We're migrating to the Cisco Community on March 29. The Meraki Community will enter read-only mode starting on March 26.
Learn more- Technical Forums
- :
- Security & SD-WAN
- :
- Re: Alerting for IDS attacks
Alerting for IDS attacks
Solved- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Alerting for IDS attacks
Good morning,
I was looking around our firewall and noticed a series of IDS attacks being blocked by our MX. I was hoping there was a way to just get alerts when an IDS ruleset was being triggered vs getting an alert anytime malware is blocked. Is there a way to get only this kind of alert?
Thanks.
Solved! Go to solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You generally don't want email alerting for IDS alerts. What happens is it tends to come in waves, and your inbox will get flooded.
+1 to @jdsilva , the Meraki platform can not alert on just IDS alerts. I would be surprised if it was added for the above reason.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I would like to be notified for these events, maybe not all of them but if the MX sees a bunch of events at least let me know its happening.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oh! If all you want is to know that they've happened then that can actually be done. If you go into Organization > Summary reports, select you appliance network at the top under "Networks(s)", and then scroll WAYYYYY down to the bottom right where you will find the section "Top Security Threats by Signature". There you will find all the IDS/IPS rules that have been triggered, and how many times. You can then set up an auto email of this report to yourself on a reoccurring frequency (daily? weekly?).
So not real time alerting by a long shot, but maybe that would work for you?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oh thats an idea! But i do want real time alerting, but i agree i dont want a ton of emails for every event more or less a summary.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
OK, one last possibility and then I'm tapping out on this one 🙂
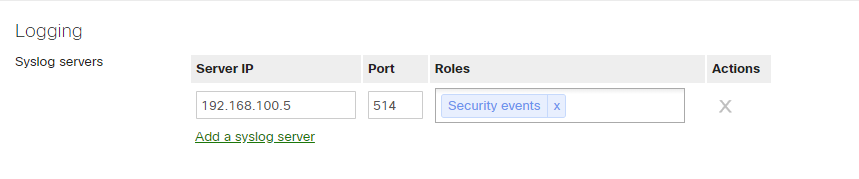
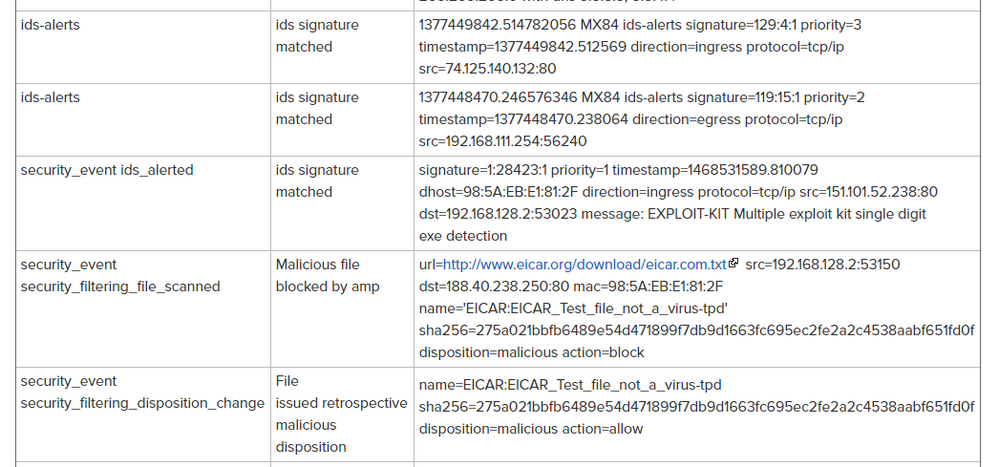
You can also configure Syslog message to send security events:
Judging by the docs, IDS signature messages are included in these (among a few others).
So if you're running a syslog server somewhere (or maybe a SIEM?) you can pipe these messages into that, and then presumably have that send you emails.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Ah! I really should spin up a syslog server.......
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
One solution we have used that has allowed us to customize the log format etc... as they come into our dashboard via grock is ELK. https://www.elastic.co/
My coworker built these configuration files to help with the syslog, netflow parsing.
-
3rd Party VPN
174 -
ACLs
91 -
Auto VPN
305 -
AWS
36 -
Azure
70 -
Client VPN
382 -
Firewall
866 -
iOS
1 -
Other
557 -
Wireless LAN MR
1