Get answers from our community of experts in record time.
Join now- Technical Forums
- :
- Wireless
- :
- Meraki wireless VLAN assignment options
Meraki wireless VLAN assignment options
Solved- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Meraki wireless VLAN assignment options
Hi there,
I have a challenge I am sure someone here can help with! I have a customer with about 50 multi-tenanted sites. Each site can have between 20-30 tenant groups and so this becomes a problem with the 15 SSID limit in Meraki.
One idea I have to get around this limit is to publish one SSID for all tenants and then assign them into VLANs based on tenant identity. This may be one shared identity between all tenants in one tenant group and then using a RADIUS-based solution ( such as ISE, Packetfence, MS NPS) to assign the tenant users into their correct VLAN.
There are a few constraints though. The solution must be easy to manage as the customer does not have a large technical staff and might rely on non-technical staff to provision new tenants.
The other is that customers will need to be set up in a new directory scheme, so there is no LDAP or AD to integrate with, unless we set up new users on there.
We also need to deploy the authentication solution either in the cloud, for example Azure or the main HQ site, which will be connected via VPN.
Then we ideally need to have a default fallback position if the local site cannot talk to the authentication solution, for example if the VPN goes down.
I hope this makes sense and apologies it this is a bit of a ramble! Thanks in advance for all replies.
Solved! Go to solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Definately use a single SSID.
Using more than about 4 SSIDs is not good. The beacons use up a lot of the air time substantially reducing what is left for sending actual data. This results in bad throughput.
If you don't mind setting up each client in the Meraki Dashboard once, you can use a group policy (one per client) and and a VLAN tag.
https://documentation.meraki.com/MR/Client_Addressing_and_Bridging/VLAN_Tagging
You can also use RADIUS to dynamically assign a group policy using the Filter-Id attribute.
There are seperate third party solutions that do this like Splash Access.
https://www.splashaccess.com/co-working-office/
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Definately use a single SSID.
Using more than about 4 SSIDs is not good. The beacons use up a lot of the air time substantially reducing what is left for sending actual data. This results in bad throughput.
If you don't mind setting up each client in the Meraki Dashboard once, you can use a group policy (one per client) and and a VLAN tag.
https://documentation.meraki.com/MR/Client_Addressing_and_Bridging/VLAN_Tagging
You can also use RADIUS to dynamically assign a group policy using the Filter-Id attribute.
There are seperate third party solutions that do this like Splash Access.
https://www.splashaccess.com/co-working-office/
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Many thanks for your reply, this is the confirmation I needed. Although the first two options you mentioned will work for us I have looked at Splash Access and it seems like a better fit for this requirement. Has anyone here any experience with it?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I haven't used this specific service of Splash Access, but I have many customers using some of their other services (their Retail guest WiFi servcies are really good).
They are amazing to deal with I I happily recommend them.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Many thanks for the confirmation about Splash Access, I will get a trial in place.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Agreed, that a network supporting all speeds will be beholden to these restrictions. Meraki documentation expands on some of the considerations: https://documentation.meraki.com/MR/WiFi_Basics_and_Best_Practices/Multi-SSID_Deployment_Considerati...
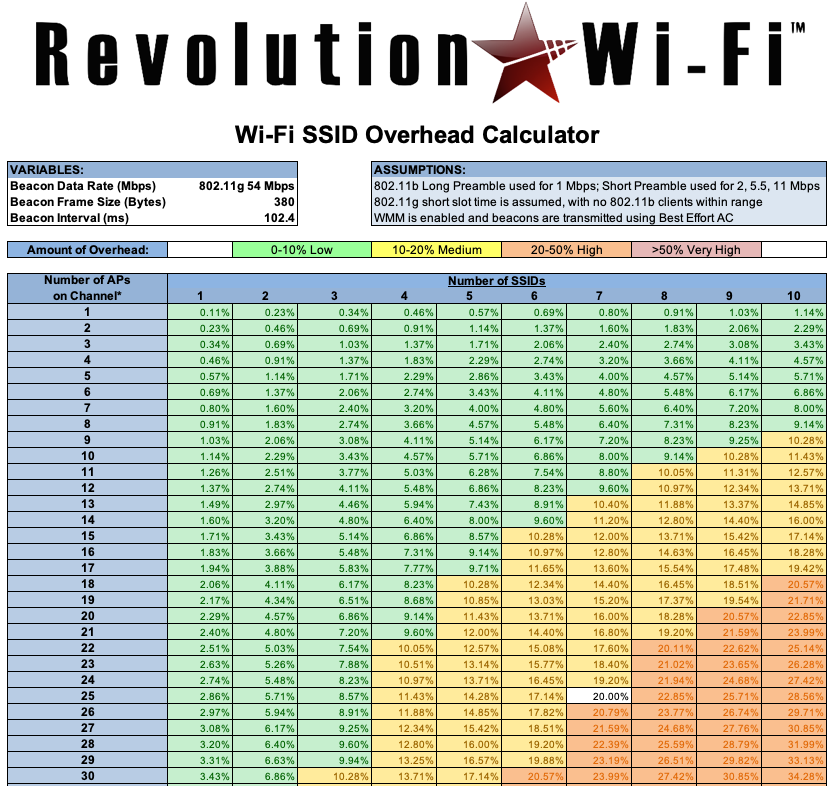
A minor point of clarification to the general rule of thumb: the formula depends on multiple variables:
- The number of SSIDs
- The number of APs on that channel (each SSID on that channel counts as an AP)
- The beacon data rate
If you are inclined to engineer a little further, adjusting any of the three can provide relief for the other two. Eliminating support for 802.11b data rates can free up a significant amount of RF duty cycle on that channel. The table on the website below paints a grim picture, but please note that it references 802.11b 1Mbps data rates. Downloading the spreadsheet and changing it to 802.11g 12 Mbps yields a radically different result.
http://www.revolutionwifi.net/revolutionwifi/p/ssid-overhead-calculator.html
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
>The number of APs on that channel
And to build on @Jon_Hartman 's excellent answer, these don't even have to be your APs. They can be APs from other nearby offices.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This is good information, thanks!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Do know what's the RADIUS attribute (RADIUS VSA Name/
Attribute Type) and vendor ID for Meraki MR as RADIUS client (authenticator )?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@AhmedK wrote:
Hi Philip!
Do know what's the RADIUS attribute (RADIUS VSA Name/
Attribute Type) and vendor ID for Meraki MR as RADIUS client (authenticator )?
No sorry. Never needed to use these fields in a RADIUS server. I only ever use the standard RADIUS attributes.