We're migrating to the Cisco Community on March 29. The Meraki Community will enter read-only mode starting on March 26.
Learn more- Technical Forums
- :
- Security & SD-WAN
- :
- Block public IP
Block public IP
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Block public IP
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This is based on mac
To secure a network better you could consider using authentication like 802.1x
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
thanks for your reply
but as i know this for private IP not public
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Ip from outside cant initiate sessions to you lan, unless you did some nat/port forwarding config.
You can make a layer3 firewall rule.
Deny any, publicIP
Or
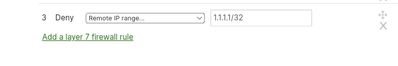
You can block traffic using layer7 firewall. Deny remote ip range
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
There is no any NAT and port forwarding in the LAN
The question is is there any way to block specific public IP
thanks for reply
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You can make a layer3 firewall rule.
Deny any, publicIP
And/Or
You can block traffic using layer7 firewall. Deny remote ip range
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
i've tried not the meraki rejected the command
would you please do any example
in Layer 3
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
i did that before but unfortunately doesn't work except /32 thanks for your help i will did it now and waiting the results then update you
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The inbound firewall will deny any traffic that does not have a session initiated by a client behind the MX. This allows internal client machines to connect with any resources they need, but does not let outside devices initiate connections with inside client machines. The exception to this is if a Port Forward or 1:1 NAT is created. More information on Port Forwarding and 1:1 NAT can be found here.
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You need to create a layer 7 firewall rule for this use case. It will block all traffic in and out to the IP address you specify.
-
3rd Party VPN
174 -
ACLs
91 -
Auto VPN
306 -
AWS
36 -
Azure
70 -
Client VPN
382 -
Firewall
866 -
iOS
1 -
Other
557 -
Wireless LAN MR
1