We're migrating to the Cisco Community on March 29. The Meraki Community will enter read-only mode starting on March 26.
Learn more- Technical Forums
- :
- Security & SD-WAN
- :
- Re: Can't ping Non-Meraki S2S VPN peer subnets
Can't ping Non-Meraki S2S VPN peer subnets
Solved- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Can't ping Non-Meraki S2S VPN peer subnets
Hello,
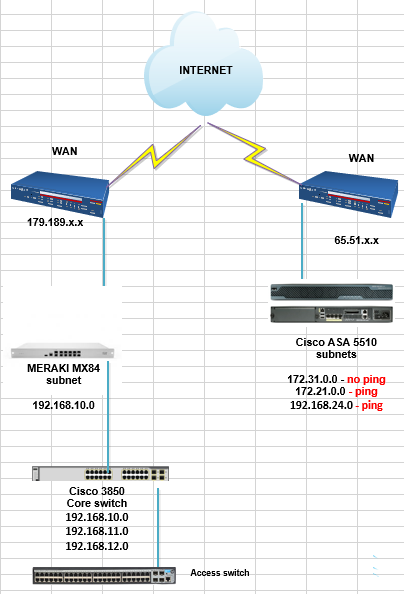
Need some help on accessing the subnets on the Non-Meraki S2S VPN peer.
I already have up and running an IPsec tunnel between HQ and Branch(ASA to ASA), now the idea is to update our Branch ASA5510 to MX84.
Just tested a VPN between MX84 and the HQ ASA and connects normally as I'm able to check over the " All Non-Meraki/Client VPN" event log.
My work on replacing the ASA to MX was to mirror the conf in ASA to MX, advertising the subnets the way they were on ASA.
The problem is that I'm not able to ping the HQ subnets from the MX.
The only thing that I see suspicious is that in ASA I see several route as:
route outside x.x.x.x(HQ subnet) 255.255.0.0 x.x.x.x(Branch MX WAN gateway) 10
I did configured a static route on MX, with HQ subnet pointing to MX local lan IP which does not go online on Route Table, tried too HQ subnet pointing to WAN gateway, but the MX does allow this stating that there's no subnet active as WAN subnet.
What is the issue?
Any help is appreciated
Solved! Go to solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
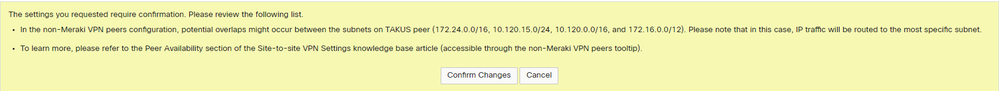
My huge problem is with subnets 172.16.0.0/12 and 172.24.0.0/16.
172.24.0.0/16 the subnet which MX is connected through the VPN(HQ) and from HQ we have another branch with the 172.16.0.0/12.
In this other branch they have created the network 172.16.0.0/12, but they don't use the 172.24.0.0 network there.
If I advertise the subnets from MX tunnel to HQ(on both ends vice-versa) this way:
172.16.0.0/13
172.24.0.0/16
172.25.0.0/16
172.26.0.0/15
172.28.0.0/14
I mean, excluding the overlap subnet from the 172.16.0.0/12, will it work?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You wont need ot add a static route on the MX side.
I would start at the ASA at HQ and see what it is reporting.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thank you @PhilipDAth
I just discovered that I can ping all subnets but one, I have 6 subnets advertised on VPN and just this one does not ping.
I'm current at Branch and I don't have access to the HQ ASA, so I'll ask them just in last resort.
As you can see I have a Core switch that gets my subnets routing
With ASA in place, when I traceroute from a client below ASA I get these hops to the subnet that I'm unable to ping when Meraki is placed:
1 - 3ms - Gateway
2 - *
3 - 119ms - subnet in HQ
Maybe it is something that I'm missing?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Just found the issue:
Overlapping subnets, with ASA in place I have no problem on working with these subnets.
I need to have access to all of them over the VPN, how can I manage to fix that?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
My huge problem is with subnets 172.16.0.0/12 and 172.24.0.0/16.
172.24.0.0/16 the subnet which MX is connected through the VPN(HQ) and from HQ we have another branch with the 172.16.0.0/12.
In this other branch they have created the network 172.16.0.0/12, but they don't use the 172.24.0.0 network there.
If I advertise the subnets from MX tunnel to HQ(on both ends vice-versa) this way:
172.16.0.0/13
172.24.0.0/16
172.25.0.0/16
172.26.0.0/15
172.28.0.0/14
I mean, excluding the overlap subnet from the 172.16.0.0/12, will it work?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
If you advertise the more specifix prefixes it should work.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thank you @PhilipDAth
For now I'll choose my guessing as solution because it'll take some till I can test this routes in HQ ASA.
For those searching for solution to the same problem, have in mind that this case just worked because the overlapping subnet 10.24.0.0 was not in use on both sites, but just in one side.
If you have same networks on both sites, a Non-Meraki VPN won't work in this case(at least this way) because it does not have the VPN translation active.
VPN translation, which is the feature that solves the problem of same subnets on both sites, only works with AutoVPN which is Meraki-to-Meraki VPNs.
If you need more info: https://documentation.meraki.com/MX/Site-to-site_VPN/Using_Site-to-site_VPN_Translation
-
3rd Party VPN
174 -
ACLs
91 -
Auto VPN
305 -
AWS
36 -
Azure
70 -
Client VPN
382 -
Firewall
866 -
iOS
1 -
Other
557 -
Wireless LAN MR
1