the user’s original query or specified by you:
base_grant_url = https://n##.meraki.com/splash/grant
user_continue_url = http://google.com
In the case of the example above the assembled URL would be:
https://n##.meraki.com/splash/grant?continue_url=http://google.com
Is it that simple ? No security tokens ? No challenge between your splash page and the meraki granting page ? No way to prove that the user got through your page and filled your form ? I may have missed something...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
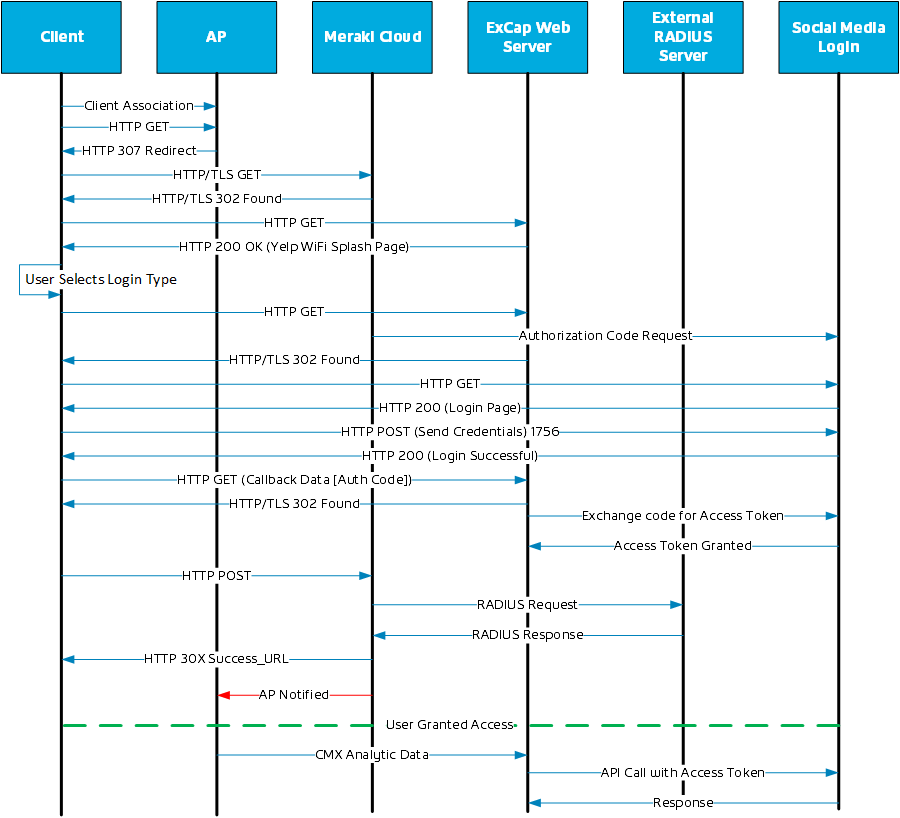
Ahh, ok maybe you're looking for something more like this diagram. I put this together when I was working on a project where the customer wanted to use a third party analytic company to do an Excap in conjunction with the Scanning API data to do targeted marketing and other nonsense.
Disclaimier, this was just me poking around with WireShark and trying to decipher the OAuth and OpenID specifications... This is not a Meraki doc, and I would be real money I don't have this 100% correct, but I do think it is a good overview of doing this with an Excap.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
That's a cool diagram
This case is actually the "Sign-on with my RADIUS server" method, right ? Because you provide data to the Meraki Cloud in order for him to do a RADIUS Request and process the Response.
I'm not using any RADIUS nor LDAP server to authenticate my custormer. In fact, i'm using a private communication service which use SMS.
The idea is that i want my customer to type their phone number. Then, he will receive a code by SMS asked by my page. If the code is correct, he will be redirect to the Meraki granting page where he will have the right to access internet right after. Meraki provide this solution but via Twilio (a paying solution).
I found the only way for me to do it, was to use the "Clickthrough" method. In consequence, I make sure that the client is human and his phone number is correct.
Maybe there is another way for me to do it ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Other than that unless you use some sort of LDAP twilio would be best bet for SMS.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
As i understand there is no way to secure a clickthrough custom-hosted splash page...
The only way to make sure that my user filled my form is to go with the RADIUS or LDAP method or with a paying solution like Twilio.
-
3rd Party VPN
170 -
ACLs
101 -
Auto VPN
316 -
AWS
39 -
Azure
71 -
Client VPN
431 -
Firewall
721 -
Other
596