- Technical Forums
- :
- Full-Stack & Network-Wide
- :
- Re: Can Meraki create an isolated network suitable for building/facility sy...
Can Meraki create an isolated network suitable for building/facility systems that may include IoT?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Can Meraki create an isolated network suitable for building/facility systems that may include IoT?
The LAN that our facilities and building systems are currently on was installed years ago and it is physically isolated from our primary data LAN for business. The facility director built it himself and didn't want to have anything to do with the IT department. Now we find ourselves with him retiring and the ISP providing WAN connectivity for that network is terminating their service offerings in our geographical area. I can either:
- Just go with a different ISP for that isolated network (increased cost)
- Somehow incorporate their network into my Meraki stack.
How do I mitigate the security risks of facility systems while incorporating the network into my production data network? Is it a question of routing? Firewall rules? VLANs?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Are you talking about a WAN connection or a LAN connection?
If It's a LAN connection you can isolate the communication using L3 firewall rules.
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
We want to use the same WAN connection as our primary production VLANs, but want the traffic on this facility network to only be able to get in and out to the WAN, much the same behaviour that NAT mode on a Meraki AP isolates the client to only be able to access the Internet.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
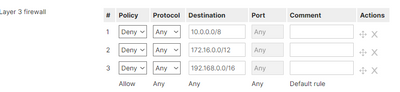
You can create a new VLAN and then create a group policy denying the IP range on RFC 1918 and apply It to the VLAN interface. Some thing like this:
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It's not clear quite what Merki gear you have, but personally I'd recommend the following approach, which matches some of the previous replies:
Having separate physical networks for this kind of thing is a dying approach, I would say and for good reasons, that I won;t go into.
Provision one common reliable, resilient, performant network for all of your traffic, then apply appropriate logical separation and controls (e.g. rate shaping) for the stuff that needs it (that probably includes BMS). While there are other approaches, simply using VLANs and firewalling between them is a relatively simple and well understood and scalable approach. Generally you provide one gateway per site that interconnects the VLANs at Layer-3 and this is where you define the (firewall) rules for what can talk to what. In a Meraki network, you'd probably be best using an MX appliance as that common gateway. It would also provide the necessary protection between your Internet uplink - particularly if you use the Advanced Security license.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
We're full stack Meraki on the production LAN/WAN side of the business.
MX 250 with Advanced Security license is our firewall. Then immediately downstream is our core L3 MS 425 that is where the VLANs are defined. Then everything stars out to our IDFs with MS 390s and MS 125s, and we have MRs of different models and gens.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
OK, so you could continue to use your L3 switching Core and apply Access Control Lists there, for your BMS separation. Is there a particular reason why you route between VLANs on your switches, rather than the MX? There are potential performance advanatages doing that (as it's done in ASIC) - but they tend to only accrue if you have servers located onsite and a decent amount of east-west traffic (particularly between servers in different VLANs). Increasingly servers tend to be away across a WAN link somewhere, where the uplink capacity is the main bottleneck.
https://documentation.meraki.com/MS/Layer_3_Switching/Configuring_ACLs
https://documentation.meraki.com/MS/Other_Topics/Switch_ACL_Operation
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I would wait until he leaves and migrate it onto the exisiting hardware and just isolate using VLANS and ACL's. I run multiple isolated subnets on one of my networks and it works a treat.
I would suggest sitting down and planning the migration to avoid any issues, just makes sure your current hardware will handle the extra traffic. As @GreenMan said its old school thinking and I have come across it plenty of times.