We're migrating to the Cisco Community on March 31. The Meraki Community will enter read-only mode starting on March 26 through March 31.
Learn more- Technical Forums
- :
- Security & SD-WAN
- :
- Combined or separate networks?
Combined or separate networks?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Combined or separate networks?
What is everyone doing from a combined/separate network perspective? I just started out with a full Meraki stack, MX, MS, and MR, so I started with a combined network. However, it seems that within a combined network I only have one chance to apply a group policy. For example, I apply a group policy to a wireless client device to block access to a particular internal resource via a L3 firewall rule I also have to completely duplicate all the L3 firewall rules that are configured on the MX, otherwise the device bypasses all the MX firewall rules.
So, now I've split the networks. This seems to let me apply a group policy to my wireless clients (say, IoT devices), but also allows the MX L3 firewall rules to still apply because the group policies are only network specific. Is my understanding correct?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Seperate networks are mostly a thing of the past now, and mostly people only use combined networks.
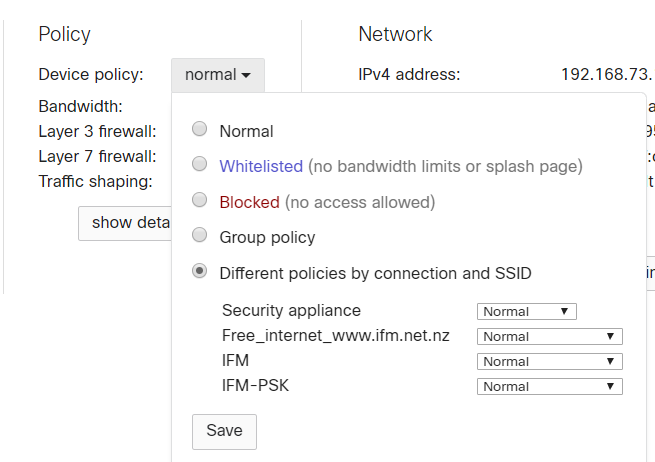
I typically do all my firewall rules on just the MX, rather than both the MX and MR. Also on the client page you can select to apply the group policy by connection or SSID, so you can apply it to the client for only one type of connection it is using.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The problem I have with split networks is that you can't click through on a client with problems from the MX to the switch or AP. So troubleshooting becomes a thing where you're going back and forth between networks.
There is however the big problem with combined networks and a L3 switch that you can have duplicate traffic types from ghost clients because in combined networks you can only use track clients by MAC address.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It is always ideal to have a single device take care of layer 3 firewall rules in a network (either the firewall or the AP).
In a combined network, when you apply a group policy with layer 3 firewall rules, your telling the Meraki devices to handle the layer traffic at a singular level, so bypassing the global firewall rules would be expected.
Additionally, it is always easier to track all layer 3 firewall rules on one page, rather than jump between multiple devices.
I would recommend you add the layer 3 firewall rule at the global level (on the MX).
BTW, what rule are you adding on the AP level, that cannot be added at the MX?
If your issue was resolved, we request you to mark the post resolved so other users can benefit in future
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
After splitting networks, all my clients have different IPs - some up to 8 IPs which they once had) and different policies. How can I prevent this?
-
3rd Party VPN
174 -
ACLs
91 -
Auto VPN
306 -
AWS
36 -
Azure
70 -
Client VPN
383 -
Firewall
868 -
iOS
1 -
Other
557 -
Wireless LAN MR
1