We're migrating to the Cisco Community on March 29. The Meraki Community will enter read-only mode starting on March 26.
Learn more- Technical Forums
- :
- Dashboard & Administration
- :
- Re: Org-level RADIUS Server - Open discussion
Org-level RADIUS Server - Open discussion
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Org-level RADIUS Server - Open discussion
Hi ,
This is an open discussion about the new EA Feature : Org-level RADIUS Server
- Documentation is properly attached . Bonus points !
- Seems to have broken some Access Policy related API. Waiting confirmation on that
- User input validation seems broken
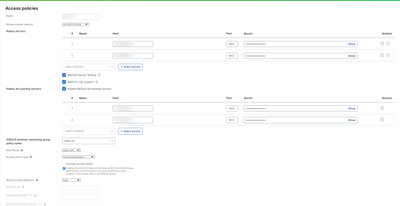
- Existing Access Policy now includes a new UI :
- The mix of 'new' UI and 'old' UI is a bit odd.
- Old Access Policy now display a 'show secret' button. That button is not displaying my current Secret. So I have no idea what it is showing
So here is my initial feedback 🙂
PS : Love the idea and the feature but still dislike the way to inform of bugs / feedback. The "give feedback button" is not event present on that page , and unsure if someone is really looking at that anyway.
Cheers !
- Labels:
-
Administrators
-
Other
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Open question : If you change one or all RADIUS server IPs , should we expect a Org-Wide re-auth on all ports configured with an access policy ?
Eg : I'm migrating my RADIUS from 10.1.1.1 to 10.2.2.2. I do the change Org-Wide. What is the expected behavior ?
My initial thoughts : Nothing happens until there's a re-auth or new auth on the ports using that access policy. Am I right ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Only for Switches??? Ok ... This is a feature I have hoped for since day 1. But wireless would be more important. For your question, I would expect the existing sessions to stay active until reauth or a button "reauth now" is pressed (either on the dashboard or on the RADIUS server).
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes I hope this get ported to MR !
The only reason I'm asking is because editing ports/access policy on MX forces a re-auth of all ports. I was worried a bit about that part but it seems that you are right. I have to do more testing
Edit : And MS too ? https://documentation.meraki.com/MS/Access_Control/MS_Switch_Access_Policies_(802.1X)
As of MS 9.16, changes to an existing access policy will cause a port-bounce on all ports configured for that policy.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
> If you change one or all RADIUS server IPs
Does it result in a re-auth if you change the RADIUS server IP address at the current network level?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Per documentation .. yes
https://documentation.meraki.com/MS/Access_Control/MS_Switch_Access_Policies_(802.1X)
As of MS 9.16, changes to an existing access policy will cause a port-bounce on all ports configured for that policy.
But I have to try it first. That message seems really old. 9.16 , I don't even remember the bugs from that version haha !
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Update from my case : Hi Raphael. The behavior in question is no longer present.
So changing the Radius settings Org-wide ( or network-wide ) shouldn't bounce the configured ports.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
MR will come later
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
+1 for MR please 🙂
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Any update on when?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Is it possible to reference these global RADIUS servers when creating an access policy via API? I'm not seeing a way to use the createNetworkSwitchAccessPolicy operation to link to these global servers.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I'm afraid it is not possible at the moment.
-
Administrators
243 -
Change log
15 -
Firmware upgrades
32 -
Inventory
49 -
Licensing
82 -
Meraki mobile app
13 -
Other
180