We're migrating to the Cisco Community on March 31. The Meraki Community will enter read-only mode starting on March 26 through March 31.
Learn more- Technical Forums
- :
- Security & SD-WAN
- :
- Re: Client VPN - AD Authentication
Client VPN - AD Authentication
Solved- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Client VPN - AD Authentication
Solved! Go to solution.
- Labels:
-
Client VPN
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Group policies don't work for L2TP VPN just for Anyconnect.
The certificate is a requirement if you want to authenticate the users from LAN. Check it out:
The MX will run through the following steps to identify AD group members and apply associated group policies:
- MX securely contacts the specified Domain Controllers for the AD domain, using TLS
- MX reads WMI logon events from the DC's security events, to determine which users are logged into which devices.
- MX binds to DCs using LDAP/TLS to gather each user's AD group membership.
- Group membership is added to a database on the MX.
- If a domain user's group membership matches an AD group policy mapping in Dashboard, the MX can apply the associated group policy to the user's computer.
Because the MX is continuously gathering this information from the domain controllers, it is able to accurately apply the policy in real-time whenever a new user logs in.
Note: At this time, the MX does not support mapping group policies via Active Directory for users connecting through the Client VPN.
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@Patrik73, there are some steps that you have to configure before. Take a look ate the documentation:
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks!
I guess I need that certificate, but the guide is a little to shallow. Al least for me.
Not sure how to create that self-signed certificate on my server. Server 2019.
Would really appreciate a guide. 🙂
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Maybe it will help you: https://windowstechpro.com/how-to-install-certificate-services-ad-cs-in-server-2019/
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Or is it enough to install IIS-role and create the certificate that way?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You need a certificate, either self-signed or a valid certificate.
I always use a self-signed certificate so I prefer to install AD CS, but each case is different.
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thank you!
I really appreciate your help.
Guess I will install the AD CS.
I do have a wildcard cert, but that is for my public domain name.
*.name.com
and not my internal domain name
*.name.local
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
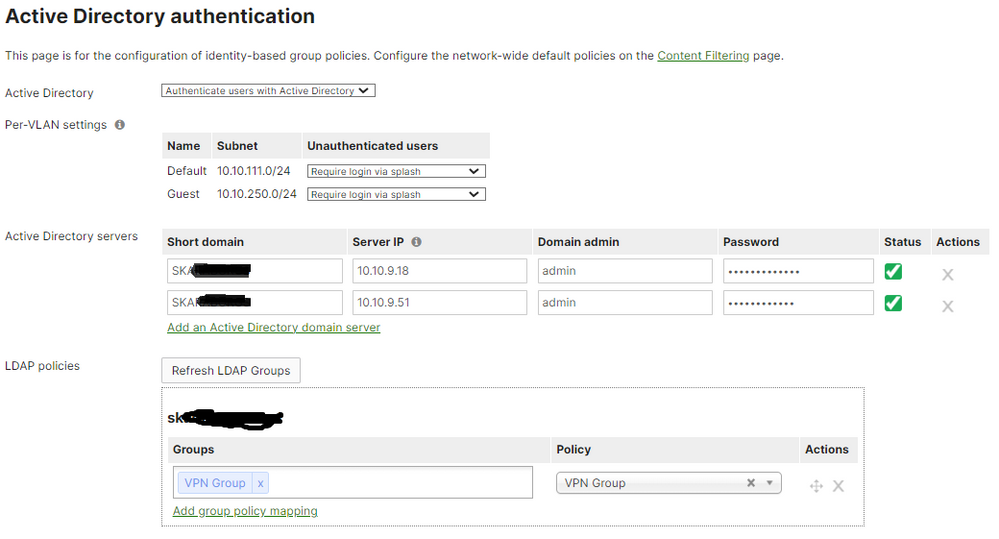
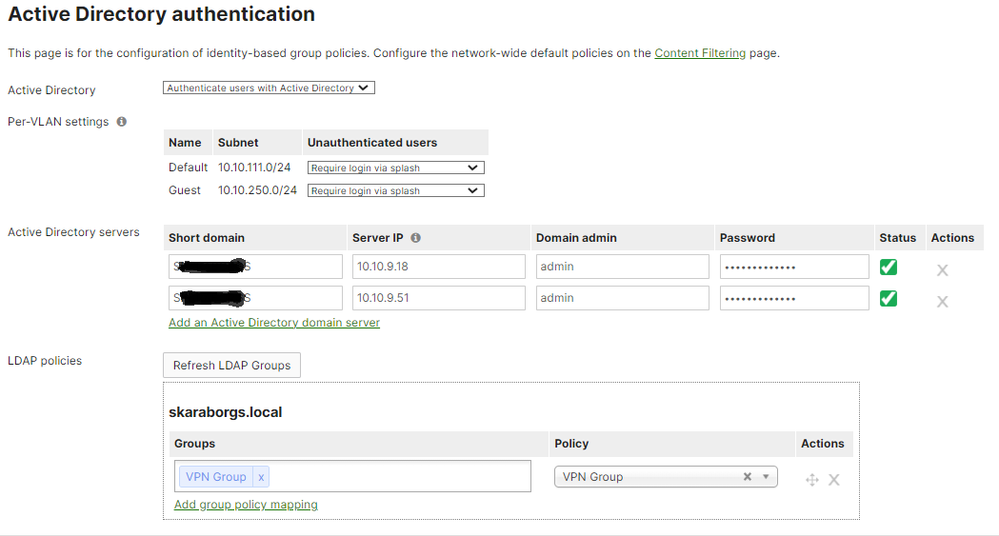
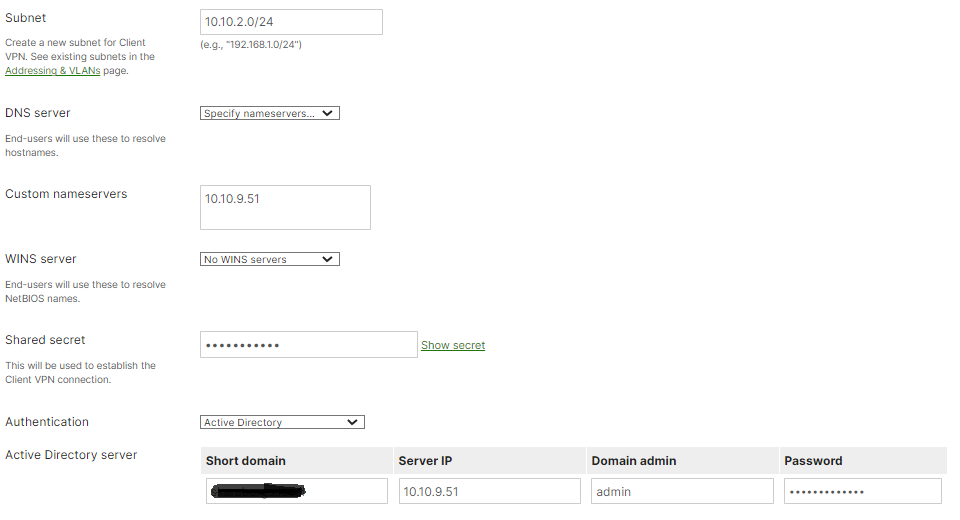
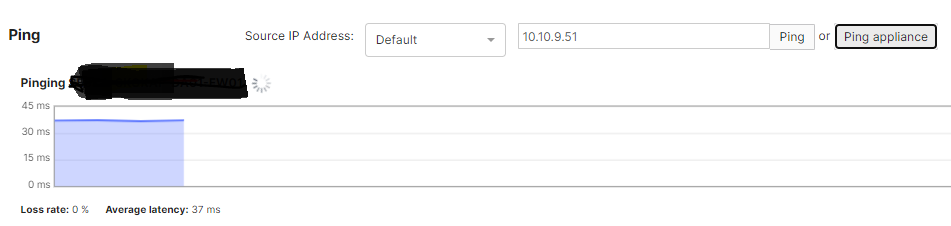
I now have setup an CA-server and created a certificate.
Configured Active Directory authentication.
It looks like it can communicate.
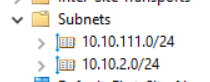
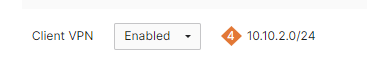
I have also added the net in Subnet
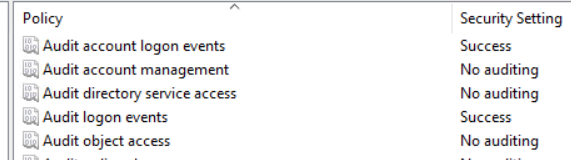
And the Audit Policy.
And my certificate seems ok.
