Get answers from our community of experts in record time.
Join now- Technical Forums
- :
- Cloud Security & SD-WAN (vMX)
- :
- Re: Can't route to vMX in AWS from the office
Can't route to vMX in AWS from the office
Solved- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Can't route to vMX in AWS from the office
Scenario:
I got one MX68 in the office and 2 vMX in AWS cloud in different regions. There are servers in each region that I'm trying to connect to. All devices are in routed mode.
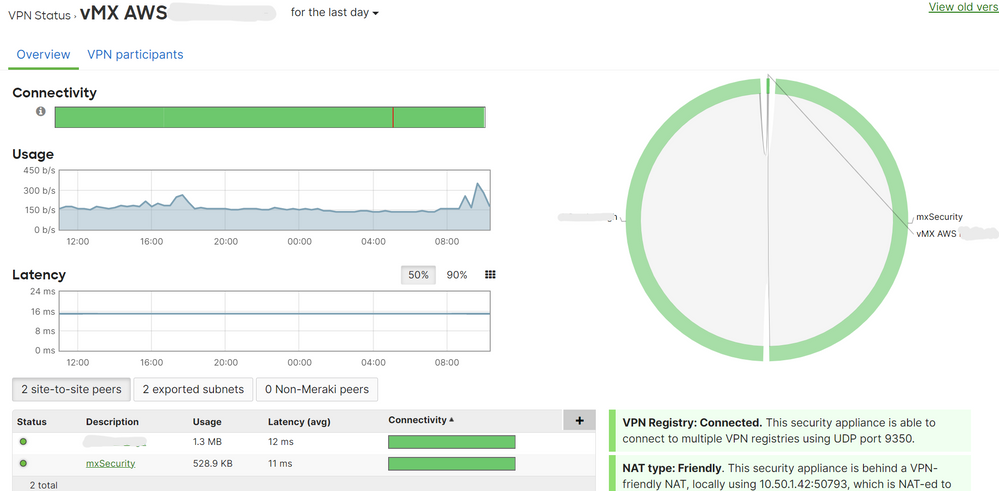
Devices connect via VPN without any issues.
Problem:
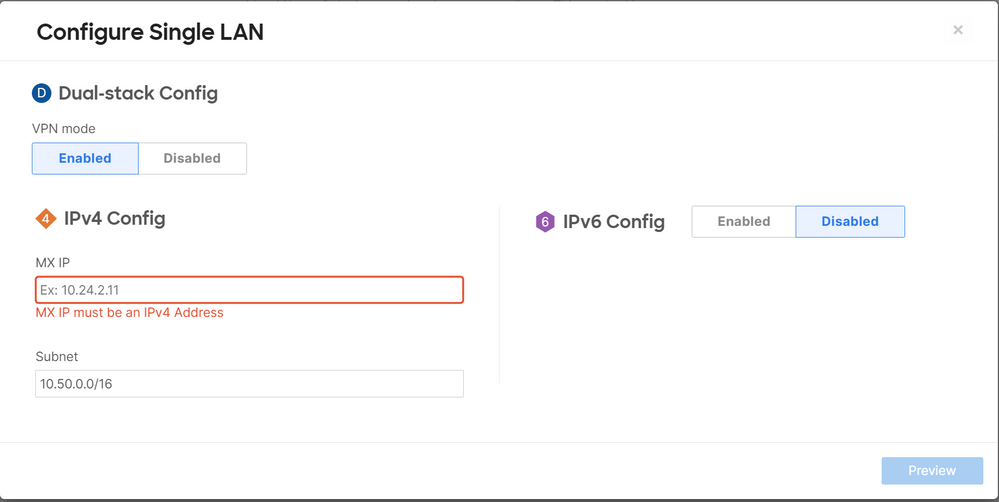
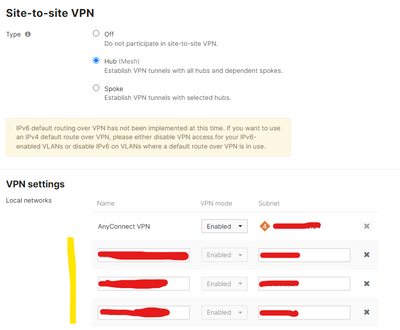
One arm configuration of vMX has me assigning IP address outside of the AWS subnet. This works for AnyConnect VPN and users can dial in to either vMX and authenticate via AD (routing to servers works). Issue now is that the site office is sending any traffic to the servers via internet, instead of VPN. When trying to add route, it complaints that there's no subnet defined and simply refuses.
