Get answers from our community of experts in record time.
Join now- Technical Forums
- :
- Security & SD-WAN
- :
- Re: AMP blocking Microsoft Security Updates
AMP blocking Microsoft Security Updates
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
AMP blocking Microsoft Security Updates
Has any changes been made to Meraki AMP to block some of Microsoft security updates for this month. First time encountering Microsoft security updates being blocked by AMP.
# | Timeslice | action | dest_ip | dest_port | disposition | eventcount | mac | name | sha256 | src_ip | src_port | url |
1 | 07/14/2023 09:31:28 AM EDT | block |
| 80 | malicious | 1 |
| EP_FW01 | ebf3e7290b8fd1e5509caa69335251f22b61baf3f9ff87b4e8544f3c1fea279d | Removed | 53601 | |
2 | 07/14/2023 09:31:23 AM EDT | block |
| 80 | malicious | 1 |
| EP_FW01 | ebf3e7290b8fd1e5509caa69335251f22b61baf3f9ff87b4e8544f3c1fea279d | Removed | 57537 | |
3 | 07/14/2023 09:31:12 AM EDT | block |
| 80 | malicious | 1 |
| EP_FW01 | ebf3e7290b8fd1e5509caa69335251f22b61baf3f9ff87b4e8544f3c1fea279d | Removed | 57508 | |
4 | 07/14/2023 09:29:37 AM EDT | block |
| 80 | malicious | 1 |
| GA_FW01 | ebf3e7290b8fd1e5509caa69335251f22b61baf3f9ff87b4e8544f3c1fea279d | Removed | 49986 | |
5 | 07/14/2023 09:29:23 AM EDT | block |
| 80 | malicious | 1 |
| EP_FW01 | ebf3e7290b8fd1e5509caa69335251f22b61baf3f9ff87b4e8544f3c1fea279d | Removed | 53531 | |
6 | 07/14/2023 09:29:23 AM EDT | block |
| 80 | malicious | 1 |
| EP_FW01 | ebf3e7290b8fd1e5509caa69335251f22b61baf3f9ff87b4e8544f3c1fea279d | Removed | 53532 | |
7 | 07/14/2023 09:29:19 AM EDT | block |
| 80 | malicious | 1 |
| EP_FW01 | ebf3e7290b8fd1e5509caa69335251f22b61baf3f9ff87b4e8544f3c1fea279d | Removed | 58044 | |
8 | 07/14/2023 09:29:18 AM EDT | block |
| 80 | malicious | 1 |
| EP_FW01 | ebf3e7290b8fd1e5509caa69335251f22b61baf3f9ff87b4e8544f3c1fea279d | Removed | 58042 | |
9 | 07/14/2023 09:28:51 AM EDT | block |
| 80 | malicious | 1 |
| EP_FW01 | 9b8db510ef42b8ed54a3712636fda55a4f8cfcd5493e20b74ab00cd4f3979f2d | Removed | 53389 | |
10 | 07/14/2023 09:28:51 AM EDT | block |
| 80 | malicious | 1 |
| EP_FW01 | 9b8db510ef42b8ed54a3712636fda55a4f8cfcd5493e20b74ab00cd4f3979f2d | Removed | 53388 | |
11 | 07/14/2023 09:28:48 AM EDT | block |
| 80 | malicious | 1 |
| EP_FW01 | ebf3e7290b8fd1e5509caa69335251f22b61baf3f9ff87b4e8544f3c1fea279d | Removed | 53375 | |
12 | 07/14/2023 09:28:48 AM EDT | block |
| 80 | malicious | 1 |
| EP_FW01 | ebf3e7290b8fd1e5509caa69335251f22b61baf3f9ff87b4e8544f3c1fea279d | Removed | 53380 | |
13 | 07/14/2023 09:28:47 AM EDT | block |
| 80 | malicious | 1 |
| EP_FW01 | ebf3e7290b8fd1e5509caa69335251f22b61baf3f9ff87b4e8544f3c1fea279d | Removed | 53373 | |
14 | 07/14/2023 09:28:46 AM EDT | block |
| 80 | malicious | 1 |
| EP_FW01 | 9b8db510ef42b8ed54a3712636fda55a4f8cfcd5493e20b74ab00cd4f3979f2d | Removed | 53372 | |
15 | 07/14/2023 09:28:02 AM EDT | block |
| 80 | malicious | 1 |
| EP_FW01 | ebf3e7290b8fd1e5509caa69335251f22b61baf3f9ff87b4e8544f3c1fea279d | Removed | 61485 | |
16 | 07/14/2023 09:28:02 AM EDT | block |
| 80 | malicious | 1 |
| EP_FW01 | ebf3e7290b8fd1e5509caa69335251f22b61baf3f9ff87b4e8544f3c1fea279d | Removed | 61472 | |
17 | 07/14/2023 09:28:01 AM EDT | block |
| 80 | malicious | 1 |
| EP_FW01 | ebf3e7290b8fd1e5509caa69335251f22b61baf3f9ff87b4e8544f3c1fea279d | Removed | 61471 | |
18 | 07/14/2023 09:26:55 AM EDT | block |
| 80 | malicious | 1 |
| EP_FW01 | ebf3e7290b8fd1e5509caa69335251f22b61baf3f9ff87b4e8544f3c1fea279d | Removed | 53468 | |
19 | 07/14/2023 09:26:29 AM EDT | block |
| 80 | malicious | 1 |
| EP_FW01 | ebf3e7290b8fd1e5509caa69335251f22b61baf3f9ff87b4e8544f3c1fea279d | Removed | 51605 | |
20 | 07/14/2023 09:26:22 AM EDT | block |
| 80 | malicious | 1 |
| EP_FW01 | ebf3e7290b8fd1e5509caa69335251f22b61baf3f9ff87b4e8544f3c1fea279d | Removed | 51560 | |
21 | 07/14/2023 09:26:21 AM EDT | block |
| 80 | malicious | 1 |
| EP_FW01 | ebf3e7290b8fd1e5509caa69335251f22b61baf3f9ff87b4e8544f3c1fea279d | Removed | 51554 |
- Labels:
-
Firewall
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
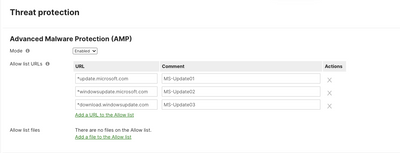
Go ahead and created an allow rule in Security & SD-WAN > Threat Protection for Cisco AMP. I'd also validate that this isn't a proxy and that the traffic comes from a trusted source (MIM). This is not expected for Cisco AMP; I've never seen it happen with the over 250 sites we manage.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi rhamersley
This might be a silly question but how do you find the report you posted? We are having programs blocked and I can't find how to view this.
Cheers
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@Agilico The security report can be found in the portal Organizations > Security Center. Make sure to refine your search based on the MX that is blocking the traffic. You can Download an export to a CSV file as well.
Content filtering blocks are a bit more difficult to track down, I normally use a syslog server or packet capture for more granular details when troubleshooting these events
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@0AK13Y Thanks for this. I have had a look at that report but it only shows snort rule blocks, not URLs like above. I have also tried to download packet captures in Wireshark format for a particular server but it shows no data?! Very confused!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You’re likely selecting the incorrect interface to run a packet capture on. Give support a call, they will be eager to help you out.
-
3rd Party VPN
171 -
ACLs
91 -
Auto VPN
298 -
AWS
36 -
Azure
70 -
Client VPN
381 -
Firewall
851 -
iOS
1 -
Other
549 -
Wireless LAN MR
1