Get answers from our community of experts in record time.
Join now- Technical Forums
- :
- Security & SD-WAN
- :
- Re: Firmware 15.42.1 problem in non meraki vpn peers (MX67)
Firmware 15.42.1 problem in non meraki vpn peers (MX67)
Solved- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Firmware 15.42.1 problem in non meraki vpn peers (MX67)
Hi,
I'm having issue with non-meraki vpn peers connection after I upgrade to 15.42.1 from 14.53.
I was insisted to rollback the firmware after the upgrade. Just want to confirm is that really the problem ? I'm using ikev1 by the way.
or in this new firmware I need to use ikev2 ?
Please suggestion. Thanks.
Solved! Go to solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Bruce,
It works now by entering the IP Private of the remote peers.
Thanks for the help.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You haven't provided enough information to help.
You can use IKEv1 or IKEv2. Both work.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Philip,
Here is the details.
Headquarters
Cisco Meraki MX67
IKEv version : IKEv1
IP Sec Policies : AWS
Phase 1 Encryption : AES 128
Phase 1 Authentication : SHA1
Phase 1 DF Group : 2
Phase 1 LIfetime : 28800
Phase 2 Encryption : AES 128
Phase 2 Authentication : SHA1
Phase 2 PFS Group : 2
Phase 2 Lifetime : 3600
Pre-shared key : used
Branch
Grandstream GWN7000
IKEv version : IKEv1
Phase 1 IKE Lifetime : 28800
Phase 1 Key Exchange mode : Main
Phase 1 Pre-Shared key : used
Phase 1 Encryption Algorithm : AES_CBC_128
Phase 1 Hash Algorithm : SHA1
Phase 1 DH Group : MODP1024
Phase 2 Encryption Algorithm : AES_CBC_128
Phase 2 Hash Algorithm : SHA1
Phase 2 PFS Group : MODP1024
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
What is the actual issue? VPN builds and fails, VPN never works, etc?
What do the logs on both ends say?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
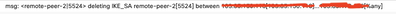
In Cisco Meraki, I got this log attached below.
For Grandstream GWN7000, I got this log attached below.
At the HQ side, it keeps deleting SA key. At the branch side, it keeps reconnecting and won't authorized. I suspicious that it has something to do with meraki settings. It works if I downgrade the meraki firmware to 14.53. After I upgrade, suddenly it won't connect.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Did you see this in the MX15 release notes?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Bruce,
I've just noticed it. Thank you for the help.
But what value do I need to fill in the remote ID field, because there is no local ID in the grandstream device. I've try to enter the Public IP and FQDN value but still won't work.
Any idea ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It’s hard to say if the Grandstream doesn’t have a specific Local ID parameter. It could use its hostname, it’s IP address (the public one, or the private one), or some other parameter that you configure on the device. Have a look at the ‘non-Meraki VPN peers’ section of this document for some suggestions, https://documentation.meraki.com/MX/Site-to-site_VPN/Site-to-Site_VPN_Settings
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Bruce,
It works now by entering the IP Private of the remote peers.
Thanks for the help.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hey @endrianusgohan! I seem to be experiencing the same issue as you did, but haven't gotten mine to work. Could you provide me with the exact Remote ID config that you used on the MX? For example in my case the peer has public IP 207.16.X.X, and only a single LAN with the peer being 10.1.1.1 (10.1.1.0/24 being the remote subnet I am trying to reach). So in my case would I configure 10.1.1.1 as the Remote ID on the Meraki? Any clarity you can provide would be greatly appreciated!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @RB___ ,
I use the private IP of the ONT Modem from the ISP of the remote non-meraki router.
If your IP is behind the NAT, you can use that Private IP Address as your remote ID.
You should try. Hope it works for you too.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello Bruce,
I am facing same issue. We have AWS on other side. Do you know what we can use as remote ID for AWS?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Most likely, it will be the public IP address of the AWS peer.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello @PhilipDAth . Thank you for your quick response. So it is going to be same as Public IP field, right ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
99% likely, yes.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Here is a note from Meraki, and it worked, even if we have 1 MX and 1 Watchguard instead of the 2 MXs in their explanation
When configuring NMVPN connections between 2 MXs in different organizations that are running MX15 code and above that are not using a UserFQDN and are NATed behind an upstream device, please ensure that the remote ID field of the NMVPN peer is filled out with the private IP address of the remote NATed MX.
Our setup:
1rst site: an MX that is NATed behind another device, getting 192.168.x.x on its Internet port
2nd site : Watchguard with ISP Public IP
At both sites, we had Remote ID parameters configured with both Public IP
S2S non-meraki vpn nerver came up, until we configured the remote ID field in Watchguard with the 192.168.x.x of the Meraki.
S2S VPN came up right away
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Here is the issue:
the far end firewall (near end is your meraki) has an IP on the interface that receives the VPN connection (the WAN interface) that is not the Public IP that the near end/meraki is connecting to
(this can be because the far end firewall is double-NATed, etc)
you will put the interface ip of the far end firewall as the "Remote ID" on the meraki vpn config
for example
far end: ASA in Azure, with interface IP (WAN) of 10.20.30.40, and azure public ip "resource" of 55.66.77.88
near end: meraki, vpn config with
public ip = 55.66.77.88
remote id = 10.20.30.40
Normally the remote id is assumed to be the remote public ip, but if the interface ip is not the public ip, you will have to specify the interface ip as the remote id
-
3rd Party VPN
165 -
ACLs
89 -
Auto VPN
290 -
AWS
36 -
Azure
66 -
Client VPN
368 -
Firewall
834 -
iOS
1 -
Other
540 -
Wireless LAN MR
1