How to go about it?
for better visualisation:
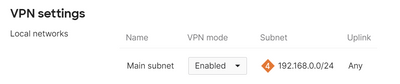
MX68 (office): 192.168.0.0/24 (device 192.168.0.1)
vMX region1: 10.0.0.0/16 (device AWS assigned IP: 10.0.12.143)
vMX region2: 10.50.0.0/16 (deice AWS assigned IP: 10.50.1.42
I've tried to set the Meraki IP in Addressing & VLAN to the same IP as AWS assigned but it wasn't routing to my AD for authentication.
I've set it to outside of any AWS subnet which works for AD authentication and client VPN but then running into issues described above - office traffic routes via internet
I've set the Meraki IP within AWS subnet but different IP that's not AWS assigned to 10.0.12.144. It wasn;t routing correctly and I got no responses and no VPN users authenticated via AD
thanks
Solved! Go to solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
thanks for assistance all. The issue was that there was no vMX template in a second region so we used AWS site-to-site VPN and VPC peering to get the connectivity going at the beginning. This has interfered with Meraki's routing and was the cause of the issues.
After removing all site-to-site VPNs and VPC peering I've changed all the routing back to respective vMXs and it all started to flow beautifully.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Are you sure that you have a site to site VPN with AWS?
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I don't believe I said that.. I have mesh VPN between all Meraki devices.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Great, Will I configure the vMX so that the networks participate in the VPN?
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
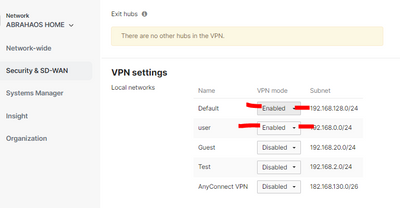
I did not and when I enquired with support (ticket still opened) they said it's not necessary. VPN connectivity seems fine.. I understood that as a single exit which we don't want. Not all traffic is routed via VPN, only VPN traffic (split tunnel)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes it is, otherwise you won't have the routes to the destination networks in your office's MX routing table. I think that was a misguided response on their part.
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
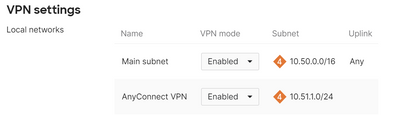
What I'm trying to say is that you don't need to configure any interface or route on your office's MX, Just configure vMX region1: 10.0.0.0/16 and vMX region2: 10.50.0.0/16 networks to participate on auto VPN and the routes will be added automatically on your office's MX.
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Meraki says that I do need it.. if you have vMX, what did you put in? Same IP as the device, different but same AWS subnet or something outside of your AWS subnet?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Just configure vMX region1: 10.0.0.0/16 and vMX region2: 10.50.0.0/16 networks to participate on auto VPN and the routes will be added automatically on your office's MX. You don't need any additional configuration, buddy.
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
But the system won't let me accept no entry or empty entry - I need to have value. Can you post screenshot from your setup? Seems unlikely that you were able to do it...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Go to Security & SD-WAN > Configure > Site-to-site VPN and enable that.
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I have that enabled.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
And how about your MX68 network 192.168.0.0/24?
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
also enabled
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
So, there is not any additional configuration. Are you trying to access your devices on AWS by IP or by name?
If you perform a traceroute what is the result?
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
by IP. As mentioned above, when I have the Meraki IP set as the device, it doesn't NAT out due to one-arm configutration. If I set it to outside of AWS subnet, it routes correctly for the client VPN users but my office device only sends to that subnet, which is outside of 10.50.0.0/16 and 10.0.0.0/16 respectively. So this is what I'm trying to square primarily...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Here you can check how to troubleshoot it:
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
And you have to do the same for your MX68 network 192.168.0.0/24, just enable on auto VPN.
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
For a VMX, you need to add the routes (10.0.0.0/16 and 10.50.0.0/16) under:
Security & SD-WAN/Site-to-site VPN/VPN Settings/Local networks
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It's already defined correctly there...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
thanks for assistance all. The issue was that there was no vMX template in a second region so we used AWS site-to-site VPN and VPC peering to get the connectivity going at the beginning. This has interfered with Meraki's routing and was the cause of the issues.
After removing all site-to-site VPNs and VPC peering I've changed all the routing back to respective vMXs and it all started to flow beautifully.
-
3rd Party VPN
1 -
Auto VPN
26 -
AWS
17 -
Azure
57 -
Client VPN
6 -
Cloud native firewall
2 -
Cloud networking
26 -
Firewall
5 -
Hybrid Cloud
6 -
Multi Cloud
3 -
Multi Region Cloud
4 -
Other
7 -
Quick Start
1 -
Virtual firewall
30