- Technical Forums
- :
- Security & SD-WAN
- :
- Re: Group Policies and Active Directory
Group Policies and Active Directory
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Group Policies and Active Directory
Hello all,
I am currently struggeling with the Active Directory integrated Group Policy features and was hoping maybe you could provide me with some input.
The intention is to maintain a Group Policy for FTP users. The Active Directory integration is up and running and the Client - User mapping seems to work fine (according to the event logs).
Thus, the MX should be aware of which users is using which client. However, it does not seem that any of the specific group policy firewall rules are being applied on the machine that has a user associated, who is a member of the mapped active directory FTP security group.
Once I add the active directory PC object though, the rules start getting applied. One further disclaimer: the affecting clients counter will stay at 0 constantly, no matter what - I assume it just simply doesn't work with AD mapped group policies?
Therfore my question - is it even possible to manage a custom firewall ruleset under group policy for a AD security group that only contains the user and not the machine object?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It should only trigger on the user logon event. The dashboard only tracks machines. So there is a mapping.
Does the dashboard show that the correct group policy is applied to the machine?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Philip
Thanks for the feedback.The group policy will always show 0 associated clients no matter what.
I was able to reproduce the following behaviour though:
- If the mapped Active Directory group only contains the user - the default Layer 3 rulesets of the firewall apply
- If the mapped Active Directory group contains the machine object as well - the group policy firewall ruleset gets applied
stockster
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Is the MX the default gateway in this network?
In the Dashboard you should [normally] be mapping a group of users and not a group of machines to a Meraki group policy.
If you are not mapping a group of users then it can't assign the Meraki policy based on the user.
The mapping the AD group of users is not working then the auditing in AD is probably not working.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes the Meraki is the default gateway in this case.
That was also my understanding and the FTP active directory group that I am trying to map is a user group only (for testing purposes I tried to add the computer object there as well), but the goal clearly is to manage a group policy ruleset for an active directory user group only (FTP users). I hope this clarifies the situation.
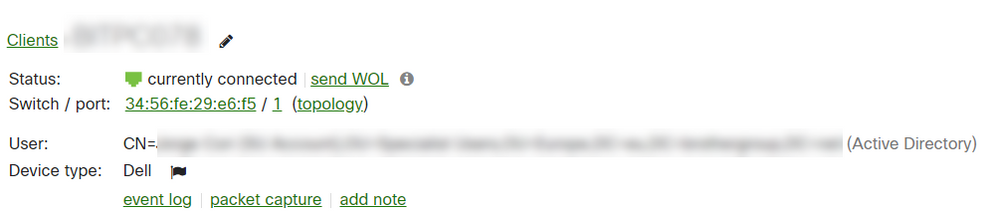
I am pretty sure the Active Directory integration works fine as far as I understand. Because when I go click on the Client machine I can see an Active Directory user:
Do I assume correctly that with this sitatution, the group policy's firewall rules should override the default L3 rules for any user in the Active Directory FTP group?
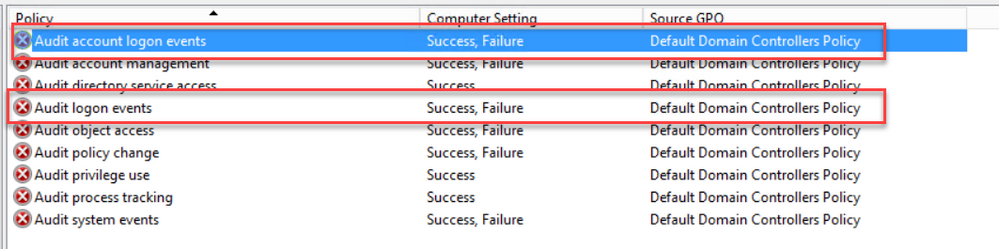
Concerning your comment about the AD auditing, I checked the domain controller's applied settings by running rsop:
Success is in place for both sections.
Am I missing something else?
Thanks a lot for your help.
Regards,
stockster
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
>Do I assume correctly that with this sitatution, the group policy's firewall rules should override the default L3 rules for any user in the Active Directory FTP group?
It depends if you have used the override option or the append option in the group policy.
-
3rd Party VPN
170 -
ACLs
101 -
Auto VPN
315 -
AWS
39 -
Azure
71 -
Client VPN
431 -
Firewall
715 -
Other
594