Get answers from our community of experts in record time.
Join now- Technical Forums
- :
- Security & SD-WAN
- :
- Re: Best practise for controling traffic between two peers through a 3rd pa...
Best practise for controling traffic between two peers through a 3rd party VPN tunnel
Solved- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Best practise for controling traffic between two peers through a 3rd party VPN tunnel
Hi,
I need to create an IPsec tunnel with another peer (which is not an MX) and then we need to gice acces to the other side only to one host on our side. I guess I have to put the entire network of the other peer under the private subnet but then how should I controll what talk to what. Is it by creating rules under the site-to-site outbound firewall rules or should I create those rules on the Security & SD-WAN -> Firewall? Or is it maybe some other way to do it?
BR
Solved! Go to solution.
- Labels:
-
3rd Party VPN
-
ACLs
-
Firewall
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Considerations for VPN Firewall Rules
When configuring VPN Firewall rules, it is important to remember that traffic should be stopped as close to the originating client device as possible. This cuts down on traffic over the VPN tunnel and will result in the best network performance. Because of this, site-to-site firewall rules are applied only to outgoing traffic. As such, the MX cannot block VPN traffic initiated by non-Meraki peers.
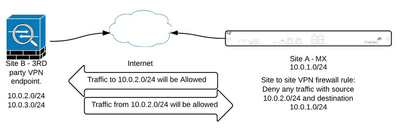
The image below demonstrates a misconfigured site-to-site firewall rule. Site-to-site firewall rules only apply to outbound traffic. This rule will never be applied as the source subnet is not a LAN subnet on the MX:
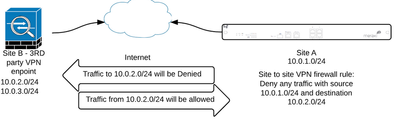
The following image demonstrates a site to site firewall rule that will be applied correctly. Traffic from the 10.0.1.0/24 subnet will not be able to reach 10.0.2.0/24 subnet since the 10.0.1.0/24 subnet is a LAN subnet on the MX.
When traffic passing through the MX matches a site-to-site VPN route, VPN firewall rules are applied in descending order. VPN traffic to both AutoVPN and Non-Meraki peers is only subject to the site-to-site firewall rules and is never subject to global Layer 3 firewall rules.
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Considerations for VPN Firewall Rules
When configuring VPN Firewall rules, it is important to remember that traffic should be stopped as close to the originating client device as possible. This cuts down on traffic over the VPN tunnel and will result in the best network performance. Because of this, site-to-site firewall rules are applied only to outgoing traffic. As such, the MX cannot block VPN traffic initiated by non-Meraki peers.
The image below demonstrates a misconfigured site-to-site firewall rule. Site-to-site firewall rules only apply to outbound traffic. This rule will never be applied as the source subnet is not a LAN subnet on the MX:
The following image demonstrates a site to site firewall rule that will be applied correctly. Traffic from the 10.0.1.0/24 subnet will not be able to reach 10.0.2.0/24 subnet since the 10.0.1.0/24 subnet is a LAN subnet on the MX.
When traffic passing through the MX matches a site-to-site VPN route, VPN firewall rules are applied in descending order. VPN traffic to both AutoVPN and Non-Meraki peers is only subject to the site-to-site firewall rules and is never subject to global Layer 3 firewall rules.
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
All right, so If I want to allow the 3rd party endpoint (their network, lets say 10.0.2.0/24) to talk with only one host on my end (for example 10.0.1.10/32) then I allow first only the source 10.0.1.10/32 to talk to 10.0.2.0/24 and then deny source 10.0.1.0/24 to destination 10.0.2.0/24. with these two rules the other part would be able to talk only to that specific IP adress but not to the entire network. Is my logic correct?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes, It is.
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
That does not work, you cant block incoming traffic with the site2site vpn firewall.
You could try using a the group policy and assign it to the local vlan. Gp uses stateless firewall rules
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
So are you saying that Meraki documentation is wrong?
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
No. Its says "As such, the MX cannot block VPN traffic initiated by non-Meraki peers."
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
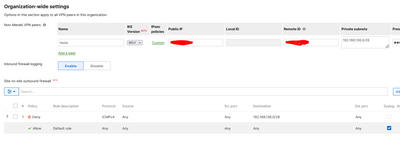
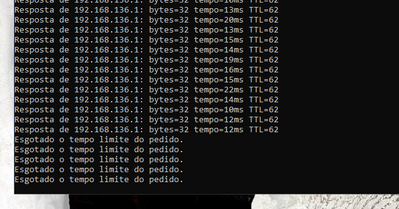
yes, It works:
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
But that is traffic initiated by you. Not by the other 3rd party
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
yes, but it works, it's just a matter of ajust the rules.
The rule may not be bidirectional, but if you create a rule the other way around it should work. I know because I use it on another customer, and it works. It may not be practical, but it works.
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It should not work because meraki statefull fw is outbund and if a inbound session is iniated its a allowed session in the firewall.
If it works then they should remove this part from the documentation.
"As such, the MX cannot block VPN traffic initiated by non-Meraki peers"
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
👍
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This is not a valid test as you are only blocking the echo-replies when initiated from the peer side.
I would consider this firewalling working if I can block an SQL-Slammer (which was only one UDP packet without any return packet) from my Non-Meraki-peer.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
👍
Please, if this post was useful, leave your kudos and mark it as solved.
-
3rd Party VPN
159 -
ACLs
88 -
Auto VPN
279 -
AWS
35 -
Azure
64 -
Client VPN
365 -
Firewall
819 -
iOS
1 -
Other
528 -
Wireless LAN MR
1