We're migrating to the Cisco Community on March 29. The Meraki Community will enter read-only mode starting on March 26.
Learn more- Technical Forums
- :
- Switching
- :
- Re: SecurePort (formerly known as SecureConnect) - More or less secure?
SecurePort (formerly known as SecureConnect) - More or less secure?
Solved- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
SecurePort (formerly known as SecureConnect) - More or less secure?
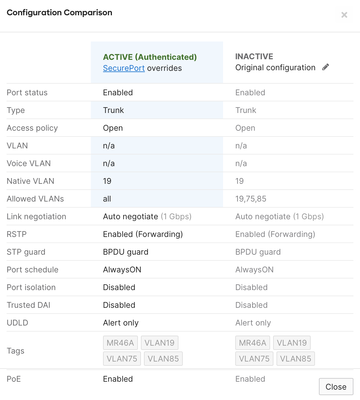
I've read through the SecurePort docs and feel with ALLOWED VLANs to ALL after enabling the SecurePort configuration...it's less secure than if pruning the VLANs to which you are serving (example below being VLANs 19-Management, 75-staff, 85-guests). I get the certificate part....from the perspective of wanting to separate wireless and wired devices.
Is there additional broadcast if ALL VLANs are allowed?
Solved! Go to solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
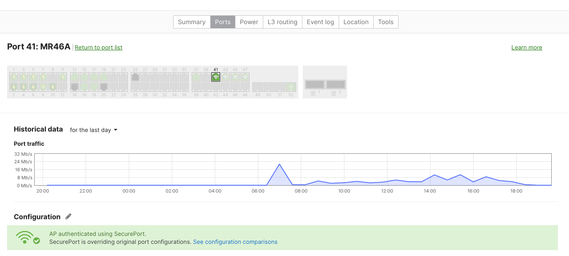
When a switch has SecurePort enabled, only Access Points that belong to the same organization, will be authenticated on the port, and the switchport will get the SecurePort configuration.
This ensures that no one can unplug your access point, and insert their own malicious access point, where traffic may be tunnelled back to some bad actor.
You can set the original switchport settings to some closed vlan, to allow minimal access. Once an AP is connected, it will get a restricted network access to allow it to contact the Meraki Cloud.
Like what you see? - Give a Kudo ## Did it answer your question? - Mark it as a Solution 🙂
All code examples are provided as is. Responsibility for Code execution lies solely your own.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
When a switch has SecurePort enabled, only Access Points that belong to the same organization, will be authenticated on the port, and the switchport will get the SecurePort configuration.
This ensures that no one can unplug your access point, and insert their own malicious access point, where traffic may be tunnelled back to some bad actor.
You can set the original switchport settings to some closed vlan, to allow minimal access. Once an AP is connected, it will get a restricted network access to allow it to contact the Meraki Cloud.
Like what you see? - Give a Kudo ## Did it answer your question? - Mark it as a Solution 🙂
All code examples are provided as is. Responsibility for Code execution lies solely your own.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It is recommended to always prune unused VLANs, this reduces the amount of unnecessary traffic and bandwidth consumption on the trunk link, as well as the security risks of exposing VLANs to unauthorized devices.
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
From a performance perspective, yes in theory it's better to prune, but in practice, just allow all and avoid the management overhead.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@Bucket Well said....thank you. I concur and appreciate the input/feedback.