Get answers from our community of experts in record time.
Join now- Technical Forums
- :
- Security & SD-WAN
- :
- Re: AnyConnect Clients can't access Non-Meraki peer Site to Site hosts
AnyConnect Clients can't access Non-Meraki peer Site to Site hosts
Solved- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
AnyConnect Clients can't access Non-Meraki peer Site to Site hosts
Hi all,
I've read many topics complaining of this same issue, but have yet to find a resolution that applies in my case. As the title says - our setup is an MX100 with a non-Meraki peer at our colocation facility. AnyConnect clients can access anything *local* to the Meraki, but can't access any hosts on the remote side of the tunnel.
VPN Client --> MX100 --//-> Fortinet Firewall
VPN subnet is enabled in the site to site settings and my layer 3 rules are allow any any for testing.
Solved! Go to solution.
- Labels:
-
3rd Party VPN
-
Client VPN
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This is working now. The issue was on the Fortinet side in case anyone else runs into this issue.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
That's not supported. The only way to get a meraki client vpn to access something available over a third party style tunnel would be to have the third party tunnel in another firewall and if it's a meraki it needs to not be in that org. You then add a static route pointing to that other firewall and are able to advertise that into your Meraki network.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It is supported. We have an existing, working tunnel between our Meraki MX100 and a Fortinet firewall. I need AnyConnect Client VPN to the Meraki to access resources behind the Fortinet tunnel.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I read too fast and read it wrong. My apologies. In this case, is the anyconnect subnet programmed on the fortinet tunnel? It will need to be in phase 2 settings and/or the relevant routes if its a VTI style tunnel. You also have the route in the mx pointing whatever the remote subnet is to the fortinet and have vpn enabled for that, correct?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The AnyConnect subnet is in the encryption domain on the Fortinet.
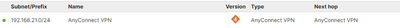
"You also have the route in the mx pointing whatever the remote subnet is to the fortinet and have vpn enabled for that, correct?"
I'm not sure how to confirm the "routing" on the MX as the routing table in the GUI is... interesting?
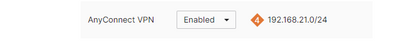
When you say "VPN enabled for that", I assume you mean the AnyConnect subnet? If so, yes:
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Honestly, I think I'm still confused, is the fortinet local to the MX and connected to the same lan as the MX or is the fortinet connection in your 3rd party VPN tunnels on the MX?
If the former then you need a static route in the MX on the addressing and vlans page pointing the relevant remote subnet to the fortinet
if the latter my original comment and @RomanMD 's stand. It is not supported and will not work. A quick call to Meraki support will also confirm this
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The Fortinet is a VPN peer of the Meraki and they are connected via the internet. The tunnel between the Meraki and the Fortinet works fine other than for AnyConnect clients connecting to the Meraki. The Fortinet is a third party tunnel to the Meraki.
There are no configured static routes on the Meraki. I'm not understanding why a static route would be needed for AnyConnect clients but not any of the other VLANs local to the Meraki, which work on the tunnel.
Meraki support tells me this configuration is supported.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You don't need a static route in this scenario, I was talking about a different configuration, not being clear on what yours was.
It has been 100% unsupported for any Meraki client vpn to access items over any third party tunnel for a very long time.
If meraki support is saying otherwise then there is something new I and others are unaware of and I suggest you work with them.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I appreciate the reply. I am working with them and they seem mystified that isn't working. I am 100 percent positive this has worked in the past as I've personally used it, so I'm not sure why it is "unsupported". This worked on this hardware, this tunnel in previous firmware versions.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Now that you said "encryption domain" I recall having a problem, and the problem was the way the subnets were defined in the encryption domain. I had to define the subnets as they were configured, and not supernet them. Maybe you have changed the configuration here...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It is not supported. The first recommendation applies.
For instance, if your MX is participating with other MX in AutoVPN and with Fortinet in IPSec, the devices behind IPsec tunnel can't talk to devices behind AutoVPN tunnel.
What you report here, is very much similar to what I've described, therefore I would assume this is the reason, but I would open a case to confirm it.
This is why I pretty much like to have dedicated hardware for different services....
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Incorrect.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This is working now. The issue was on the Fortinet side in case anyone else runs into this issue.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi, I have the same setup, anyconnect to MX84 - MX84 vpn to "non meraki fortinet firewall"
The "non meraki vpn" works fine, but the anyconnect client to the MX84, cant see resouorces on the fortinet network.
What did you do on the fortinet firewall to make it work?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Could you post here which step is required to check? I have the same issue. We are migrating our old sophos to MX.
-
3rd Party VPN
163 -
ACLs
88 -
Auto VPN
287 -
AWS
35 -
Azure
66 -
Client VPN
367 -
Firewall
832 -
iOS
1 -
Other
539 -
Wireless LAN MR
1