- Technical Forums
- :
- New to Meraki
- :
- High Usage - UDP + P2P - Blocked at layer 7 but staffic still coming throug...
High Usage - UDP + P2P - Blocked at layer 7 but staffic still coming through
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
High Usage - UDP + P2P - Blocked at layer 7 but staffic still coming through
Hi guys, hope you can help.
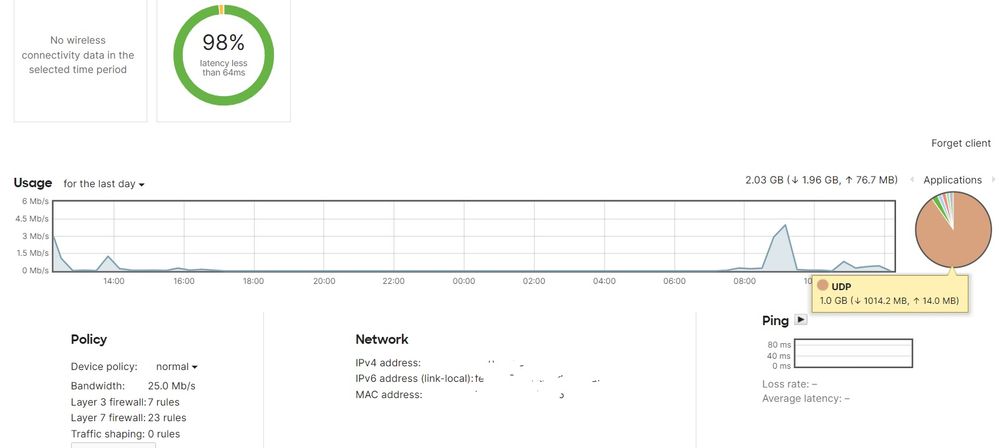
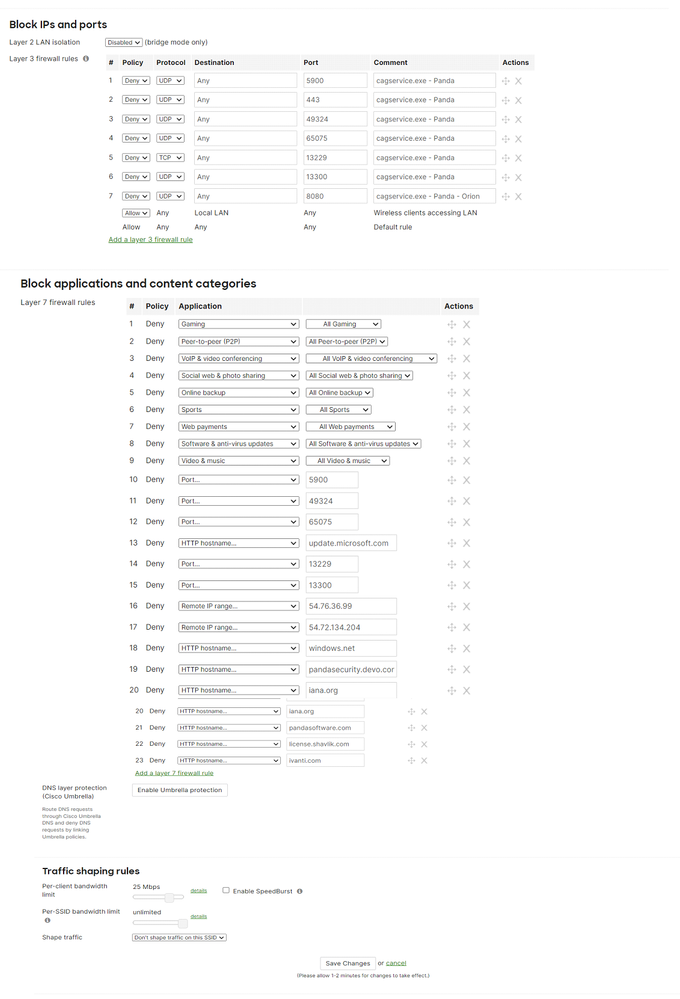
I still have annumber of clients that have high usage on our network for UDP apps and high usage in P2P (random ports)
I have created layer 7 rules and tried to block all P2P applications, but traffic still seems to be getting through.
Can anyone advise me on what im doing wrong here? I mus be doing something stupid. Any help is appreciated guys 🙂
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
File sharing programs, such as BitTorrent, are now able to be configured to encrypt traffic as secure HTTPS, potentially bypassing P2P traffic shaping rules that have been configured. Cisco Meraki MX Security Appliances and Wireless APs are capable of detecting some of the encrypted P2P traffic on the network. When encrypted P2P traffic is detected, it will be matched to any configured P2P traffic shaping rules, and honor the limitations that have been configured. However, if the traffic is encrypted, it may not be possible to accurately classify all of the offending traffic.
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi alemabrahao, thanks for responding. I can also see a lot of usage on application UDP, i have no idea what this is. Is there anyway of finding out exactly what this application is via the meraki dashboard?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
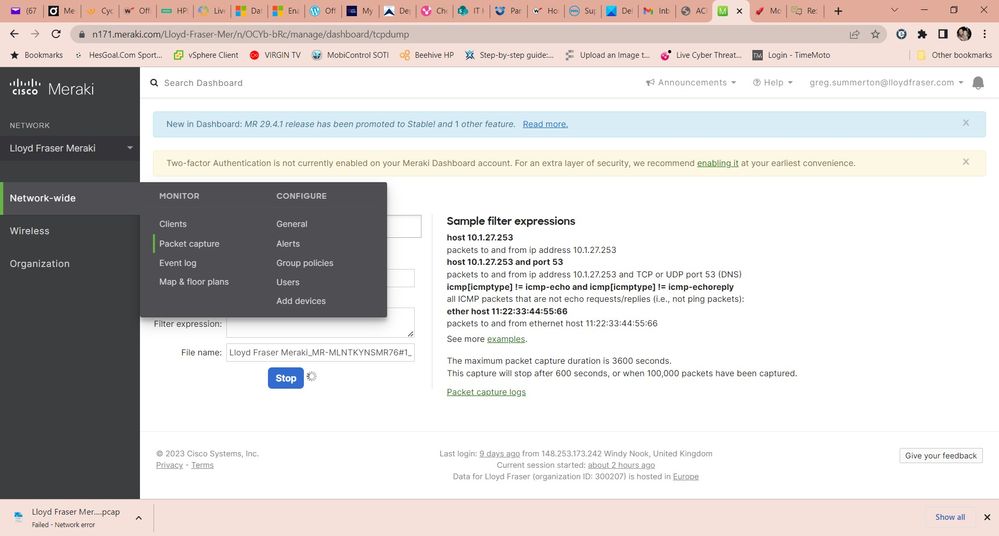
There are a lot of applications that use UDP ports, you can try to perform a packet capture, but it seems to me a relatively small volume of traffic. You can also send the logs to a syslog server, but I think that packet capture is enough.
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
you can also check the Network-wide > Monitor > Traffic analytics
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@WhitwickWindmil you could try turning on traffic analytics to get used port details/ip' like @alemabrahao suggests
https://documentation.meraki.com/MS/Monitoring_and_Reporting/Switch_Traffic_Analytics
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks so much. I've started a packet capture, so hopefully that'll highlight the usage. This AP is running of a 4G sim card, so i need to keep the usage to a minimum as its very expensive once you go over your limit.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks guys, i tried all the things you suggested, reall really helpful. It turns out they were just accessing microsoft services, our warehouse system relies on this and is quite heavy in terms of traffic passing though it, nothing
suspicious to report here 😁