Get answers from our community of experts in record time.
Join now- Technical Forums
- :
- Cloud Security & SD-WAN (vMX)
- :
- Re: Azure vMX 100 - Unable to ping vmx100 in Azure when connected to Client...
Azure vMX 100 - Unable to ping vmx100 in Azure when connected to Client VPN
Solved- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Azure vMX 100 - Unable to ping vmx100 in Azure when connected to Client VPN
Hello All!
Thank you for taking the time to read this. I am having an issue with once connected to vMX in Azure using the Client VPN - I cannot get a ping response to the vMX100 in Azure
First off - I have searched the entire breadth of the internet to try spot if I am missing something, but I just cannot find it - I also have a case open with Meraki which has been open for sometime without resolution. Therefore, I would be extremely grateful for any ideas / guidance.
------------------------------------------------------------------------------------------------
- I have deployed a VMX100 into Azure using the CSP work around. - Shows online with Public IP in Meraki Dashboard.
- My vMX100 has its own dedicated VNET (Meraki-LAN) and Subnet dedicated to the vMX100
- My Servers have their own VNET (Server-LAN) and Subnet (Peeing between the vMX VNET and my Server VNET With IP Forwarded Traffic on the Peering from meraki to Servers VNET)
- I have enabled Client VPN in the Meraki Dashboard.
- Azure VMX100: - VNET = 10.140.1.0/24 || Subnet = 10.140.1.0/24 (vMX gets IP of: 10.140.1.4)
- Meraki Dashboard Client VPN - 10.140.2.0/24
- Servers: - VNET = 10.140.8.0/21 || Subnet = 10.140.8.0/24
-----------------------------------------------------------------------------------------------
Once the above was setup (Before I added any route table anywhere) I thought a good first test would be to
- Connect to the vMX100 using the Client VPN and Ping the vMX100's Local IP.
I used Meraki Authentication, and connect to the VPN, it prompts me for username and password, and it then connects - I get a IP that I would expect. 10.140.2.86 - However, When I try to ping the Meraki (10.140.1.4) I do not get a response.
I cannot work out why or how to resolve this. 😞
I also enabled Split Tunnelling (Just un-ticking a box in the IPV4 Advance settings on thje VPN NIC) (Windows 10)
------------------------------------------------------------------------------------------------
I guess after I have successfully got the device to ping with my local device I can then deploy a Route Table with the Client VPN route and the Servers Subnet in the table. Until then I am just trying to get the first part to work.
Many thanks
Adam
Solved! Go to solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I have resolved this issue.
Inside of Azure, I deployed the Meraki vMX100 to a VNET 10.140.1.0/24 with a SUBNET of the same (10.140.1.0/24)
My client VPN on the Meraki Dashboard for the vMX100 is 10.140.2.0/24
With this config, I could ping my device from a server in azure, but I could not ping the server in azure from my device connected to the VPN
Therefore, in Azure, under the same VNET i created , I added an additional Address Space (it give you the option under the VNET Address space to do this) of my client VPN 10.140.2.0/24
And straight away I could ping both way. Hooray! 🙂
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
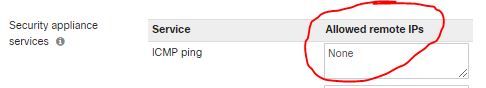
Can you ping 'past' the MX ?
Not familiar with the vMX, but juuuuuuuuust in case its something this simple.
Firewalls don't usually let you ping them, so in case that is the issue.
Check this? Maybe try adding the 10.140.2.0/24 into this list and try again.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I think that should work. What ports are you allowing through to the vMX? I would allow:
UDP/500
UDP/4500
IP protocol 50 (ESP)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@PhilipDAth- I currently have "allow everything" both way on the vMX
once connected to the VPN - the vMX also cannot ping me on the Client VPN IP i get, from when I defined. 10.140.2.0/24
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I have resolved this issue.
Inside of Azure, I deployed the Meraki vMX100 to a VNET 10.140.1.0/24 with a SUBNET of the same (10.140.1.0/24)
My client VPN on the Meraki Dashboard for the vMX100 is 10.140.2.0/24
With this config, I could ping my device from a server in azure, but I could not ping the server in azure from my device connected to the VPN
Therefore, in Azure, under the same VNET i created , I added an additional Address Space (it give you the option under the VNET Address space to do this) of my client VPN 10.140.2.0/24
And straight away I could ping both way. Hooray! 🙂
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I am following your Steps and still cannot Ping MX, do you have NSG on the public NIC on the MX?
Any more info would be appreciated. I really thought this was the answer and did as you described. putting my client VPN in same Subnet with my /16 Network. Then added it to the routing table and Association.
I got local resources working but still cannot ping MX or 8.8.8.8
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Did you get anywhere with this ?
I am in the same boat as you but I can ping 8.8.8.8 with split tunnelling on
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I am having trouble with this
I didnt need to add address space as I had it contained already
Address space 10.101.0.0/16
Client VPN 10.101.3.0/24
Did you have to add Client VPN as a VNET Subnet too? Thats not working for me either but just wondered
and How did the 'local networks' bit look on your Meraki
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
you just need a routing table that points back to the Meraki so that traffic knows where to go. I can confirm while on the client VPN i can ping the vMX in Azure. I have Routing table that points any subnet I want to be able to reach azure resources pointing back to the MX Hope that helps.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Its not like a nomral MX, its like a VPN concentrator more then a firewall, it doesnt have the ICMP service option. - But I beleive from reading posts around the net, you should be able to receive ping response.
I also cannot ping past the vMX100 device to my Servers.
However:
1 - I can ping from the vMX100 to the Servers in Azure Server Subnet (perring working)
2 - I can ping from the Servers in Azure Server Subnet back to the vMX100 (peering the other way working)
3 - I cannot ping from the vMX to my device when I am connected to the VPN (and vice versa ofcourse)
When I am connected to the VPN - I don't get a default gateway (Hence why I guess you need to enable split tunnel on the vpn nic) (
'Azure VPN Nic' and 'home wifi nic' below:)
---
PPP adapter Azure-Meraki:
Connection-specific DNS Suffix . :
IPv4 Address. . . . . . . . . . . : 10.140.2.185
Subnet Mask . . . . . . . . . . . : 255.255.255.255
Default Gateway . . . . . . . . . :
Wireless LAN adapter Wi-Fi:
Connection-specific DNS Suffix . : home
IPv4 Address. . . . . . . . . . . : 192.168.1.202
Subnet Mask . . . . . . . . . . . : 255.255.255.0
Default Gateway . . . . . . . . . : 192.168.1.254
---
-
3rd Party VPN
1 -
Auto VPN
26 -
AWS
17 -
Azure
57 -
Client VPN
6 -
Cloud native firewall
2 -
Cloud networking
26 -
Firewall
5 -
Hybrid Cloud
6 -
Multi Cloud
3 -
Multi Region Cloud
4 -
Other
7 -
Quick Start
1 -
Virtual firewall
30