Get answers from our community of experts in record time.
Join now- Technical Forums
- :
- Security & SD-WAN
- :
- Re: Group Policies and Whitelistings
Group Policies and Whitelistings
Solved- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Group Policies and Whitelistings
I am trying to create a security environment for a device to block all internet traffic except for the X amount of websites I have specified. I created a group policy for this device and I have tried varying configuration settings.
I have denied all HTTP/S traffic in the firewall rules, but listed all the whitelisted websites and it doesn't work nor was I expecting this to work.
I have allowed all HTTP/S traffic outbound in the firewall rules, used an * in the Blocked URL Patterns, and added all the whitelist sites and I can't get anywhere. I get a denied message at all HTTP sites and HTTPS websites won't even load.
Lastly, I have allowed all HTTP/S traffic in the firewall rules, put nothing in the Blocked URL Patterns, all the same whitelisted pages, and I can go anywhere on the internet, which I expected.
I want to say that my second configuration is how it's supposed to work, but I'm rather new using this device. Any and all help is appreciated.
Solved! Go to solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The whitelist is not correct. For example, Adobe should just be:
adobe.com
No *, no /, no nothing else.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It is best to use content filtering.
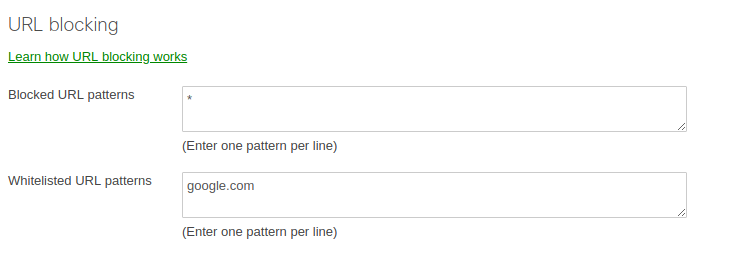
Block everything with a * and then add in what is allowed. Here is a screenshot only allowing access to *.google.com domains.
Note after making a change allow a good 5 minutes for it to take effect.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
That is exactly what I have set up, but it blocks everything, including what's in the whitelist.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
What firmware version are you using?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
14.24
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
If you go Network-Wide/Clients and click on the client, and under Policy in the bottom left you click "Show Details" - is it showing the group policy to be applied as expected?
Failing that; make sure you have quit the web browser and restarted.
Failing that; reboot the MX. Note the content filtering wont kick in straight away.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I have checked the clients and it does appear the policy is applied to the client.
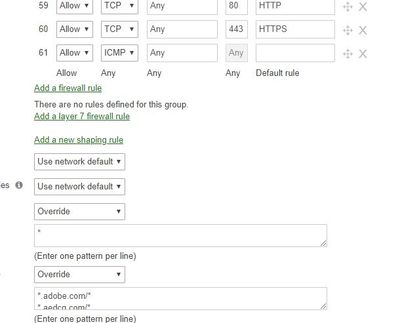
I have rebooted the firewall and restarted the browser, as well. Below is a picture of what I have in the Group Policies window. For every *.url.com/* there is a url.com/*. Am I using the wildcards incorrectly? I manage another different kind of firewall that uses this type of URL whitelisting.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The whitelist is not correct. For example, Adobe should just be:
adobe.com
No *, no /, no nothing else.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Ok live tested and it's working. Thank you all for the assistance. I guess I misunderstood how this device uses the wildcard.
-
3rd Party VPN
160 -
ACLs
88 -
Auto VPN
282 -
AWS
35 -
Azure
65 -
Client VPN
365 -
Firewall
827 -
iOS
1 -
Other
536 -
Wireless LAN MR
1