Get answers from our community of experts in record time.
Join now- Technical Forums
- :
- Wireless
- :
- Re: Routing wireless clients to a private VLAN
Routing wireless clients to a private VLAN
Solved- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Routing wireless clients to a private VLAN
We are looking at implementing the following environment:
MX68 Appliance
3 MS120-48LP switches
12 MR36 APs
We have 40 private VLANs set for wired clients. (Its a shared office environment with 40 individual tenants all with their own private VLAN.) Is there a way to allow these clients the ability to access their own private VLAN(s) wirelessly while roaming between multiple APs if they are moving around the building?
In short:
Client one's network has a private VLAN (we'll say VLAN1) on the wired connection in the office, but they want to be able to access that private VLAN from any AP while connected wirelessly.
In our scenario there are 39 more clients with a private VLAN, all like Client one, that want to access their own private VLAN via wireless.
Can this be configured on the equipment listed above? Maybe through Group Policy? I see how to set a VLAN per SSID, or tag multiple VLANs to a SSID, but not sure how to allow the client to access them individually.
Thanks in advance!
Solved! Go to solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Perhaps use IPSK. You could define per client Group Policies which map the SSID to their private VLAN. Then on the common SSID use IPSK so each client has a unique non-shared/known PSK preventing them from accessing another users VLAN.
Assuming the 40 VLANs exist on the MX you'd also want firewall rules there to prevent VLAN to VLAN communications.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
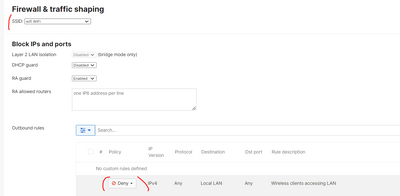
Under Wireless > Configure > Firewall & Traffic shaping change on SSID the rule to allow to clients be able to access LAN.
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks. I can get them to access the LAN, but I need the ability to have them access their private VLAN (each user has a different VLAN on their wired connections to their offices) via wireless.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Perhaps use IPSK. You could define per client Group Policies which map the SSID to their private VLAN. Then on the common SSID use IPSK so each client has a unique non-shared/known PSK preventing them from accessing another users VLAN.
Assuming the 40 VLANs exist on the MX you'd also want firewall rules there to prevent VLAN to VLAN communications.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks! I think this may be the answer I am looking for. Let me research a bit on it to make sure, but this looks like a great start!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I got it, in my opinion it's the best option:
But the options that @Ryan_Miles suggested you is good to.
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Splash Access (a paid option) also has a brilliant "multi-dwelling" system. It has a portal where clients can on-board their own WiFi devices, and it drops their devices into their own private VLAN automatically.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
True. Splash Access is a great solution but a little overkill for this particular project.