We're migrating to the Cisco Community on March 29. The Meraki Community will enter read-only mode starting on March 26.
Learn more- Technical Forums
- :
- Switching
- :
- VLAN, IPSec tunnelling and routing
VLAN, IPSec tunnelling and routing
Solved- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
VLAN, IPSec tunnelling and routing
Hello,
We have the following configuration:
1. MX84 - router (LAN1 port to WAN uplink)
2. MS120-24p Switch (connected to LAN3 port on the router)
We have 2 VLANs on the security appliance.
1. VLAN1 (default): 192.168.128.0/24
2. VLAN2 : 192.168.33.0/24
LAN3 port is configured as trunk with native VLAN1 but allowing all VLANs
One of the ports on the switch is configured to work on VLAN2 with following properties:
Type: Access
VLAN: 2
Link: auto
Trusted: Disabled
When I connect a device to this switch port it gets the anticipated IP address and I am able to reach public internet.
Now we have Non Meraki VPN Peer configured with AWS IPSec policy with availability to all networks. The subnet we want routed through this tunnel is VLAN2 (192.168.33.0/24)
But we can't seem to reach the remote destination IP from either of the VLANs. I don't see the routes under `netstat -r` either.
How do I go about de-bugging this and is the configuration correct if we want to be able to reach the remote server over the tunnel from VLAN2.
Solved! Go to solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Have you configured your AWS Security Group to allow the traffic from your VLANs?
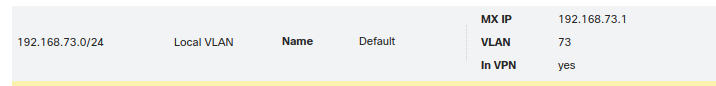
Have you definitely selected to include the subnet in the VPN on the MX (under Security Appliance/Addressing and VLANs)?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Have you configured your AWS Security Group to allow the traffic from your VLANs?
Have you definitely selected to include the subnet in the VPN on the MX (under Security Appliance/Addressing and VLANs)?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Philip,
I hadn't configured it to be in VPN. I've done that, but nothing changed on testing side. I was however able to see connectivity green light on the appliance's routing table against the tunnel route
The remote server belongs to a third party so we're working with them to monitor the network logs. Having said that, are there any other things I could check on our end?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Okay so we were given the incorrect remote IPSec subnet. We solved it once we got the right subnet.
Now is there a way to access this remote subnet from a subnet on our end that is not being forwarded through the tunnel?
Would it be possible to initiate traffic from say a host on 192.168.89.8 (Client VPN subnet)--> 192.0.2.1
to remote IPSec subnet but via the forwarded subnet 192.168.33.0/24?
Just curious how that would work, if it would work.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
If the remote end wont add it your client VPN subnet - so you really do want to access the remote end of the VPN from a subnet of yours not being forwarded via the VPN - then you'll need to use something like a proxy or a jump host.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Got it, thanks!