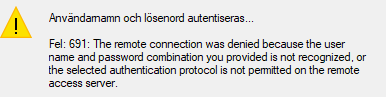
But still get errror 691 😞
Getting a little bit frustrated.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
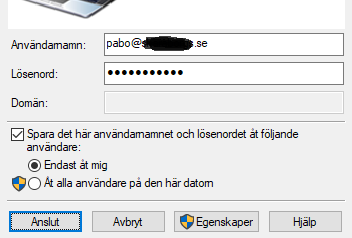
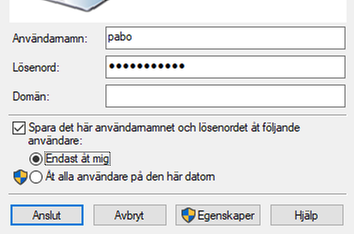
Your L2TP connect probably is misconfigured. Can you share the configuration on your machine?
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It seems to work now.
I tried to login with my full login name but then I get Error 691.
When I change to just my username it worked.
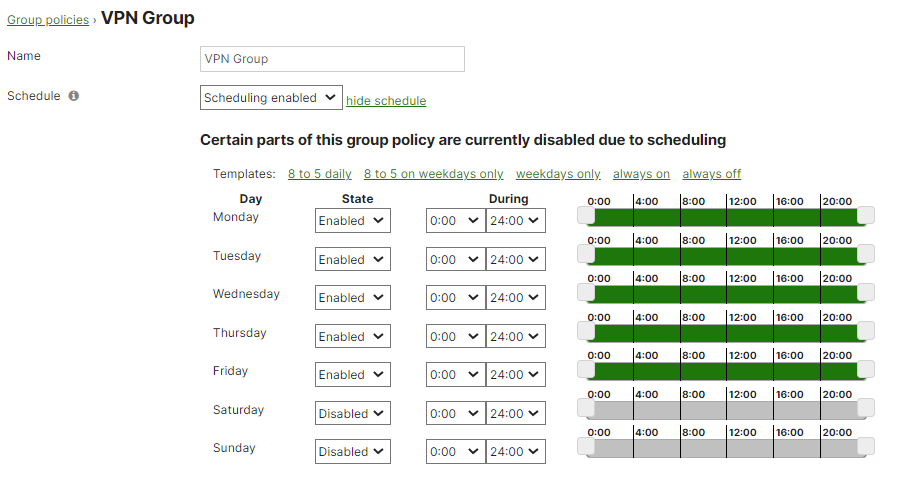
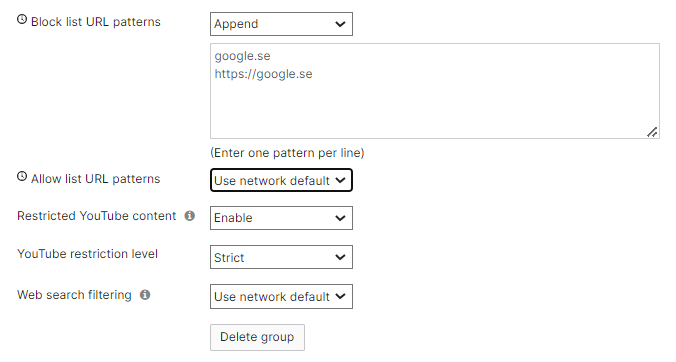
But I'n not sure what the groups actually does.
I tried to set some restriction on the group that my testuser is member of, but that doesn't change anything.
Maybe I should go for Radius login instead to be able to restrict access to VPN through AD-group membership.
And then I can activate Azure MFA.
And I'm not sure why I need the certificate, I removed it and the VPN still works.
Guess all I needed to do was to add to the Client VPN settings.
Domain short name
IP to DC
Username
Password
I also removed the subnets from Sites and Services and it still works.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Group policies don't work for L2TP VPN just for Anyconnect.
The certificate is a requirement if you want to authenticate the users from LAN. Check it out:
The MX will run through the following steps to identify AD group members and apply associated group policies:
- MX securely contacts the specified Domain Controllers for the AD domain, using TLS
- MX reads WMI logon events from the DC's security events, to determine which users are logged into which devices.
- MX binds to DCs using LDAP/TLS to gather each user's AD group membership.
- Group membership is added to a database on the MX.
- If a domain user's group membership matches an AD group policy mapping in Dashboard, the MX can apply the associated group policy to the user's computer.
Because the MX is continuously gathering this information from the domain controllers, it is able to accurately apply the policy in real-time whenever a new user logs in.
Note: At this time, the MX does not support mapping group policies via Active Directory for users connecting through the Client VPN.
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thank you very much for the help.
-
3rd Party VPN
174 -
ACLs
91 -
Auto VPN
306 -
AWS
36 -
Azure
70 -
Client VPN
383 -
Firewall
868 -
iOS
1 -
Other
557 -
Wireless LAN MR
1