- Technical Forums
- :
- Wireless
- :
- Re: MAC-Based Access Control and external captive portal
MAC-Based Access Control and external captive portal
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
MAC-Based Access Control and external captive portal
Hello everyone,
First post here. Take it easy on me 🙂
We have developed an integration with Meraki to display our own external captive portal which works great. We are now working on a seamless auth scenario.
User connects to SSID A, gets the splash page, processes splash page. Session is created (ie. 3 months)
User comes back 1 week later, connects to SSID A, seamless auth occurs and user is granted internet without having to process splash page.
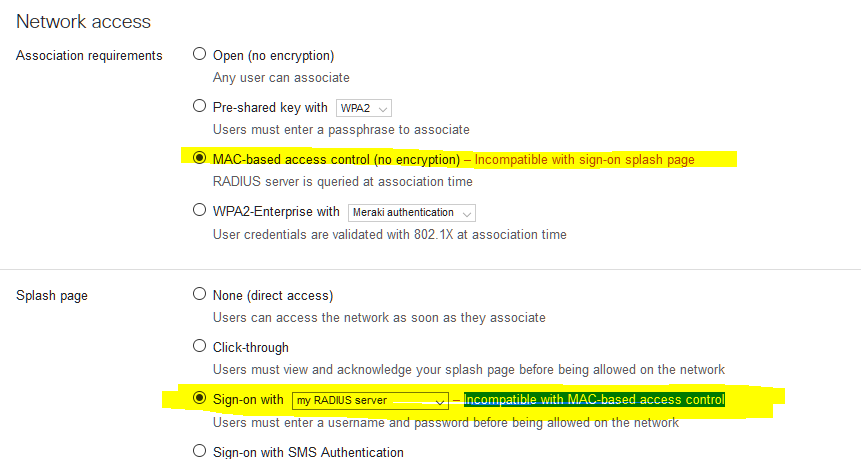
Now we have a working POC but what irks me is the following in the screenshot attached. It throws up an error but allows us to save and our POC works....Any idea why we "can't" do this?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I'm guessing here, but I think the association and authentication steps are limited to a single radius configuration (you can have several radius servers). MAC-based access control uses radius. Splash page sign-on uses radius. As a result, I don't think they can be used together.
If you're already using "Sign-on with (my radius server)" with a custom splash page and you need MAC-based access control, you should be able to validate the MAC address on the same back-end handling your splash page.
Oh well, it should be that easy, but it isn't. Sign-on splash uses a different URL than click-through splash (see https://meraki.cisco.com/lib/pdf/meraki_whitepaper_captive_portal.pdf). Sign-on splash doesn't appear to include the client MAC address in the URL.
But all hope is not lost. I haven't tried this myself, but it should work...
After the user completes the sign-on process, the Meraki AP sends a radius request to your server to confirm the credentials. This radius request SHOULD include the client MAC address. If I remember correctly, it's in the calling station id and the value is ALL CAPS, separated by dashes, followed by a colon, and followed by the SSID. Depending on your radius setup, you may be able to do the MAC filtering at this point.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
We need to intercept it prior so wondering why it allows me to save but throws up an error.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello pmonardo.
Where you able to work this out?
Are you using Freeradius?
We are looking for the same solution.
Greetings!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
We simply went ahead with the warning message.
MAC-based access control (no encryption) and Sign-on with (using My Radius Server).
In our case, we are leveraging the same radius server for MAC-auth and the Splash page.
We also send back the following radius VSA (Aruba-User-Role) since we cannot specify a NAS ID in our radius configuration (since we are not using WPA2-Enterprise and this is an Open network).
We use group policies with the names being the ones returned by our radius server in Aruba-User-Role.
The first group being the same as the SSID configuration with the splash page, etc.
The second group simply bypassing the splash page.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The Meraki Dashboard let's you use MAC-based access and Sign On. That we have configured.
But what about your Radius Server Settings.
How does your Radius show the Captive Portal to Uknown Mac Addresses.
Basically the Radius won't give access to an unknown MAC, do you add the MAC address manually to the Accounting Database or how are you working this out?
We want to give "access" to all known and unknown mac addresses, but unknown mac addresses will be shown the splash portal and known MAC's will bypass the splash portal.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You can create a group policy that bypasses the splash page.
You would then use MAC-based authentication and have your radius server set that group policy for known MAC addresses. For everyone else, the radius server would grant access without setting the group policy.
Unknown MAC addresses would then see the splash page.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@HodyCrouch wrote:You can create a group policy that bypasses the splash page.
You would then use MAC-based authentication and have your radius server set that group policy for known MAC addresses. For everyone else, the radius server would grant access without setting the group policy.
Unknown MAC addresses would then see the splash page.
Exactly like HodyCrouch said. I thought I mentioned it above?
Basically the radius server allows ALL MAC AUTH to occur
Group policies like so (see attached).
You must build the logic in your radius server and splash page server.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Many Thanks Pmonardo and HodyCrouch.
I configured the Access Control Settings as you told me and we made some changes on the Radius to allow all Mac Users and it is working.
Where you able to enable Radius Accounting?
When I click save, it goes backed to disabled
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I am not sure if this video will help to show different authentication methods.
https://www.youtube.com/watch?v=TQNgh5m5ehU
Let me know if that helps